This page aims to help you remove Vonteera Adware. These Vonteera Adware removal instructions work for Chrome, Firefox, Internet Explorer and Safari, as well as every version of Windows.
If your computer has been infected with Vonteera Adware then you are dealing with a threat commonly referred to as Adware. This is basically a type of Malware that specializes in the display of advertisements, or Ads for short. You are going to see a lot of these on every page you open. It’s also possible that new tabs will be created without your permission and they will either hold Ads or a search bar that wields Ads when used. Another variation will make certain keywords turn into hyperlinks and pop-up an Ad when your mouse is hovered over. Whatever the type of Ads you see is it’s never a good idea to click on them. Ignore them and uninstall Vonteera Adware as soon as possible.
Methods used by Vonteera Adware to infect computers
Adware typically spreads around the internet by using several different popular methods. They are listed below, but please keep in mind that there are always improved upon and changed. Always be on your guard for any similar tricks.
- Software bundles – by far the most common and popular method. Software bundles are installers for programs that contain multiple programs inside. All the extras will be installed without your explicit permission if you select the Quick/Default installation option. For this reason we strongly encourage our readers to always use the Advanced installation option instead. When used it will give a detailed description of the number of items that will get installed and you will have the option to get rid of everything but the main program, which you want anyway.
- On-line Ads or Ads by other Adware programs – also common cause. Internet sites are often filled with Ads that promise programs with useful functionality for free. Unfortunately those are not really free and sometimes don’t even serve a purpose – enter Vonteera Adware. Avoid downloading any software offered to you like this.
- Email bombs – as old as the internet itself these bombs can install all kind of malicious programs on your machine. Recognize the dangerous attachment by its file extension – Invoice.PDF or Invoice.DOCX might be a real file, Invoice.EXE is definitely a virus.
- Torrent sites and online storage sites also frequently spread virus-like applications. When visiting such a site be careful – there will often be multiple Download buttons to click on and only one of those will be real (if there is even one). If you click on a fake one you will get a file to download. This file will match the file you want, but in name only. The contents will actually be a virus.
SUMMARY:
| Name | Vonteera |
| Type | Adware |
| Detection Tool |
Vonteera Adware/Trojan Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
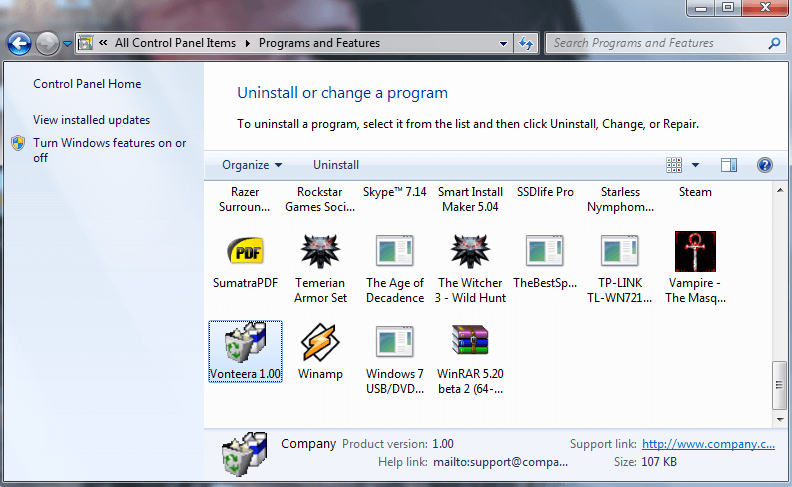
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Comment