*Ttap is a variant of Stop/DJVU. Source of claim SH can remove it.
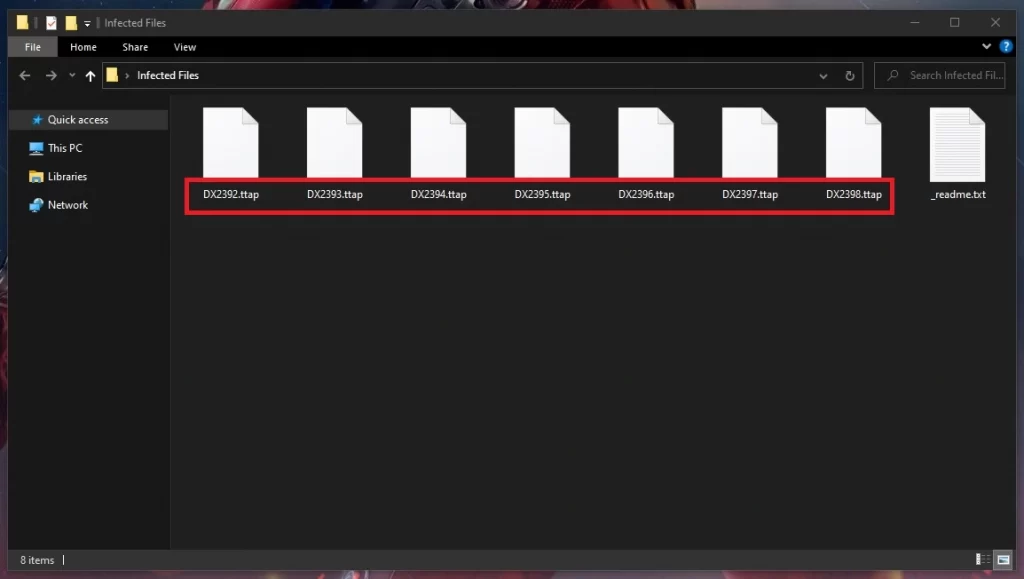
Ttap File
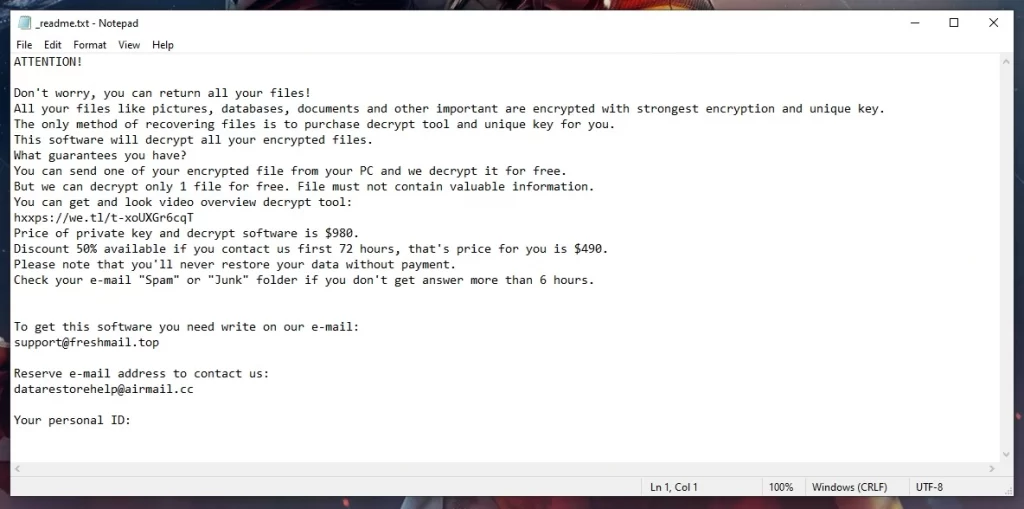
The Ttap file encryption algorithms to lock users’ files and render them inaccessible. Once inside a system, it systematically encrypts a wide array of file formats, appending a unique extension to the affected files, signaling the successful encryption. It then presents a ransom note, demanding payment in cryptocurrency for the alleged decryption tool. The Ttap file encryption leveraged by this virus is generally unbreakable, making recovery extremely challenging without the specific decryption key. Consequently, victims face a grim dilemma: pay the extortionate fee and hope for a solution or lose their files indefinitely. Experts advocate for regular backups and employing reliable security solutions to prevent such infiltrations.
How to decrypt Ttap ransomware files?
To decrypt Ttap ransomware files, you’ll either need to get the unique private key that only the blackmailers have access to (for which a ransom must be paid) or try some free alternative methods, like the one shown at the end of this page. Neither option guarantees file recovery, but the latter one is much safer and won’t put your money on the line.
How to remove the Ttap ransomware virus and restore the files?
To remove the Ttap ransomware and restore the files, you must first follow our removal guide and then check out the suggested file recovery tool posted at its end.
Ttap Virus
The Ttap virus ransomware, a dangerous DJVU variant, encrypts users’ files, holding them hostage until a ransom is paid, generally in cryptocurrency. Falling under the larger umbrella of malware, ransomware is designed to exploit system vulnerabilities to infiltrate and seize control over vital data. The Ttap virus, like other DJVU family members, targets individuals and businesses indiscriminately, seeking financial gains through these illicit activities. The primary goal is straightforward: to exact money from victims in exchange for a decryption key, which purportedly restores access to the affected files. It is imperative to maintain updated security systems and backup files regularly to guard against such attacks, as payment does not guarantee data retrieval.
Ttap
The Ttap ransomware utilizes sophisticated distribution tactics including spam email campaigns, exploiting software vulnerabilities, and malicious advertisements. These methods are crafted to deceive users into initiating the malware download, often through seemingly legitimate attachments or links. To circumvent this ransomware’s distribution strategies, users are advised to maintain updated security software that can identify and block known threats. Additionally, practicing cautious online behavior such as avoiding unfamiliar emails, not downloading software from untrusted sources, and regularly updating system and application software can be pivotal in preventing Ttap infections. By adhering to these preventative steps and fostering a culture of cybersecurity awareness, users can significantly reduce the risk of falling prey to this and other similar ransomware threats, such as Mzre and Ttza.
.Ttap
