This page aims to help you remove .Vesad Virus Ransomware for free. Our instructions also cover how any .Vesad file can be recovered.
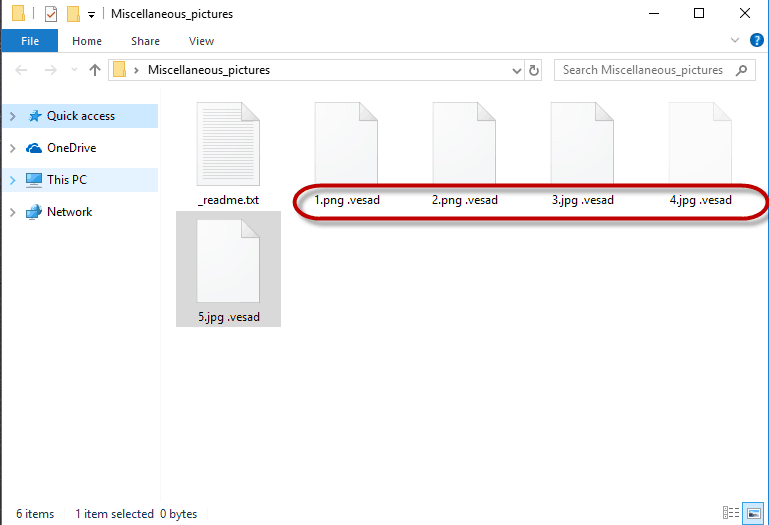
.Vesad virus is another strain from the Stop Ransomware family. It will modify the extension of your files to .Vesad
After the ransomware encrypt your files, it leaves a _readme.txt file with instructions to follow:
ATTENTION!
Don’t worry my friend, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https ://we .tl/t-pPLXOv9XTI
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
If you have landed on this page because you have received a strange ransom-demanding message from a malware named .Vesad, then stay with us. The software piece you are dealing with is a Ransomware cryptovirus that has the ability to infect a computer through stealth and apply a complex encryption to all the files that are stored on it. Once the device is compromised, .Vesad automatically starts the encryption process in the background of the system and locks the files, one by one, thus preventing their owner from accessing them. The malware also generates a special decryption key which it stores on the server of its criminal creators. The moment all the targeted data gets secured with the complex encryption code, the hackers ask for a ransom payment in exchange for sending you the decryption key. They normally request the payment in bitcoins or another type of cryptocurrency, as those are very difficult to trace and this is what ensures that the hackers stay anonymous. The use of cryptocurrency also means that in pretty much all cases of infection with Ransomware, the money sent to the hacker is gone for good and it wouldn’t matter if the victim actually gets back their files.
How can .Vesad infect your computer?
As a typical Ransomware cryptovirus, .Vesad and .Muslat , .Heroset, .Pidon can sneak into a device through multiple ways and operate in the infiltrated system without the user’s awareness. One of the most widespread methods is the use of fake e-mail messages that are used to carry misleading links and infected file attachments. Clicking on the malicious link or downloading the attachment results in an infection with the malware. Another way is through a malicious web page or an ad that, upon entering, automatically downloads the virus.
In many cases, apart from individual users, big companies are also a common target of threats like .Vesad because they tend to pay the ransom more quickly as they have much more to lose – they risk losing their clients’ personal data, accounting reports and other sensitive information. Other common targets are public organizations, which have systems that can be easily hacked and because of the importance of those organizations, the ransom typically gets paid as potentially the quickset method of restoring the data.
What you must do if .Vesad has your files under its encryption?
Leading security experts and professionals advise the companies and individuals who suffer from a Ransomware attack to not pay the ransom and to instead seek legitimate alternative methods to deal with the infection. This is mostly because there is no guarantee that the encrypted files will be recovered and decrypted even if the victims strictly fulfill all the hackers’ demands. There is a high chance that the crooks may simply disappear with the money and never send a decryption key to the users. Besides, sometimes, even that key may prove to be ineffective at reversing the applied encryption code. For these reasons, in the case of some viruses like .Vesad, it is advisable to seek ways to remove the infection and recover the data through alternative methods that don’t involve paying money to some anonymous hackers. For instance, you can start with taking a look at the instructions in the Removal Guide below. The steps there focus on removing the Ransomware from your computer, as this is the first thing you should concentrate on. There is also a file-recovery section added to the guide which contains suggestions on how to potentially restore some of your files for free.
SUMMARY:
| Name | .Vesad |
| Type | Ransomware |
| Detection Tool |
Remove .Vesad File Virus Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment