*Ttza is a variant of Stop/DJVU. Source of claim SH can remove it.
Ttza File
The Ttza file is a particular type of file that can’t be easily accessed using common software. If you attempt to view it using the apps on your computer, you’re likely to get an error because the file has been locked and cannot be accessed without a decryption key. Stumbling upon an Ttza file on your device is a strong indicator of a ransomware attack. Such malicious software restricts you from accessing your files, adding extensions to them, and then holding them hostage for money. Missing the ransom deadline might result in a permanent loss of your files.
Decrypting files affected by Ttza ransomware is a complex task due to the robust encryption method that is used. Therefore, it’s vital to identify the exact variant of the ransomware that has breached your device. Knowing this can help you find specific tools for decryption that are tailored to the threat that you are faced with. To prevent further damage, it is advisable to disconnect the compromised computer from the internet and other networks. You need to invest time in researching reputable sources to find decryption resources, guides or software, or contact a professional for assistance.
To clean your system from the Ttza ransomware virus and recover your locked files, you must disconnect the infected computer from all networks. Then, understand which version of the Ttza ransomware you’re dealing with, as this can help you find tailored removal and decryption tools. Use current antivirus software for a complete scan to detect and remove the associated threat. If needed, manually erase any doubtful files linked to the ransomware. Before retrieving files from backups, ensure your system is ransomware-free.
Ttza Virus
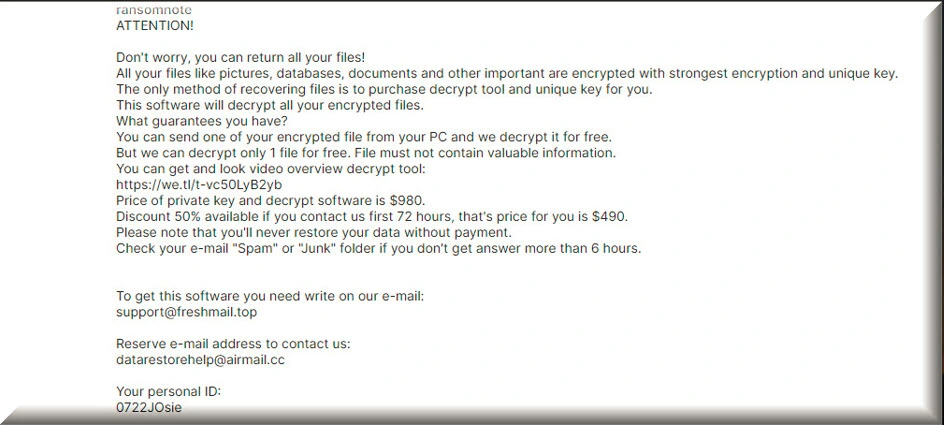
The Ttza virus is a dangerous malware, categorized as ransomware, that sneaks into systems in various ways. Tactics like deceptive online ads, spam email attachments, and disguised downloads are commonly used by the cybercriminals to distribute this threat. It’s not unusual for the Ttza virus to be concealed in seemingly innocent files, like a zipped folder or a macro in a document. Therefore, if you want to stay safe you should always be wary of unknown digital content and maintain an effective security tool. Upon infiltrating your system, the malware immediately begins encrypting a list of files that are stored on your computer’s hard drive. After it is done, you will see a ransom-demanding notification on your screen, or an informative text file that is stored in the folders containing encrypted files.
Ttza
To defend against ransomware such as Ttza or Ttwq is not that difficult, as long as you develop the habit to be alert about the potential threats in clickable links or downloadable files from unverified sources. Safe online habits combined with trustworthy antivirus software can drastically reduce the risk of a ransomware encounter. Of course, keeping all software updated is equally important, since ransomware often targets unpatched vulnerabilities. Nonetheless, the best defense against a Ttza attack is to regularly back up all your essential data, either on external devices or cloud storage. In this way, you can always access it on the backup source and recover it once the ransomware is removed from the system.
.Ttza
the .Ttza Ransomware uses a sophisticated encryption process to lock up your data and demand a ransom for its release. When you accidentally trigger the ransomware infection, the malicious software infiltrates your computer andthen begins an extensive search for valuable files. This search isn’t random. The .Ttza ransomware typically targets files that are important to you, like documents, photos, and videos. Once the ransomware identifies its prey, it employs a complex encryption algorithm that converts your files into a secret code that only the attacker can decipher. To make matters worse, the ransomware displays a ransom note on your screen, demanding payment in exchange for the decryption key. This is the attacker’s way of holding your files hostage, and they’ll often set a deadline to pressure you into paying up.
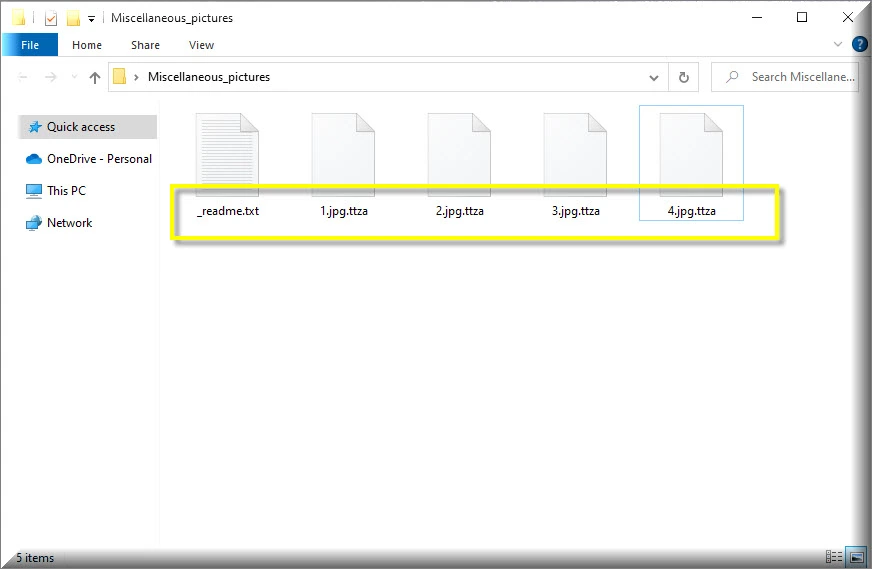
Ttza Extension
Files encrypted by the Ttza ransomware typically have the unique Ttza extension attached at the end. This added tag differentiates the tampered files from their original formats and renders them inaccessible. Identifying which files have been encrypted is usually as simple as spotting the Ttza extension, though some ransomware versions might use varying extensions. The key to recovering your files lies in obtaining the decryption key from the attacker, usually by following their instructions for making a payment. However, paying the ransom is risky and not recommended, as there’s no guarantee that the attacker will actually provide the decryption key or that they won’t strike again in the future.
Ttza Ransomware
The Ttza ransomware operates with a sinister precision that distinguishes it from other cyber threats. Its core objective is to infiltrate your system stealthily, often leveraging deceptive techniques or exploiting vulnerabilities in outdated software. Once inside, it scrambles your files, rendering them inaccessible. Cybercriminals behind this ransomware then initiate their extortion strategy, presenting victims with ultimatums to pay substantial sums for decryption. Even more alarming is its ability to remain undetected, subtly jeopardizing backups that users believe to be safe. Therefore, to stay safe, it is important to implement multi-layered security protocols, including off-site and cloud-based backups, as these offer a formidable defense against the devastating impacts of the Ttza ransomware and other threats.
What is Ttza File?
The Ttza file is like a hostage file taken by the malicious Ttza ransomware. Think of this ransomware as a digital kidnapper that, instead of people, takes your files – be it photos, documents, or videos – and locks them up. Just like a kidnapper leaves a sign or message, the ransomware changes the name or adds a special ending to each captured file to show it’s been taken. Both the bad guys behind the ransomware and the computer owner can easily spot which files are “kidnapped” by looking for these name changes. So, in simple terms, an Ttza file is just a regular file on your computer that’s been locked up by this nasty ransomware and can
SUMMARY:
| Name | Ttza |
| Type | Ransomware |
| Detection Tool |
*Ttza is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Ttza Ransomware

