This page aims to help you remove Vesrato for free. Our instructions also cover how any Vesrato file can be recovered.
Ransomware viruses have been around for some time, but it wasn’t until the last few years that this malware category gained some serious momentum. Millions of new and sophisticated versions of Ransomware are getting published each year, and the numbers keep growing exponentially. One of the latest versions is Vesrato, and we’ve received quite a few reports from our readers about it. Just like most other Ransomware viruses out there, Vesrato secretly encrypts the files stored on the infected computer, and then places a ransom-demanding message, telling the user that the only way they could get their data restored is through the payment of a ransom. The attack of such malware is an extremely uncomfortable experience, where your most valuable information is kept hostage, and you cannot open or use it unless you pay money to some anonymous hackers. So should you do in the event of such an infection with Ransomware?
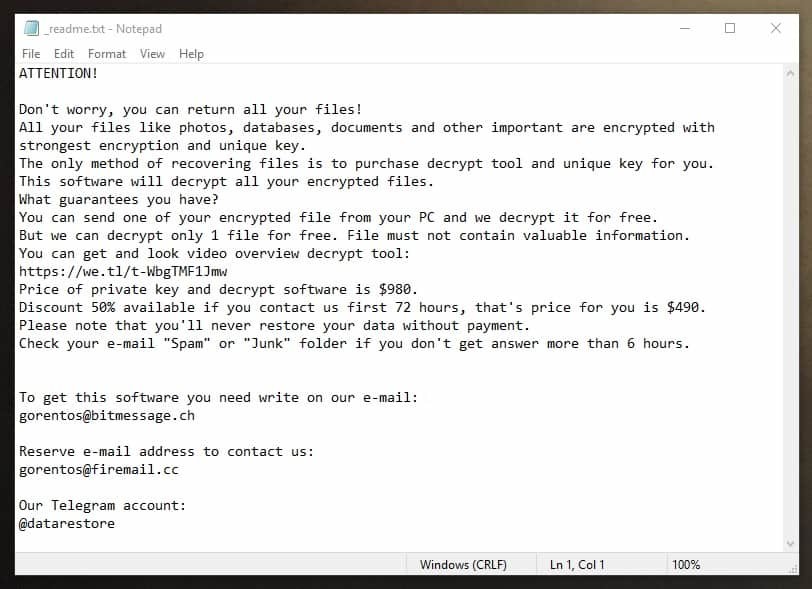
The .Vesrato virus
The .Vesrato virus is a strain of the Stop Ransomware primarily targeting users in North America and Indonesia. The .Vesrato virus displays the following Ransom Note to victims:
One of the most essential things is to remove the malware, and with the help of our detailed removal guide below, we can show you exactly how to do that. There are also some steps to restore your files from system backups, which you will find in a special file-recovery section. But please, take a few minutes to first read the information in the next lines before starting the removal process.
Ransomware is considered one of the most harmful and dangerous types of viruses in existence, and there are a number of important reasons for that. One of them is the fact that those viruses happen to be incredibly hard to detect once they sneak into your system. Unfortunately, most antivirus programs do nothing to stop this type of malware because of the encryption processes that is being used.
Here, it is important to mention that the encryption is not a damaging method, and it effectively serves as a means of protecting important data from people parties who aren’t authorized to access it. We’re using encryption daily to protect our financial details, and other sensitive digital information. Yet, people with malicious intentions have found a way to use it for blackmailing purposes, by secretly locking down the users’ information, and by extorting money from them in exchange for the liberation of the encrypted data.
The .Vesrato file encryption
If you see . Vesrato files as in the picture below and they have fully taken over your folders, then the encryption process has been completed. If you see a .Vesrato file but not all of the files have the extension, immediately shut down your computer and enter in safe mode.

Users may have the ability to stop this blackmailing scheme, though. What one can do to counter any of the most dangerous Ransomware types out there is to first refuse to pay the requested ransom. For one, there is no assurance that you will be given access to your information regardless of how strictly you may comply with the ransom demands. The hackers behind Vesrato or Nasoh may not send you a key for decryption or they may ask you for more money after the initial payment. This is often the case for many victims out there. Secondly, even if you obtain a decryption key, this does not necessarily mean that you will decrypt your information effectively. The key may not work, and also you’d still have the malware present in your computer on your hands. This is the reason why we typically suggest that our readers to focus on the removal of Vesrato, as this will prevent further harm. As far as your files are concerned, you could use file backups if you have any, or give a try to the file-recovery methods shown in the guide, as potential alternative means of restoring your files.
SUMMARY:
Vesrato Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Reply