Utatity
Utatity is a malicious piece of software widely identified and listed by experts as a Trojan horse virus. Utatity infects computers without showing visible symptoms and can typically remain hidden in the system for quite long.
The Virus secretly infect your system and makes strange tabs open automatically
Detecting Trojans can be difficult because these threats can easily blend with the rest of the software on your computer and can even camouflage their processes as regular system processes. Nonetheless, if you have a reason to believe that your computer has been compromised by a Trojan called Utatity, then you need to take the necessary steps to remove it so that it does not carry out its dangerous activities. Here we will do what we can to educate you about how to get rid of the virus and how to prevent similar attacks on your system in the future. What is more, we will go over a couple of the key characteristics of Utatity and the Trojans in general and will try to give you an idea of what they are capable of.
The Utatity Virus
The Utatity virus can sometimes be used as a spy tool to secretly capture sensitive data from the infected computer and then use it for blackmail, banking fraud and other illegal activities performed by hackers. In other instances, the Utatity virus can take over the whole device, exploiting the system’s CPU and RAM to mine cyptocurrencies for the hackers.
In such situations, the infection is more apparent, and can manifest as extreme slowdowns, freezing, program errors and perhaps even BSOD crashes may occur due to overload of the system. In general, however, there are no specific symptoms that can indicate the presence of the infection on the computer. Users must either be very observant of unusual system behavior or rely on professional security software to detect the Trojan. The latter is actually the best way to catch threats like Utatity before they manage to damage the computer in a serious way. That’s why our recommendation is to invest in a reliable antimalware program and use it to scan your computer for Trojans, viruses, Spyware, and other stealthy threats.
A very malicious ability of the members of the Trojan Horse family is their ability to perform different criminal activities one after the other. It is generally impossible to tell what a malware such as Utatity is up to while on your computer because the hackers who control it can set it to carry out specific criminal tasks depending on their criminal intentions. The Trojan can effectively be used to spread ransomware, spyware and different viruses and to invite them in the compromised computer by exploiting its vulnerabilities. A lot of new ransomware versions actually come in a combo with a Trojan and attack the victims’ machines in secret.
That’s why security experts advise that the Trojan be removed immediately if you don’t want to experience any of the aforementioned malicious effects on your machine. As far as prevention is concerned, it is important that you only use credible and trustworthy websites to access information and to avoid sites that appear to deliver poor quality or pirated apps! It is also critical for you to filter spam messages and click-bait ads in order to avoid potential infections with a Trojan or other harmful viruses.
SUMMARY:
| Name | Utatity |
| Type | Trojan |
| Detection Tool |
Remove Utatity Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
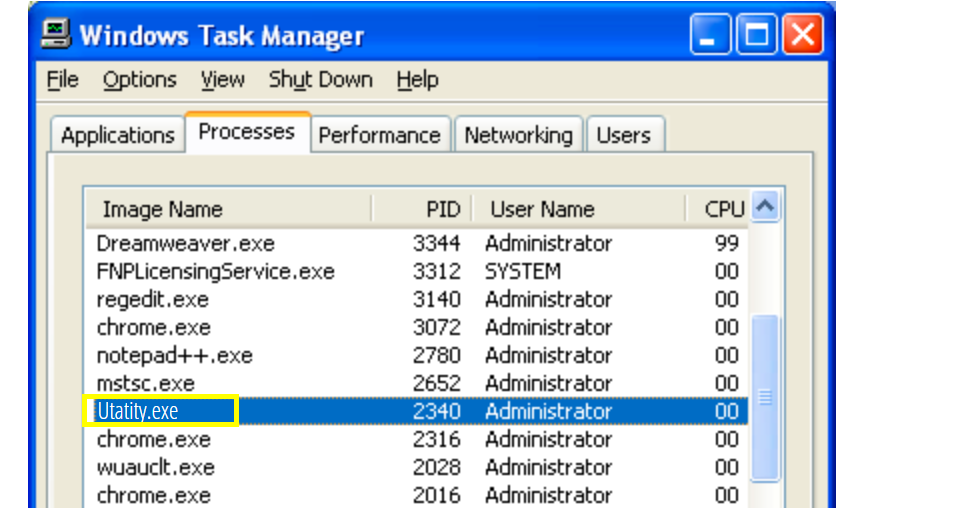
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment