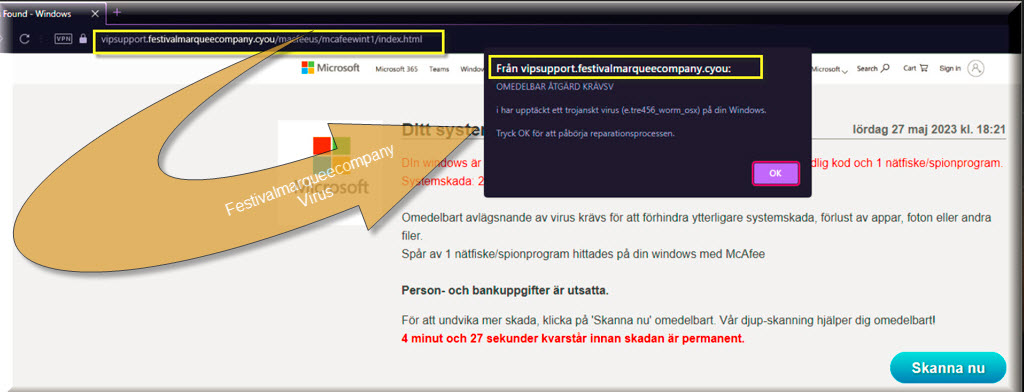
Vipsupport.festivalmarqueecompany.cyou
The Vipsupport.festivalmarqueecompany.cyou is a form of malware that aims to take over your browsers, change the addresses of their starting page and search engine, and use them to promote certain sites, products, or online services. The Vipsupport.festivalmarqueecompany.cyou itself is not damaging, but could make your system vulnerable.
Regardless of what software problem a given user may be struggling with, the first step towards dealing with the issue is understanding what’s causing it. In this particular post, we will focus on a very common problem that many users have with their browsers and that is when the browser is getting swarmed with unpleasant and obstructive advertising materials that are making it difficult to surf the Internet in peace.
Here, however, we aren’t talking about ads and page redirects that are coming from different websites. Instead, we are referring to the advertising materials spammed by so-called browser hijacker apps. a category of software the representatives of which are able to infiltrate most popular browsers (ones like Chrome, Edge, Firefox, and so on) and turn them into an ad-streaming platform by making changes to their search engines and homepage addresses and by showing all sorts of pesky advertisements in their windows and tabs.
This type of problem is, as we already said, really common and many customers do not even realize that the cause behind it is a browser hijacker software component. Now, if you have a similar issue with your browser and do not know how to put an end to the continuous generation of pop-ups, banners, page redirects, pop-unders and other intrusive content, know that the most important step to take is to uninstall the unwanted software that has latched onto your browser and that is triggering all of the unpleasant activities.
There are actually thousands of browser hijackers out there but since you have landed on this particular article, you likely have the Vipsupport.festivalmarqueecompany.cyou hijacker on your computer. Below, you can find detailed removal steps and a professional removal tool both of which should allow you to make quick work of Vipsupport.festivalmarqueecompany.cyou and rid your computer and browser of its presence.
Careful with the ads and the other commercial messages
You surely don’t want to land some malicious ransomware, spyware or Trojan horse virus on your computer, yet this is exactly what could happen if you accidentally open some misleading or fake advert on the Internet. Sadly, with a hijacker in your browser, the number of ads you get exposed to on your computer will drastically increase, meaning that the chances of running into some unsafe piece of online content will also go up.
Now, Vipsupport.festivalmarqueecompany.cyou or Festival Marquee Company itself is not a malicious virus program or some Trojan horse or ransomware cryptovirus. It’s an advertising tool that is supposed to make money through its ads. The problem is that you can’t really trust each and every advert that comes your way and it is always safer to simply keep away from the random commercial messages that get spammed on your screen. In fact, it’s best if you simply get rid of the app that is triggering the ad generation which is why we once again remind you to make use of the guide on this page and eliminate Vipsupport.festivalmarqueecompany.cyou for good.
SUMMARY:
| Name | Vipsupport.festivalmarqueecompany.cyou |
| Type | Adware |
| Detection Tool |
Remove Vipsupport.festivalmarqueecompany.cyou
If you can’t wait to remove Vipsupport.festivalmarqueecompany.cyou from your browser, we suggest you first give a try to the following instructions:
- Select More Tools (or Add-ons) from the list of options in your browser’s main menu.
- Open the Extensions tab/submenu.
- Search for Vipsupport.festivalmarqueecompany.cyou or any other potentially unwanted extension that you feel is hijacking your search results.
- Remove the unwanted extensions by clicking on the Trash Bin/Remove button next to each of them.
- Start a new browsing session to test the browser’s performance without any unwanted extensions.
If the issue has been handled and you are satisfied, no more action is required. However, if Vipsupport.festivalmarqueecompany.cyou continues to disturb your web surfing experience with auto-redirects and unexpected pop-up advertisements, then use the detailed removal guide below to get rid of any hijacker-related components that may have been installed on your system.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.

As a first step, please make sure to save this Vipsupport.festivalmarqueecompany.cyou removal guide to your bookmarks since you’ll need to return back to it several times until you complete all the instructions in it.
Next, reboot your computer in Safe Mode by using the instructions from this link and then get back to this page and proceed to the next step in this guide.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL, SHIFT and ESC on the keyboard at the same time to launch Task Manager, then click on the Processes Tab on the top of the window.
Look for processes that may be connected to Vipsupport.festivalmarqueecompany.cyou. Search specifically for processes with strange or unusual names and those that use a lot of CPU and Memory for no apparent reason in addition to processes named directly after the browser hijacker.
Right-click on anything strange that catches your eye and select Open File Location.

