This page aims to help you remove VLC Updater Malware. Our removal instructions work for every version of Windows.
VLC Updater
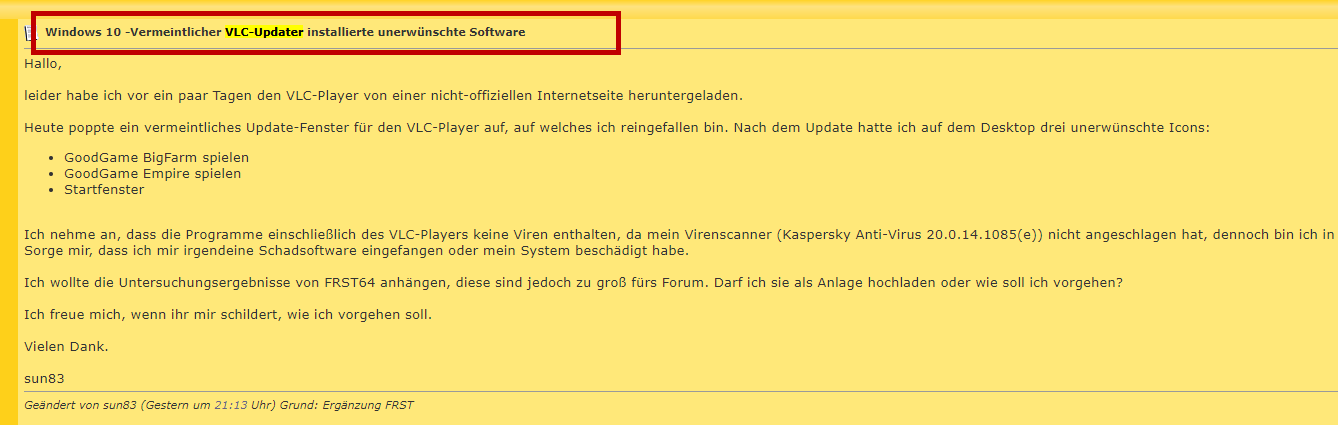
VLC Updater is a Trojan Horse malware program – a type of malicious software that tricks the users about its true purpose by being disguised as a seemingly harmless piece of data. Threats like VLC Updater are often used for data theft and Ransomware distribution.
If the insidious VLC Updater Trojan virus infection has infiltrated your system there’s really no time to lose as this threat may cause all kinds of unpredictable issues in your computer that could be related to loss of data, financial theft, and even espionage and stalking. The good news is that you’ve been able to spot the malware and you now know what you have on your hands. All that remains to be done now is to remove the threat from the infected computer. Getting rid of a Trojan isn’t always an easy task and in some cases, you may need the help of a reliable anti-malware tool to fully achieve it. Fortunately, there is a set of manual instructions below which you can use to remove the virus and if for some reason they don’t fully work in your case or if you don’t think you can complete all the steps, there is a recommended security tool inside the guide which is tested against this sort of infections and can help you locate and remove all files and system entries related to this Trojan Horse.
The VLC Updater Malware
If Vlc-updater.exe is in a “C:\Users\YOUR_USERNAME” or “C:\Documents and settings\YOUR_USERNAME\” or type %HOMEPATH% in Explorer address bar the security assessment is 100% hazardous.It is a file with no intelligence about its developer. Vlc Updater Malware is able to record keyboard and mouse inputs and check applications.
As we said, it is good news that you are aware of the presence of VLC Updater in your machine. Many computer users that have a Trojan in their systems have actually no idea about the ongoing infection. There are many different tactics that Trojans are known for employing in order to stay undetected in the computer for longer periods of time. For instance, some Trojans are known for ending and even prohibiting certain processes. Often those are processes related to the antivirus programs in the computer – the Trojan may end their processes and may block the user from starting the antivirus again. It’s even possible that the Trojan doesn’t allow you to install new security programs, in which case your only remaining option would be to use the manual instructions from the guide.
Another stealth tactic that allows viruses like VLC Updater to remain unseen is the disguise they use for their own processes and files. Most Trojans are known for giving their processes the names of system-related ones that no one would suspect of coming from a malware program. The same is done for the files of the Trojan – they could have the names of OS-related files or they may be hidden deep inside system folders. All of this makes the timely detection and removal of VLC Updater and other similar infections quite difficult, not to mention the high likelihood of deleting something that is actually coming from the OS while trying to remove the Trojan data and system-entries.
How harmful is VLC Updater
Currently, we cannot tell you with certainty what the goal of this malware is but you must know that the Trojans, in general, are known for stealing data, abusing the system’s resources, and spreading other threats like Ransomware. Only the timely removal of the Trojan can prevent those things from happening to you.
SUMMARY:
Remove VLC Updater Malware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Reply