Trust Wallet Scam Text
This article explains the Trust Wallet KYC Scam Text sent through bogus emails and how to remove it.
Online frauds are more common than ever and due to technological advancements this isn’t going to change soon. One such recent fraud is targeting users of the Trust Wallet service, asking them to verify their KYC by replying to a bogus email.
Do you remember receiving an email from Trust Wallet requesting that you complete your KYC online recently? If yes, you should know that scammers have been detected using a bogus email that circulates the web to trick online users into verifying their wallet and doing an online KYC.
According to reports, users of the Trust Wallet have received a series of emails pushing them to complete the online Know Your Customer verification process. However, although such a verification process does exist and is a common verification method used by many financial platforms, security researchers are nothing that this recent case is an effort to obtain financial information from customers, thus, it should be treated with great care and should be avoided as a fraud.
What is Trust Wallet KYC?
Trust Wallet is a popular online payment platform owned by Binance, that is considered one of the safest online platforms for Cryptocurrencies. This wallet is used by many users to store, transfer, and receive crypto. However, news of a Trust Wallet fraud have recently pushed the name of the service to the top of the search results.
It seems that the end goal of this fraud is to get access to Trust Wallet users’ accounts. An email asking for a KYC verification is used in this fraud, trying to trick the recipients into filling in sensitive details. In no time, the wallet fraud started making headlines in the tech world, as many users reported that their Trust Wallet accounts have been compromised. Many Australians have fallen victim to the Trust Wallet KYC Scam since Trust Wallet is a popular service in Australia.
What is the Trust wallet scam text?
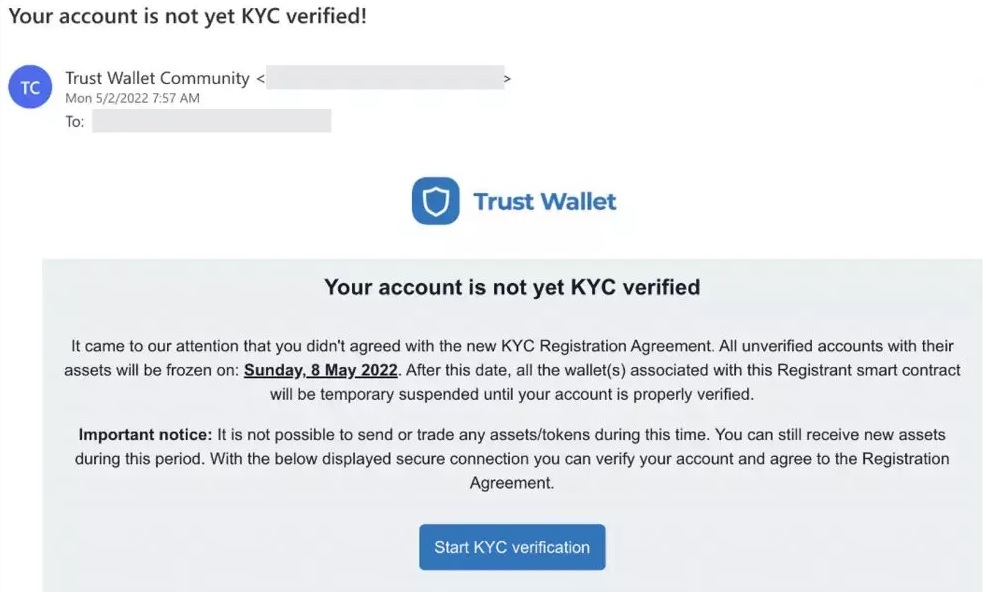
The Trust Wallet Scam Text begins with a well-crafted email requesting the Trust Wallet user to confirm their personal information and prompting them to do a KYC on their trust wallet account. The Trust Wallet scam text in some of the emails includes a button that says “Click here to verify your email“, while in other fraudulent emails there is a direct link included.
Users of trust wallets may be easily tricked into entering their password when they get this email and are prompted to do so by the website they land on after clicking on the link included in the email. Once a user inputs their Trust account login details, they will no longer be able to access their account or their cryptocurrencies.
Trust Wallet Scam Text
Many Australians have received email messages stating that to keep using the wallet, they need to update their KYC. However, security researchers are warning that this is a rip-off.
Fraudulent email messages have been sent to people from an email ID that seems to be legitimate. “Your wallet account is not KYC verified”, states an email sent from “[email protected]”, according to reports.
Customers have been urged through a text message to complete online verification in order to continue using the services. According to the text, the account will then be KYC-verified after the verification process is complete.
What is the Trust Wallet KYC Scam?
KYC or “Know Your Customer” verification is a new verification method and a common rule for many financial platforms. Considering that Trust Wallet is an online financial wallet, users are questioning whether they would need to complete a “Know Your Customer” authentication. So, does Trust Wallet require a KYC verification?
Trust Wallet is commonly used by cryptocurrency investors and users as a popular mobile wallet app. According to Trust Wallet’s Privacy Policy and Terms of Services, there are no KYC requirements for Trust Wallet users. In this non-custodial online wallet, assets and personal information are kept in cold storage for maximum security. Trust Wallet uses a decentralized environment, where each user is in charge of his or her own assets, so no personal information or KYC verification is required to use the service. As a result, be wary of emails prompting you to validate your KYC. If you are an owner of a Trust Wallet account and have recently received such an email, then it’s best to avoid it.
How to avoid frauds on the Internet?
Online scams requesting users to verify their information, purchase different products and subscriptions, or complete some other action through clicking a link or a button, aren’t new and similar scam scenarios are being sent to many Internet users every day.
These scams may often look very trustworthy, but they can be avoided by following some basic online safety tips. First, make sure that you don’t visit untrusted sites. Also, don’t install any random programs, especially if they originate from non-reputed sources. When it comes to your online accounts, make sure that you enable two-factor authentication for maximum protection. If you come across a fraudulent message or a questionable site, it is best to report it as soon as possible and try not to click on spam messages or emails sent from unknown senders.
SUMMARY:
| Name | Trust Wallet |
| Type | Trojan |
| Detection Tool |
Remove Trust Wallet Scam Text
The Trust Wallet Trojan should be removed as quickly as possible by those who have been infected with it. As a first step, we suggest that you follow the instructions provided in the following paragraphs:
- Click on the Windows Start menu (the Start button in the bottom left corner) and select the Control Panel >>> Programs and Features >>> Uninstall a program.
- After you go there, spend some time searching for Trust Wallet and other suspicious-looking apps that were installed on your computer without your permission or knowledge. The name and the Developer of the apps might help you determine whether or not they pose a threat to your computer.
- Then, choose the apps you want to remove and click the Uninstall button at the top of the window to remove them one by one.
- If a pop-up warning like the one shown below displays on the screen when you click Uninstall, choose NO and follow the instructions from the uninstallation guide to finish the process.

