*Ttrd is a variant of Stop/DJVU. Source of claim SH can remove it.
Ttrd File
The Ttrd file encryption is a malicious process initiated by a ransomware infection that turns your files into digital puzzles with no solutions, essentially locking them away from you. Imagine if your files were written in a secret code that only the attacker could understand. That’s what happens when ransomware strikes. The Ttrd file encryption employs complex mathematical algorithms to jumble the contents of your files, making them unreadable. It’s like taking your favorite book and replacing every word with a random set of characters. To make matters worse, the attackers then demand a ransom, usually in cryptocurrency, in exchange for the decryption key. Until you pay up, those files remain trapped, leaving you with a tough decision: succumb to the attacker’s demands or try to find another way to break the encryption.
How to decrypt Ttrd ransomware files?
If Ttrd ransomware has encrypted your files, decryption can be daunting due to the advanced techniques used by this threat. However, what you can do is detect the exact strain of Ttrd affecting your computer. Recognizing this strain aids in seeking specific decryption methods linked to the exact threat that has attacked you. Of course, you will need to do an extensive research to find decryption tools and solutions from authoritative sources.
How to remove Ttrd ransomware virus and restore the files?
To cleanse your device from the Ttrd ransomware and regain the encrypted files, you should detect which strain of ransomware has compromised your system, as this knowledge facilitates the targeted removal of the threat that has compromised you. You can utilize an updated antivirus tool for a comprehensive scan and removal, or manually delete any traces of the ransomware with the help of a removal guide. What is really important is to ensure the system is thoroughly clean before restoring any backups.
Ttrd Virus
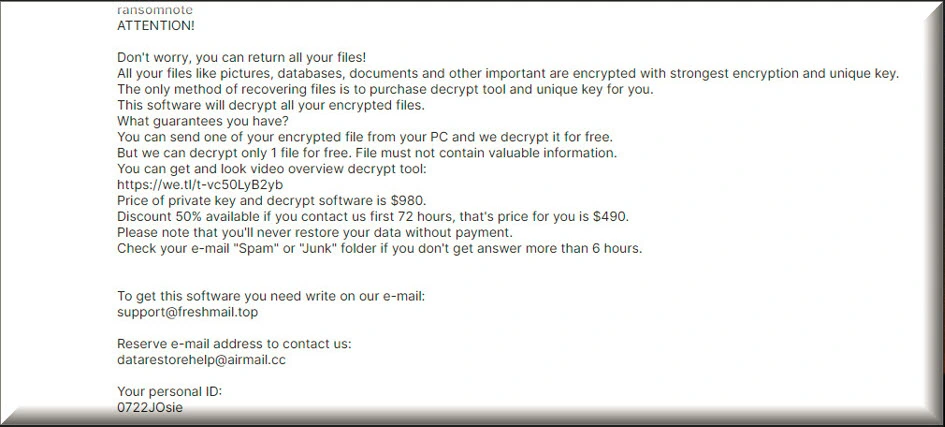
When your files are encrypted by a ransomware like the Ttrd virus, it’s like they’ve been transformed into an unreadable secret code that only the attacker can decipher. Imagine your cherished photos, important documents, and valuable data becoming nothing more than gibberish. You won’t be able to open or use these files because their content has been scrambled beyond recognition. To add to the distress, the Ttrd virus often displays a menacing message on your screen, demanding a ransom in exchange for the decryption key. Until you pay up and get that key, your files remain inaccessible and effectively held hostage. This situation can be incredibly frustrating and worrisome because it may result in you losing your files forever.
Ttrd
If your files are encrypted by Ttrd, Ttwq or Mzre, it’s crucial not to panic and follow a careful plan of action. Under no circumstances should you pay the ransom, as it’s risky and encourages criminal activities. Instead, report the incident to law enforcement, which can aid in tracking down the cybercriminals. Also, seek assistance from cybersecurity professionals or firms specializing in ransomware recovery, as they may have tools or expertise to decrypt your Ttrd files. If you have clean and up-to-date backups, use them to restore your system. Finally, enhance your cybersecurity practices to prevent future attacks, including regular software updates, strong passwords, reliable antivirus software, and educating yourself and your team about ransomware prevention.
