Ultimate Volume Booster may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Source of claim SH can remove it.
Ultimate Volume Booster
Ultimate Volume Booster is a computer malware designed to advertise certain sites directly from within the user’s browser. Security researchers categorize Ultimate Volume Booster as Adware and their advice is to remove this app from your browser ASAP if it is currently installed in it.

The ads, browser page-redirects to Searchinet, pop-ups and banners, generated by Ultimate Volume Booster, may quickly get on your nerves if you don’t know how to remove them and how to permanently stop them from spamming the screen of your Chrome, Firefox or Explorer browser. That’s why, in the next lines, we have prepared a special removal guide with step-by-step instructions which will explain to you how to deal with this nagging adware and how to uninstall it once and for all. Unfortunately, this type of software is very commonly encountered all over the Internet and pretty much everyone faces difficulties when trying to deal with it. The reason is, unlike most regular applications which can be uninstalled from the Control Panel menu or through their uninstallation kit, the adware may not have such options and it might be quite difficult to completely remove this app from the computer. You may try to get rid of it by removing it from the extensions menu in the affected browser but that may still not be enough to stop it from generating ads the very next time you open the browser. At the same time, many users tend to get panicked and tend to consider the adware as some sort of a nasty virus which is probably trying to infect them with even nastier threats like Ransomware or Trojans. This is a quite exaggerated assumption because the nature of this software is generally not malicious. Still, its presence on the system would normally make the web browsing quite unpleasant and frustrating. That’s why, in the paragraphs below, we have published a step-by-step manual, which can help the people who may have Ultimate Volume Booster in their browsers successfully deal with it. The guide contains detailed instructions and screenshots, as well as an automatic removal tool which can scan the entire system for adware and eliminate it.
The Ultimate Volume Booster Virus
The main reason why we usually advise our readers to remove applications like the Ultimate Volume Booster virus from their system isn’t because the adware itself is harmful. The browser extension on Chrome Ultimate Volume Booster sends any searches from Google through Searchinet.net
There are much more serious computer threats such as Ransomware viruses, Trojans, Rootkits and others, which will do far worse things to your computer than flooding its screen with sponsored ads. However, while the adware is certainly not as dangerous as real malware, its randomly generated ads may be carriers of various security hazards. This is the reason why such pieces of software are still not to be trusted completely, especially when they prompt you to click on redirect links, unfamiliar websites, different offers, pop-ups, banners and similar eye-catching content with unverified origin. After all, it is a well-known fact that the criminal hackers often use misleading links and intriguing ads in order to distribute viruses and nasty computer threats. Of course, an application like Ultimate Volume Booster is unlikely to purposefully make you click on harmful promotional content, but, technically, it is perfectly possible that some of the displayed adverts may be linked to security hazards, which may sneak inside your computer if you happen to click on them.
SUMMARY:
| Name | Ultimate Volume Booster |
| Type | Adware |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Different intrusive ads may spam your screen during your regular web browsing. |
| Distribution Method | Common sources of adware are torrents, spam messages, ads, freeware sites, program bundles, free download links. |
| Detection Tool |
We tested that SpyHunter successfully removes Ultimate Volume Booster* and we recommend downloading it. Manual removal may take hours, it can harm your system if you re not careful, and Ultimate Volume Booster may reinstall itself at the end if you don't delete its core files. |
*Source of claim SH can remove it.
Remove Ultimate Volume Booster Virus
To try and remove Ultimate Volume Booster quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Ultimate Volume Booster extension (as well as any other unfamiliar ones).
- Remove Ultimate Volume Booster by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Ultimate Volume Booster and any other suspicious items.
If this does not work as described please follow our more detailed Ultimate Volume Booster removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Source of claim SH can remove it.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Ultimate Volume Booster from Internet Explorer:
Remove Ultimate Volume Booster from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
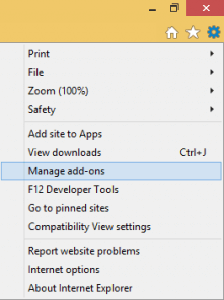
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
 Remove Ultimate Volume Booster from Firefox:
Remove Ultimate Volume Booster from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

 Remove Ultimate Volume Booster from Chrome:
Remove Ultimate Volume Booster from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
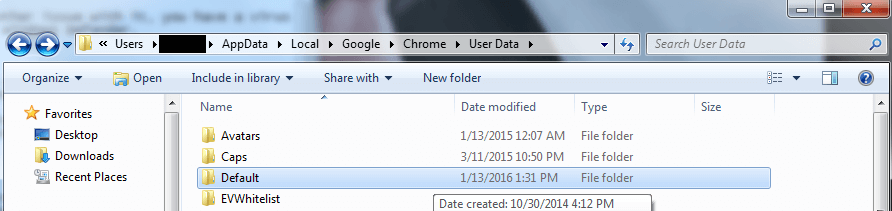
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!


Leave a Reply