Most parts of the Trojan threat should be removed from your computer if you’ve followed these instructions. However, there are several places on your computer where malicious components and dangerous files might be secretly added by a Trojan like Trust Wallet. Therefore, we strongly recommend you not to stop here, but rather to follow the manual removal instructions below to ensure that the Trojan is entirely removed.

Restarting your computer numerous times may be required for the effective removal of all Trust Wallet files and components. With this in mind, we suggest bookmarking this page with removal instruction in your browser so you can have quick and convenient access to it. Or, you can use a smartphone, tablet or another computer to access the guide.
As soon as you’ve saved this page, restart the computer in Safe Mode (click the link for details on how to do that). In Safe Mode, the number of operating processes and apps is limited to just the most critical ones, making it easier to notice any strange behavior on the computer.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Using the Start menu, type msconfig in the search area and press Enter while the machine is in Safe Mode. Take a look at the startup items mentioned in the System Configuration Startup tab:

A startup item with a “Unknown” Manufacturer or a strange name should be unchecked if you suspect it is linked to Trust Wallet or its malicious activity.

Next, open the Windows Task Manager, using CTRL + SHIFT + ESC on your keyboard.
Search for processes that could be associated with Trust Wallet by selecting the Processes Tab. You may also right-click on a suspicious entry and choose Open File Location if it has a strange name or uses a lot of CPU or memory. This will allow you to access all files associated with that process.

The scanner below may be used to check these files for malicious code:

If one or more of the files from the scan turn out to be hazardous, end the process they belong to and remove the folders associated with them.
![]()
It is common for the Hosts file of a computer to get modified when infected with Trust Wallet. This is why you need to copy and paste the code below into the Start menu search field and then press Enter to open up the Hosts file:
notepad %windir%/system32/Drivers/etc/hosts
Next, scroll down in the Hosts file and search for “localhost“.

In the event that you have been hacked, many suspicious IP addresses will be shown under Localhost. Please send us a copy of any suspicious IP addresses in your file. We’ll have a look at these IPs and get back to you with some recommendations.
![]()
In the final step of this guide, you will need to launch your Registry Editor and look for items that Trust Wallet has added to the registry. In order to do so, enter Regedit in the Start menu search bar, followed by a key press on Enter from the keyboard.
After the Registry Editor Opens, use another key combination – CTRL and F – to search for the Trojan infection’s name in the Editor. Type the name of the malware in the Find box, select the Find Next button, and carefully delete any results that are matching that name.
If no results appear in the search, we recommend you check each of the directories below manually for files and folders with peculiar names that are not associated with any authorized software already installed on your computer:
- HKEY_CURRENT_USER—-Software—–Random Directory
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If in doubt, don’t mess with anything in the registry because you might end up causing major damage to your operating system if you delete or alter a particular file or folder that is unrelated to the Trojan infection. In case you need help, please note that you can use the powerful Trust Wallet removal tool listed on this page or the free online virus scanner to find and remove all traces of the Trojan from your computer.

Leave a Comment