To make it easier to complete all the steps from this guide, you may want to save this page’s uninstallation instructions as a bookmark in your browser. In this way, you won’t have to go searching for the Ttza removal guide every time you restart your computer, since the instructions will already be there.
The next step is to start the compromised computer in Safe Mode, which allows you to see what programs and applications (aside from the most necessary ones) are running on the system and whether they are potentially harmful to your computer.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ttza is a variant of Stop/DJVU. Source of claim SH can remove it.
To open the Task Manager, press the CTRL+SHIFT+ESC keys on your keyboard at the same time. On the Processes tab, you should look for processes with unusual names or processes that are consuming a lot of resources. Right-click on any process that seems to be suspicious to you and choose Open File Location from the pop-up menu that will appear.

Next, scan the files associated with that process to see if any malicious code has been included. A free virus detection program is given below.

If there are files that the scanner detects as dangerous, you may need to first end the suspicious process in Task Manager by right-clicking on it and selecting End Process before proceeding to the files and successfully removing them.

When a system is infected, an attacker has the ability to change the Hosts file. As a result, the next step is to manually search the “Localhost” section of the file for potentially problematic IP addresses (like those on the image below). You may open the Hosts file by pressing the Windows key and the R key at the same time, and then typing the following command in the Run box:
notepad %windir%/system32/Drivers/etc/hosts
To run the command you’ve just typed, press the Enter key on your computer, and then search for any unusual IP addresses in the Localhost section of the file. Please let us know if you come across anything suspicious by posting a comment in the comments space provided below. If we find that the IP addresses you’ve published are dangerous, we will reply to you with advice on what to do next.

In the next step, enter msconfig in the Windows search field and hit Enter. The System Configuration dialog box will appear on the screen as a result of this action. Look for Ttza startup items in the startup tab of the task manager. If you find any, remove their checkmarks and then hit the “OK” button to save your changes. Keep in mind, however, that you should not remove the checkmark from any genuine startup items that are part of your computer’s operating system.


*Ttza is a variant of Stop/DJVU. Source of claim SH can remove it.
To avoid detection and to achieve long-term persistence, an increasing number of malware applications secretly insert malicious entries in the system’s registry. For this reason, if you want to successfully removed Ttza, in this step, you need to use the Registry Editor to search for and remove any Ttza-related files that may have been added there. This may be accomplished by typing regedit in the Windows search field and pressing Enter. Following that, you should be able to view the Registry Editor on your computer’s screen. Search for files that may have been added by the ransomware by pressing the CTRL and F keys at the same time. Enter the ransomware’s name in the Find box and click the Find Next button to begin a search for the malware.
Carefully remove any ransomware-related files that show in the search results. Repeat the search as many times as required until there are no more results to remove.
Attention! If you attempt to manually remove the malware-related files from your registry, you should be aware that there is always the possibility of accidentally removing something else that is not linked to the malware problem. When it comes to safety, using an anti-virus software is the best option since it removes potentially harmful applications and unsafe registry entries without removing critical system files.
Malicious ransomware-related files may also be present in the following five locations. Therefore, you should double-check your system by typing each of the search phrases listed below in the Windows search bar and pressing Enter.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Any questionable files that you come across should be deleted. Holding down the CTRL and A keys simultaneously and pressing the Del key on your computer will remove all temporary files from your computer’s Temp directory.

How to Decrypt Ttza files
It is possible that non-professionals will have difficulty recovering data that has been encrypted by ransomware. Moreover, the decryption processes that may be used to recover the data may differ depending on the variant of ransomware that was used to encrypt it. It is possible to distinguish between different ransomware variants based on the file extensions that are attached to the encrypted data.
A thorough scan of your computer using a professional virus removal program (such as the one available on our website) is the most important thing you can do before trying any data restoration steps. After the scan has shown that there are no threats on the system, it will be safe for you to experiment with the various file recovery options that are available.
Next Djvu Ransomware
According to security experts, the STOP Djvu ransomware is a new variant of the Djvu ransomware that has been found. The files encrypted by this new threat carry the extension .Ttza at the end of their names. In certain cases, using a decryptor such as the one found at https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu, you may be able to recover your encrypted data.
Before you can begin the decryption procedure, you must first download the STOPDjvu.exe software from the specified URL. To run the file as an administrator, right-click on it and choose “Run as Administrator”, then confirm. You’ll also want to make sure you understand the license agreement and any accompanying instructions. However, it is vital to remember that this tool will not be able to decrypt data that has been encrypted with unknown offline keys or with online encryption.
If you encounter any issues when removing the Ttza ransomware, the anti-virus software available on our website may be of assistance. You may also use our free online virus scanner to check for any strange files that you come across.

Leave a Comment