Usheethe
Recently, many users have made disgruntled reports about an unknown piece of software called Usheethe that has introduced changes to their browsers. It has replaced the default search engine, it has changed their homepage to Usheethe, it has made modifications to their toolbar and so on.

The annoyance that the Usheethe virus, a browser hijacker can bring into your everyday browsing activities oftentimes depends on what kind of person you are – some people get easily irritated by random page-redirects and pop-up clickbait ads, while others don’t pay such irritations that much attention.
Usheethe . com / mdnk
Regardless of the individual facing these annoyances, it is still safe to assume that most people wouldn’t be too happy with the presence of Usheethe . com / mdnk in their Chrome, Safari, or Firefox (or another) browser. However, what’s even worse than the intrusiveness of these apps, like Usheethe . com / mdnk and Wp20.ru, is their potential of weakening the security of your browser, and, in turn, that of your whole system.
If that is something which sounds familiar to you because you are currently dealing with a similar type of irritation in your browser, then make sure to read every piece of info that this article, and the guide below it, have to offer. Usheethe is the webpage that this new and invasive hijacker seems to promote and if you are not okay with this being your current browser homepage, then we may have some good news for you – after you finish reading this article and the removal guide attached to it, you should have no problem removing Usheethe from your browser and keeping hijackers like the one responsible for its promotion away from your computer.
Usheethe.com
The Usheethe.com browser hijacker components that get added to the users’ browser aren’t really viruses or some other kind of insidious malware, which is something many people mistakenly take them for. An app like the one that has added Usheethe.com as your starting page won’t try to access your files, mess with them, damage your system, spy on you and so on – those are all activities reserved for Trojans, Spyware, Ransomware and other highly dangerous forms of malware.
Despite that, however, a hijacker may still indirectly contribute to the decrease of your system’s security levels. The random redirects that it may trigger in your browser, and the ads that some hijackers are likely to spam the users with may sometimes originate from unreliable online locations. Needless to say, if you somehow land on some shady page with questionable contents, the chances of getting your system attacked by a Trojan, a Ransomware or some other nefarious software piece, go up. Therefore, it is important to keep your browser clean and secure – no extension or other additional software components in your browser should be able to do anything without your permission, and since the hijacker you are currently dealing with does exactly that, it should be uninstalled.
As far as keeping such software away in the future, be sure to always check the custom setup settings in the installer of programs you are about to install in your machine – oftentimes, there would be bonus components in the installer, some of which may be hijackers.
SUMMARY:
| Name | Usheethe |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Hijackers typically introduce unwanted and annoying changes to the affected browser. |
| Distribution Method | Most users get hijackers alongside other programs that they install in their computer – the hijackers are normally included in the setup file of the main program. |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Remove Usheethe Virus
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Usheethe from Internet Explorer:
Remove Usheethe from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
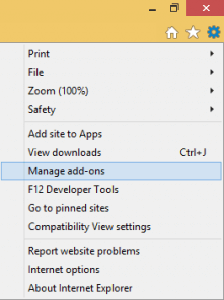
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
 Remove Usheethe from Firefox:
Remove Usheethe from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

 Remove Usheethe from Chrome:
Remove Usheethe from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
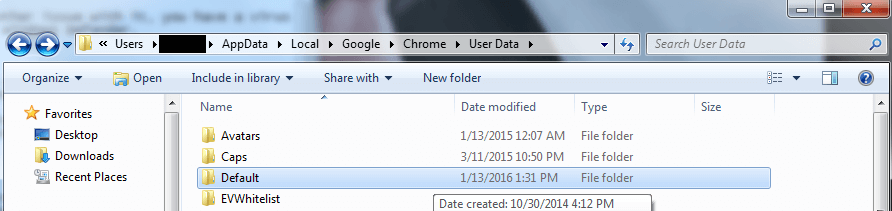
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!



Leave a Comment