The “.Ttap” extension is synonymous with the malicious encryption imposed by this ransomware. Files appended with this suffix signify a successful encryption process, rendering them inaccessible to the user. Typically, following the encryption, a ransom note surfaces, demanding payment for potential decryption. It is worth noting that while encrypted files may seem unrecoverable, victims could explore data recovery solutions such as using backup copies, shadow volume copies, or specialized recovery tools. Nevertheless, there are no guarantees of full data retrieval of files with the .Ttap file suffix. It is always recommended to approach reputed cybersecurity firms for assistance and to avoid paying the ransom, as this does not ensure file recovery.
Ttap Extension
The “.Ttap” extension is a distress signal in the cyber realm, indicating that your files have been encrypted by a variant of the notorious DJVU ransomware family. While the files are not damaged or altered in their core structure, the encryption barricades normal access, holding your data hostage. Within this scenario, a ransom note usually follows, coercing victims into paying a hefty sum for a decryption key. It’s imperative to note that succumbing to the ransom demand should be a last resort, as it neither guarantees the retrieval of files with the .Ttap extension nor does it promote a secure cyber environment. Initially, consider alternative recovery options, including consulting with a cybersecurity expert, using backups, or applying legitimate file recovery tools, to regain access without fueling the criminal endeavor.
Ttap Ransomware
The Ttap ransomware, operating under the DJVU family, can infiltrate systems via deceptive emails, malicious downloads, or exploited vulnerabilities in software. Warning signs of an impending attack can include unusual system behavior, sluggish performance, or unanticipated file alterations. Users need to be vigilant and act promptly to spot these signs before data encryption commences. In the event of an infection, it’s crucial to undertake damage control measures: disconnecting external drives and other devices can prevent the malware from spreading further. Regularly updating software, utilizing reliable antivirus solutions, and educating oneself about phishing scams can offer a sturdy defense line. Remember, preemptive awareness and immediate responsive actions are your primary shields against the destructive Ttap ransomware’s encryption crusade.
What is Ttap file?
A Ttap file is a document that has fallen prey to the encryption techniques of this ransomware. Once it infiltrates your system, it encrypts your most valuable files, adding its extension to each one, effectively sealing off access to your own data. In essence, a Ttap file is a hostage, trapped in an unreadable state until a ransom is potentially paid to the attackers to regain access. However, relying on the cybercriminals’ mercy is risky; hence, users are advised to explore every alternative avenue of data recovery available, prioritizing approaches that do not involve engaging with the attackers and further encouraging their criminal endeavors.
SUMMARY:
| Name | Ttap |
| Type | Ransomware |
| Detection Tool |
*Ttap is a variant of Stop/DJVU. Source of claim SH can remove it.
Ttap Ransomware Removal