Then use the powerful free online virus scanner below to check the files that you find there for hijacker-related code.

In case that the scan detects files that get flagged as potentially dangerous, go back to the Task Manager’s Processes tab, right-click on the suspicious process and choose End Process or End Process Tree to stop the process from running.

Software bundling is often used to introduce programs like Vipsupport.festivalmarqueecompany.cyou to a user’s system. Therefore, it’s possible that the new application that you have installed recently might have came along with a browser hijacker in its installer. If this is the case, you may need to remove that software from the Start menu >> Control Panel >> Programs and Features >>Uninstall a Program.
Look for suspicious apps that might be related to Vipsupport.festivalmarqueecompany.cyou or other potentially unwanted programs that have been installed without your permission and remove it/them as well.
After you are done with that, go back to the Start menu, type msconfig in the search field and hit the Enter key from your keyboard.
Remove the tick from the checkboxes of any startup items that may be relevant to your browsing issue in the Startup tab in System Configuration. Click OK to save your changes and then close the window when you’re done.


Next, press Windows key and R from the keyboard and copy and paste the following in the Run box that pops on your screen:
notepad %windir%/system32/Drivers/etc/hosts
Click the OK button and this should immediately open a Notepad file named Hosts.
Scroll the text of the file and find Localhost. Then check if there are any strange IP addresses like those shown in the image below:

Close the file if you don’t notice anything odd. Nonetheless, if you see any unusual IP addresses, please copy them and send them to us in the comments section below so that we can investigate and give you advice on what to do.
Next, go back to the Start menu button bottom left, click it and search for Network Connections in the search bar. Open the result and carefully repeat the following instructions:
- Right-click on the Network Adapter that you are using and select Properties from the pop-up menu.
- In the Properties window, use the cursor the highlight Internet Protocol Version 4 (ICP/IP) and click the Properties button at the bottom.
- In the next step, make sure that Obtain DNS server address automatically is checked with a dot, then click on Advanced.
- To delete any rogue DNS, tap on the DNS tab in the Advanced TCP/IP Settings window’s and remove anything that has been added there. When you are done, click OK and exit the window.


In this fifth step, we’ll go through the specifics of removing Vipsupport.festivalmarqueecompany.cyou from all of your system’s browsers.
Open Properties by right-clicking on the browser’s shortcut icon.
NOTE: We’ll show you how to do it in Google Chrome, but the steps are the same in Firefox and Internet Explorer (or Edge).

Select the Shortcut tab in the Properties window and check if anything has been added after .exe in Target. If you detect that something has been added, remove it as shown on the image:

![]() Remove Vipsupport.festivalmarqueecompany.cyou from Internet Explorer:
Remove Vipsupport.festivalmarqueecompany.cyou from Internet Explorer:
To get rid of any traces linked to Vipsupport.festivalmarqueecompany.cyou in Internet Explorer, you first need to open it, click ![]() and then select Manage Add-ons.
and then select Manage Add-ons.
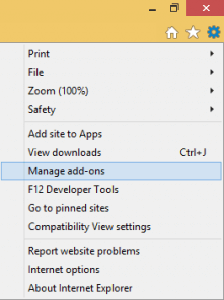
Disable any questionable add-ons that appear in the list of extensions.
After that, go to ![]() once again, click the Internet Options and change the URL of the homepage (if hijacked), then click on Apply.
once again, click the Internet Options and change the URL of the homepage (if hijacked), then click on Apply.
![]() Remove Vipsupport.festivalmarqueecompany.cyou from Firefox:
Remove Vipsupport.festivalmarqueecompany.cyou from Firefox:
In Firefox, the instructions are almost the same. Just choose Add-ons —-> Extensions from the main menu icon top right and then remove any extensions that seem questionable

![]() Remove Vipsupport.festivalmarqueecompany.cyou from Chrome:
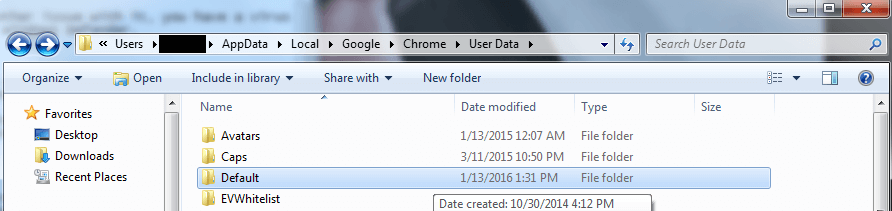
Remove Vipsupport.festivalmarqueecompany.cyou from Chrome:
In Google Chrome, you’ll need to keep the browser closed and manually navigate to this location:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data.
Find the Default folder inside User Data and right-click on it. Select Rename and change the name of the folder to Backup Default, then save it that way. After that start the browser to check how it behaves.

In the final step, launch the Registry Editor by typing Regedit into the Start menu search bar and clicking on the editor’s icon in the results.
After that, press CTRL and F at the same time and type the name of the hijacker in the Find box to quickly search for it. Start a search, and then remove anything that has the same name.
If nothing is found, you may use the left panel of the registry editor to navigate to these system locations and manually check them:
- HKEY_CURRENT_USER—-Software—–Random Directory.
- HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
- HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
Check each of these locations for new files and folders, and remove anything suspicious you find. Let us know if you have any questions or concerns in the comments below.
In case that you are not completely confident that the registry entries you find should be removed, don’t make any changes on your own. Instead, please scan the system with the professional removal tool linked on this page, or use the free online virus scanner to check the files that look suspicious.

Leave a Comment