The Ursnif Malware
Ursnif is a malicious program from the Trojan Horse type that can steal sensitive user information and provide hackers with remote access to the infected machine. If not removed on time, Ursnif could also destroy important digital data, turn the computer into a bot, or corrupt the entire OS.
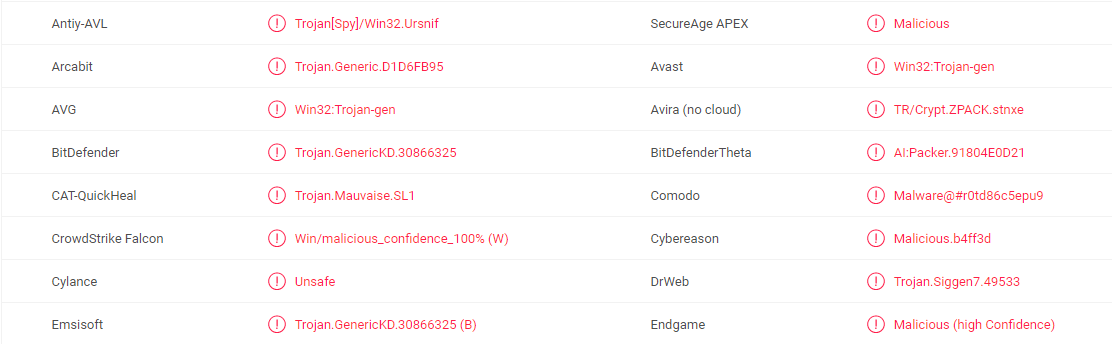
The Ursnif Malware detected by multiple anti virus programs
Trojan horses at the present moment – just as hazardous as the Trojan they were named after
This category of malware comprises a lot of different viruses. Nowadays they are constantly increasing in numbers, and we can say that the variety of their diverse purposes (the most typical of which we have introduced later in the text); as well as the number of their possible sources (also to-be-discussed in the next paragraphs) are also rising.
What makes them a separate software group is their normal way of acting. Firstly, you can never see such a serious threat coming. Secondly, you will never know what exactly such a multifunctional virus intends to do to you or your PC. Last but not least, such an infection itself is not easily seen at all in the general case. Normally, you will realize you have been hacked right after Ursnif Virus(or another Trojan virus) has successfully implemented its (usually evil) plan. The plans of these viruses very much resemble the way the Greeks won the Trojan war – they are equally cunning and subtle. And if we talk about their possible hiding places, these programs are very well-distributed. No website, no program and no torrent on the Internet can be considered safe anymore. Such viruses can find a way to invade anything – from a document to a file-sharing web page; from an online ad to an email letter and its attachments. Ensure that you avoid all sorts of software, which gets spread for free, because such places and files are also a common source of various malware.
Potential consequences you may be facing, once your system has been contaminated with a Trojan
The effects of the appearance of such a virus inside your system could really be terrible. Trojan horses are usually able to perform plenty of malicious activities and the damage they might cause may be of a different sort. Here we have listed the most common ones.
- Data corruption, destruction or a total system crash. The idea of having your PC crashed, your operating system completely destroyed, or your data modified surely sounds disgusting. However, this possible effect from a malware infection could be the lesser evil of all the potential ones you may be facing.
- Spreading of Ransomware. Trojan horses may be exploited for distributing other sorts of malicious software. Generally speaking, the viruses that they may be spreading are mainly Ransomware-like programs. This possible usage of Ursnif is awfully disturbing as these different kinds of viruses are truly dangerous enough alone; and if combined, they may indeed give you no other opportunities but to have to fully reinstall your machine. The ransom-demanding viruses are particularly awful as they do encrypt your most regularly accessed files, and after that you can do really nothing effective enough to recover them.
- All sorts of stealing activities. Such programs may be used as theft tools, bank-account stealing means, social media accounts hacking instruments. The cyber criminals behind Ursnif may be after your finances, so that the virus could be set to track down all the bank account information that you enter while being online. Another possibility is that they might as well be after your own identity, so the purpose of such malicious software may be your social media accounts and other online profiles.
- Simply spying on you as an individual or as a professional. Maybe you will become the victim of spying, both professionally and personally. Some hackers may be psychotic and may want to track your activity 24/7. Moreover, some company’s sensitive information might be what interests the hackers. In such a case, your PC will be used as a means of hacking your professional network.
Indeed, there may be other potential usages of this sort of malware, but only the most widely used of them could be described in only one article.
The process of removing such a virus
Luckily, we have a potential solution for your Trojan-caused problem. To safely and successfully get rid of Ursnif, implement the instructions in the Removal Guide below with attention and care.
SUMMARY:
| Name | Ursnif |
| Type | Trojan |
| Detection Tool |
Remove Ursnif Malware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Comment