.Vari
.Vari is a new and highly dangerous ransomware cryptovirus. .Vari encrypts user files and prevents its victims from accessing these files until they pay a ransom.
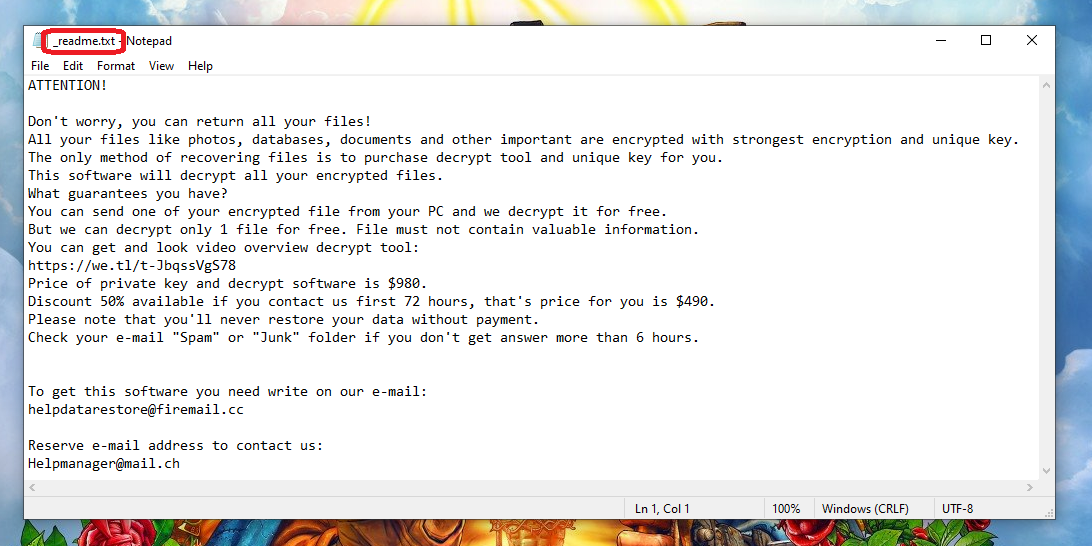
The .Vari Virus will show you this message in a .txt file.
If you have recently noticed that your images, photos, audios and documents have become unavailable because .Vari has put its secret encryption on them, here you can learn what to do to remove the infection and potentially recover your encrypted data without paying a ransom to some anonymous hackers.
A strange ransom message has probably appeared on your desktop after your .Vari files have been encoded. This is the note the hackers use to inform their victims of the ransomware attack and ask them to pay some money to their Bitcoin wallet to get a special decryption key for the encrypted files.
This is basically how most ransomware cryptoviruses like .Vari, .Oonn and .Nile work – they secretly sneak in the system (by exploiting camouflaged transmitters or system vulnerabilities), and lock the information stored there without warning. This stealthy technique helps the criminals to blackmail the users whose data has been encrypted, and to extort some money from them for a decryption key.
The .Vari virus
The virus .Vari is usually very sneaky, and without the right tools, is typically difficult to detect it while running. Still a possible symptom of the .Vari virus in action is the significant slowdown of the system without any particular reason.
Sadly, in most cases, this is not enough to draw the necessary attention from the users and the ransomware manages to complete its agenda without being interrupted. The hackers behind the threat can be really persuasive in their attempts to convince you to pay them the demanded ransom. They typically try to make you pay so soon as possible and promise to send you a decryption key for your files as soon as you fulfill their demands.
Security experts, however, believe that the payment of the ransom is not a reliable data recovery option as it just makes you risk your money without any guarantee for your files and computer’s future. We also share the same opinion and don’t advise our readers to trust anonymous cyber criminals with their money. Moreover, once you agree on their terms, the hackers can blackmail you again and again for as long as the ransomware is present on your computer. Not to mention that you will not be able to create and save new files on the infected machine without them being encrypted. Thus, our best advice is to focus on how to remove .Vari in the safest possible manner.
The .Vari file encryption
The .Vari file encryption is a stealthy process that can last for several hours. But once that is over, it is extremely hard to reverse the .Vari file encryption without using a decryption key.
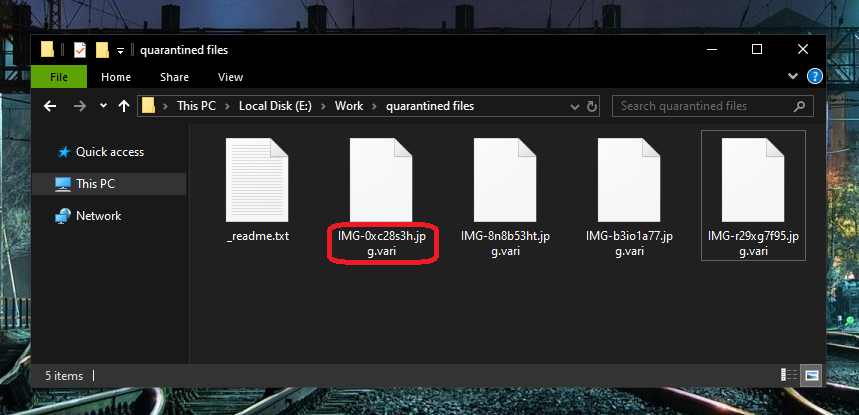
.Vari will start encrypting your files as soon as it has infected your computer.
If you can’t figure out how to remove .Vari from your system and can’t find a workaround for the files it has encrypted, we recommend you check out the removal guide at the end of this post. It includes instructions that may help you remove the infection and search for other hidden threats. Once you have finally deleted the ransomware, check out our tips for free file recovery in the file-recovery section of the guide. There you will find some free methods that may potentially help you to retrieve some of your precious data.
SUMMARY:
| Name | .Vari |
| Type | Ransomware |
| Detection Tool |
.Vari Ransomware Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Hello
I have a .vari virus that cannot open the data file
I need to recover data encrypted by .vari virus
Thank you so much
Hi Tho,
you can go to How to Decrypt Ransomware page and try decryptors there.
Hello
I have a .vari virus,I need to recover data encrypted by .vari virus.
(personel id does not end with t1 then i have benn infected online
)
Hi tayib id mabiri,
i am sorry to hear that but if you are infected with online key then recovery is impossible.