.Ttrd
As unpleasant an .Ttrd ransomware attack could be, it may be possible to decrypt the ransomware-encrypted files without paying the ransom, but that depends on various factors. In some cases, security experts and law enforcement agencies may manage to crack the encryption used by certain ransomware strains, making free decryption tools available to victims. Additionally, having clean and up-to-date backups of your files allows you to restore your .Ttrd data without yielding to the ransom demand. However, it’s essential to exercise caution when searching for decryption tools online, as not all of them are safe. Stick to reputable sources like cybersecurity firms and official law enforcement websites to download decryption tools, as some malicious actors use the guise of decryption tools to distribute malware.
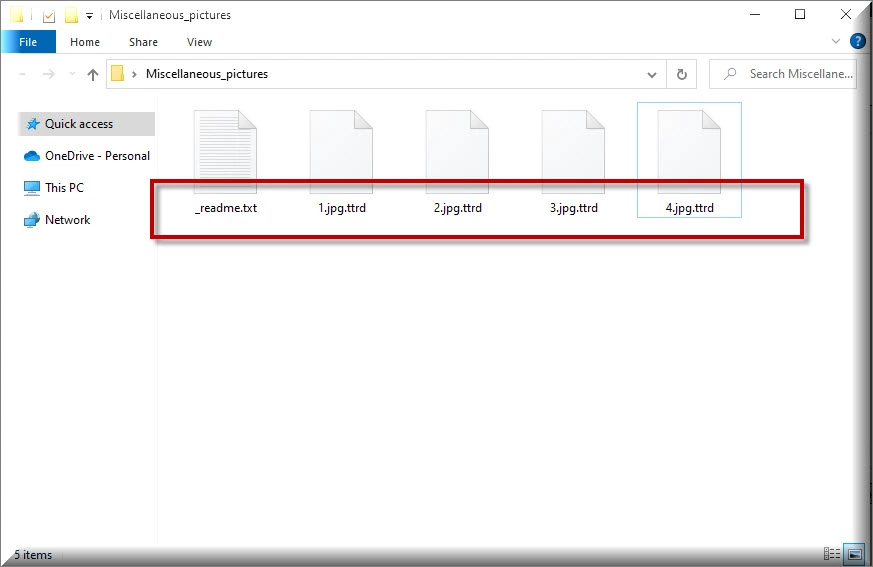
Ttrd Extension
The ransomware often operates silently until it strikes, but there can be some signs to watch for before it adds the Ttrd extension to your files. First, you might notice a sudden slowdown in your computer’s performance as the ransomware silently works in the background. Additionally, you may receive phishing emails or encounter suspicious links and attachments in emails or on websites that, if clicked, can lead to a ransomware infection. Once your files are encrypted, you’ll typically see the new Ttrd extension added to them. After it is done, the ransomware will display a ransom note on your screen that demands payment and makes it clear that your files are no longer accessible without the decryption key.
Ttrd Ransomware
The Ttrd ransomware attackers typically demand payment in cryptocurrency, such as Bitcoin, as it offers relative anonymity. They provide victims with detailed instructions on how to acquire the required cryptocurrency and send it to a specific wallet address. Once the payment is made, victims are instructed to send proof of payment to the attackers. After verification, the attackers will supposedly provide the decryption key. However, paying the ransom is not recommended due to the risks involved, including the possibility of not receiving the decryption key and supporting criminal activities. It’s usually advisable to explore other Ttrd ransomware recovery options, such as restoring your files from clean backups.
What is Ttrd File?
The ransomware has the capability to encrypt a wide variety of file types, making it a versatile and potent threat. It doesn’t discriminate based on file types, so it can target and encrypt documents, photos, videos, spreadsheets, databases, and much more. Essentially, if a file resides on your computer and is accessible, the ransomware can potentially encrypt it and turn it into an Ttrd file. This indiscriminate nature is one of the reasons why ransomware attacks can be so devastating, as they can impact both personal and business data, causing substantial disruption and distress. This encryption is typically distinguished by the addition of a unique Ttrd file extension or an altered file name that serves as a telltale sign of the attack.
SUMMARY:
| Name | Ttrd |
| Type | Ransomware |
| Detection Tool |
*Ttrd is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Ttrd Ransomware

Remember to save these instructions as a bookmark if you’re dealing with ransomware, so you don’t have to keep searching for them after every system restart that is required. Rebooting the system in Safe Mode before proceeding to the second step of this guide will also make it easier to detect and remove the malware.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ttrd is a variant of Stop/DJVU. Source of claim SH can remove it.
The next step in this guide is to check the Task Manager’s Processes tab for any suspicious processes by pressing CTRL+SHIFT+ESC on your keyboard. Unusual processes, such as those that aren’t associated with any of your regular programs, should get extra attention. When a suspicious process catches your attention, right-click on it and select Open File Location from the context menu.

You can check for malicious code in files associated with the suspicious-looking process using the free online virus scanners listed below. You can scan files by dragging and dropping them into the scanner from the File Location folder of a suspected process.

After you see the results from the scan, you have to remove any potentially harmful files that are discovered during the scanning process. It is best to end the suspicious process prior to deleting the files by right-clicking on it and selecting End Process from the context menu, as some files may not be deleted while the process is running.

After searching for the command msconfig in the Windows search bar and pressing Enter, click on the result to open System Configuration. Once in System Configuration, select the Startup tab and look for any startup items that could be related to Ttrd.

Check off any startup item that doesn’t come from a reputable source. You should only leave the checkboxes next to legitimate startup items that you want your system to start with.
Another location on a computer where changes could be made without your permission is the Hosts file. Open it and look for any suspicious IP addresses listed under “Localhost”. In order to do so, open a Run window by pressing Win+R, then paste the following line into the text box and press Enter:
notepad %windir%/system32/Drivers/etc/hosts
Check the Localhost section of the Hosts file as shown on the image below. Please send us any IP addresses that look suspicious in the comments below. They will be investigated by a member of our team to determine whether or not they are dangerous.


*Ttrd is a variant of Stop/DJVU. Source of claim SH can remove it.
In order to remain on the system longer and be more difficult to remove, more advanced malware frequently adds harmful registry entries. You may not be aware of the harmful files that Ttrd may have added to your registry, thus, we recommend you to use the Registry Editor to see if you can locate any and remove them. This can be done in a variety of ways. To open the Registry Editor, type Regedit in the Windows search bar and press Enter. CTRL and F can be pressed simultaneously to open a Find window inside the Registry Editor. Enter the ransomware’s name and click “Find Next” to start the search process.
Remove any ransomware-related entries that appear in the search results. Once a result has been found and removed, the search may be repeated as many times as needed.
Attention! If you delete files unrelated to the ransomware infection while cleaning up the registry, the operating system may be damaged. If you don’t delete all associated registry entries, on the other hand, the threat may return. As a result, we urge you to run a malware scan and a registry clean with an anti-malware program.
The following five locations should also be checked manually. Type them exactly as they are shown in the Windows search bar and press Enter to open them one at a time.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Remove any dangerous-looking files that have recently been added to any of these locations. Selecting the files in your Temp folder and pressing Del on your keyboard will remove all of the temporary files in your system.

How to Decrypt Ttrd files
Ransomware victims still face the challenge of decrypting their encrypted files, even after they have had the ransomware removed. Ransomware comes in many forms, and each one may have a different means of decrypting the encrypted data. In order to identify a specific ransomware variant, look at the extensions of the encrypted files.
Prior to attempting to recover your files, you should run a reliable anti-virus scan with a trusted security tool (such as the one available on this page) on the infected system. A ransomware-free machine can be used to test various file recovery methods and even connect backup sources after you’re sure the computer is clean and the virus has been removed from it.
New Djvu Ransomware
Experts in the field of cyber security have recently discovered STOP Djvu, a brand-new Djvu ransomware variant. The .Ttrd suffix at the end of files encrypted by this infection sets it apart from the rest of the malware. You can decrypt data encrypted by this threat using an offline key decryptor, such as the one found at the following link.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Once you download the STOPDjvu.exe file on your computer from the link above, select “Run as Administrator” to open it. To start the program, simply press the Yes button. You can begin decrypting data as soon as you’ve read the license agreement and any accompanying brief instructions. Please note that unknown offline keys or online encryption cannot be decrypted with this tool.
If you need to get rid of the ransomware quickly and easily, consider using the anti-virus software listed in this guide. Alternatively, a free online virus scanner can be used to check for any suspicious files.

Leave a Comment