VCrypt
VCrypt is a file-encrypting ransomware threat that infects computers without visible symptoms. VCrypt primarily blocks access to certain files on the computer and then asks the owner to pay a ransom for them.
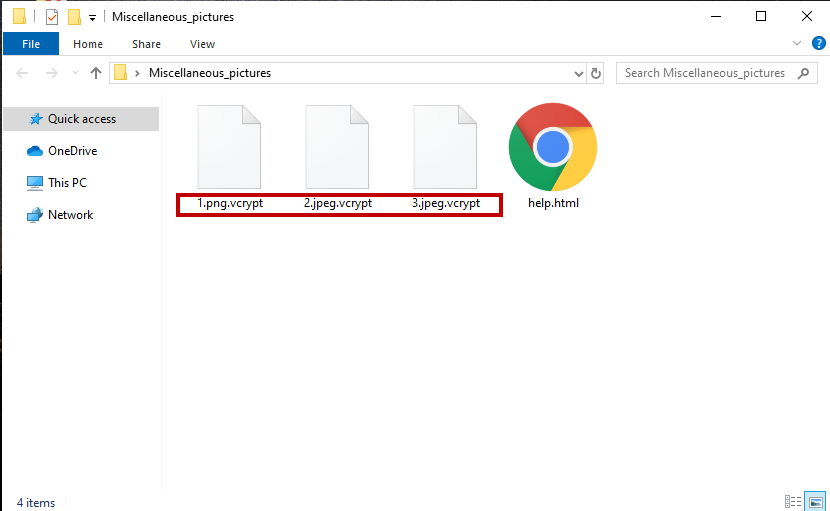
Once the VCrypt Virus has encrypted your files it will leave a help.html file.
A relatively simple extortion scheme is what stands behind the behavior of this ransomware infection. The cybercriminals who have control over VCrypt use it to encrypt digital files without the knowledge of users and then demand a money transfer in order to provide the decryption key for the applied file encryption. Normally, the malware is programmed to scan the entire computer and to detect the files that are used the most or could be of great value for the victim in order to make it more pressing to pay the ransom money. These could be images, personal videos and audios, archives, databases, digital documents, etc. Once they become encrypted with a complex code, their file extension may be changed to an odd one that no program can recognize. If you want to access them again, the hackers offer you to “purchase” a specially generated decryption key from them. They typically place a notification with ransom payment instructions but the payment they demand is not in regular currency but in cryptocurrency. This is because if you send the hackers the money they request in cryptocurrency, the authorities will not be able to verify exactly where the transfer is going and who receives it which gives the crooks anonymity. On this page, however, we will provide you with some alternatives to the ransom payment and a detailed removal guide that explains how to remove VCrypt from your computer.
The VCrypt virus
The VCrypt virus is a new ransomware variant that targets digital data and encrypts it. The cybercriminals behind the VCrypt virus demand a ransom payment for the decryption of the encrypted data and place a threatening message on the victim’s computer screen.
Every year there are millions of new variants such as VCrypt that extort money from innocent web users through the above-described blackmail scheme. If you have already been targeted by this particular cryptovirus, it is really important not to panic and fulfill the hackers’ demands out of fear and frustration because there is no guarantee that they will provide you with a decryption key. Instead, what we suggest you do first is to explore alternative ways to remove the infection and recover your files without paying a ransom.
The VCrypt file encryption
The VCrypt file encryption is a complex code used to render digital files unreadable. The VCrypt file encryption code can get applied to common file formats and cannot be reversed without a decryption key.
If you have been seeking a way to recover your computer and your files from the ransomware’s attack without paying a ransom, the first thing you should do is to remove the cryptovirus which can be done either manually or with the help of professional removal tool. Next, you can give the free file-recovery suggestions in the guide below a try or use personal backups and professional help to minimize the data loss as much as possible.The easiest way to protect yourself from a ransomware cryptovirus such as VCrypt is to make backups of your most important information regularly and store these backups on a separate drive that is not linked to the Internet or your computer.
SUMMARY:
| Name | VCrypt |
| Type | Ransomware |
| Detection Tool |
Remove VCrypt Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment