Trezaa
Trezaa has been classified as an adware. Programs like Trezaa are known to cause all sorts of internet browsing problems like changing of the user’s designated home page or even the preferred browser of choice and a number of unwanted pop-up ads.
If you are looking at this page, you have undoubtedly noticed unusual behavior on your PC. Either in the form of advertisements, excessive pop-up ads, random opening of webpages and/or other unwanted tabs, and worst case scenario: opening of additional browsers when you have no intentions to use them. You have probably also noticed that this is not happening just with Chrome, for instance, but with Mozilla Firefox and Internet Explorer too.
This article will help you to understand what exactly has happened or is happening with your PC, how to remove Trezaa Malware and how to protect yourself for the future. If you still have questions, you’re welcome to leave them as comments and we will reply to you in a timely manner.
What is Trezaa?
Another sign of Trezaa Malware is something we call “browser hijacker”. Simply put: this is when you are working on your computer and suddenly random web pages begin to open or additional browsers. The content seen on these websites is usually, again, something of the type of the ad mentioned above or even worse, inappropriate.
This is as high as the red flag can go to signalize that something is definitely gotten into your computer and needs your prompt attention and to be uninstalled. Any delay of removing will cause further infection to your files!
We live in a digital era where computers and other digital inventions have taken over most of what used to be ‘man-done work’. Along with the convenience of it and efficiency, hackers are taking advantage of our naive trust in computers, programs, etc. They know how we think, what we use our devices for and have created threats that attack us on a regular basis. A decade ago a computer malware was just that: a virus. Now the word is not a good enough definition as there are many types and kinds of viruses. Today, we will tell you of Trezaa Malware. As much as some still consider it not to be a virus and even a legal software, the truth is that it is not — it is harmful.
Trezaa Malware could be easily spotted by simply paying close attention to the advertisements and pop-up ads on the web pages you visit. Yes, it is always nice to catch a good promo-ad about a discounted vacation on the Hawaii islands, but is this really coming from a legit tourist company? Well, if the ad looks suspicious in any way, such as: flashing images, changing content, asking for a good amount of money as a security deposit, or if it is simply prompting you to click on it — “you’re one click away from your dream vacation!”, kind of thin — then it is 100% a sham. The more you click on such ads, the more they will continue to pop-up and the only way you can escape is to find the virus and remove it off your PC.
Let’s look another aspect of Trezaa Malware now… How is it distributed?
There are more ways for Trezaa Malware to be spread than you and I know. Hackers are called that for a reason. Either via infected e-mail messages, such as the phishing e-mails — they tend to appear like any other regular e-mail you receive, but end up having no text, changing and/or self-deleting text or are simply flashing — or through letters from your Spam box/folder, or via “software bundle” — you have downloaded a program and along with it you have unintentionally downloaded few others that are carriers of the virus — when a hacker has determined that the malware needs to be spread, they will find a way to do it.
You are strongly encouraged to read carefully the removal guide attached below, familiarize yourself with the basic removal techniques and don’t be afraid to apply them when the unusual PC behavior begins. It is only in your best interest to do so.
SUMMARY:
Trezaa Malware Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
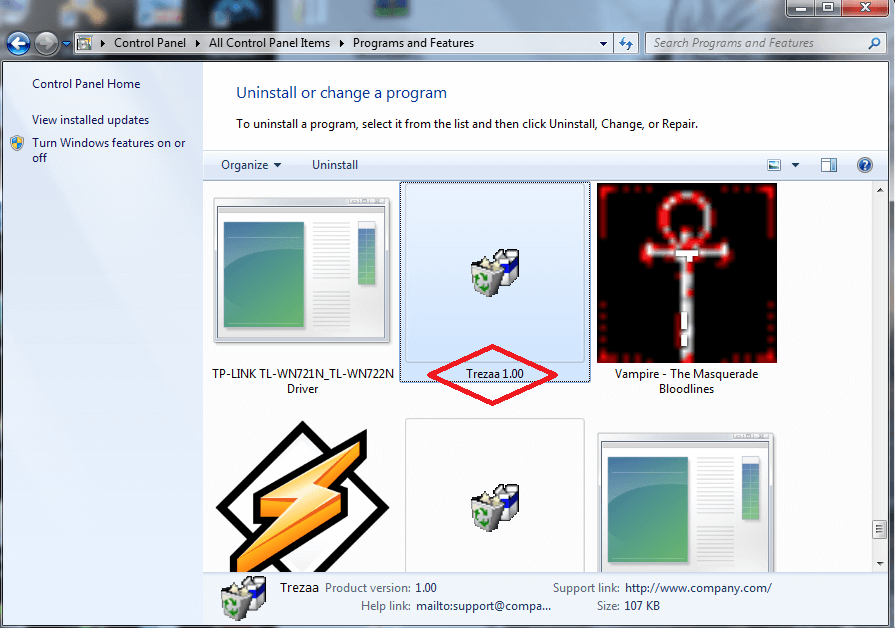
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Reply