The removal of ransomware infections such as Ttap might be a quite challenging task, especially for users who are dealing with this malware for the first time. That’s why, we recommend restarting the machine in Safe Mode, as this will limit the number of processes and programs that are running only to the most important ones and, eventually, will make the detection of the malicious components easier.
Before you reboot in Safe Mode, though, make sure to bookmark these removal instructions in your browser or open the page on another device, so that you can simply reload it and complete the guide from start to finish.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ttap is a variant of Stop/DJVU. Source of claim SH can remove it.
In the second step, you’ll need to head to the Task Manager, and take a look at the processes that are running there.
The easiest way to do that is to press CTRL, SHIFT, and ESC, then choose Processes from the tabs at the top.
Look at the list of processes for anything out of the ordinary. Oddly named items that use a lot of CPU or RAM may fall into this category. The easiest approach to check a process for malicious code is to right-click on it, choose Open File Location, and use a trusted scanner to scan the files of that process.

We recommend using the powerful free online scanner below. You can drag and drop the files that you want to check in it and let it do the job for you.

The processes whose files get flagged as harmful should be ended, and the files themselves should be deleted from the system.

Infections like Ttap may alter a variety of system files. That’s why it is a good idea to check the following file for changes. To open it, press the WinKey and R from the keyboard together and paste the line below in the Run window, then click OK:
notepad %windir%/system32/Drivers/etc/hosts
In the Hosts file, go to where it writes Localhost and look for any strange IP addresses like the ones shown below:

Please let us know if you see anything disturbing in your files by leaving us a message in the comments section at the end of this guide.
Next, open System Configuration by typing msconfig in the Windows Search bar:

Check whether Ttap has added any harmful Startup Items to the list by selecting the Startup tab. If a certain item looks dangerous to you, or you cannot link it to any legitimate program that normally starts on your computer, do a fast online search to find out more about it. Next, depending on the information that you find, you may need to uncheck the checkmark of the item that you believe is linked to the ransomware in order to disable it.

*Ttap is a variant of Stop/DJVU. Source of claim SH can remove it.
Attention! Registry files are what you’ll be dealing with in this step. If done incorrectly, alterations to the Registry may damage the whole system.To avoid the risk, please use a professional malware removal tool and scan the files that you plan to delete.
If you prefer to search the Registry manually, you need to enter Regedit in the Windows Search field and hit Enter from the keyboard.
When the Registry Editor appears, press CTRL and F at the same time and write the name of the ransomware inside the Find box. Next, start a search for the ransomware by clicking on the Find Next button.
If any registry entries with that name are identified, they most likely belong to the ransomware and need to be deleted. Nevertheless, you should proceed with utmost caution in order to avoid damaging your system by removing items that are unrelated to the danger.
Once you’ve eliminated any ransomware-related items from the Registry Editor, click the Windows Search bar, and enter the following lines one at a time:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
To ensure that the ransomware hasn’t added any new files to these locations, be sure to thoroughly search each of them for entries with an unusual name. When you open the Temp folder, select all temporary files stored there and remove them.

How to Decrypt Ttap files
The steps required to deal with ransomware may be different, depending on the variant that has attacked your computer. The ransomware’s variant may be identified by looking at the extensions it adds to the files it encrypts.
However, you must first ensure that your computer is free of the ransomware infection. If you have concerns about that, we recommend using a professional anti-virus tool, an online virus scanner or a combination of both to verify that Ttap is entirely removed from your computer.
New Djvu Ransomware
STOP Djvu is the latest variant of the Djvu Ransomware family. This threat is rapidly spreading worldwide and attacking more and more users. In order to distinguish this specific variant from other malware, please search for the .Ttap suffix at the end of the encrypted files.
Once you are sure that STOP Djvu is the threat that has attacked you, you can give a try to the decryption tool linked below and see if it can help you get back your encrypted files.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Open the link ,and then click the Download button on the website to save the decryptor on your computer.
The process of decryption
Make sure that you run the decryptor as an administrator, then confirm by clicking on the Yes button to start the file. Next, you need to read the license agreement and the on-screen instructions before proceeding any further. To decrypt your data, just click the Decrypt button. Please note that the tool may not be able to decode files encrypted using unknown offline keys or files that were encrypted online.
If you have any questions, we would love to know about them in the comments. Also, we would like to know if you find this Ttap removal guide helpful and if it has helped you to deal with Ttap successfully.

Leave a Comment