Vpn3protectplus
Vpn3protectplus infects the Safari and Chrome browsers on iPhone and iPads. Vpn3protectplus is compatible with all the latest iOS versions and becomes instantly noticeable after it’s installed on the device.
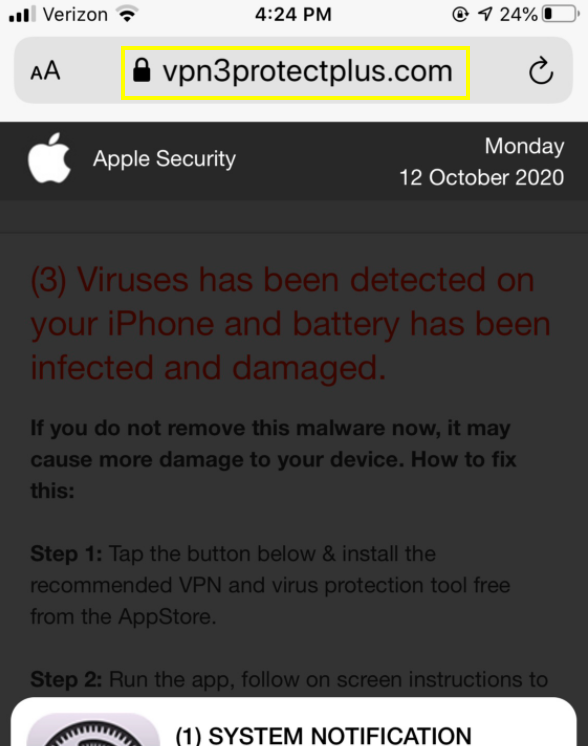
The Vpn3protectplus Virus will display pop up ads.
Namely, you will start noticing large quantities of popups and banners during your web browsing sessions. And very often it will be quite difficult to avoid tapping on these ads, which will constantly result in page redirects to various sites trying to sell you some type of product or service.
In addition, software like Vpn3protectplus is known as browser hijackers and the reason for that is that these programs have a strong tendency to mess with the original configurations of the infected browsing applications. Thus, they can, for instance, replace the default search engine with a different one. And they might even set it as the new browser homepage, as well.
Furthermore, browser hijackers like Vpn3protectplus are notoriously persistent and as long as they are present on your iOS device, they will be in charge of your browser and will override any changes you try to make to the settings. This is generally the reason that most people choose the remove these applications from their iPhone or iPads. And to assist you with this task, we have designed a special removal guide which you can find on this page.
If you’re worried about whether or not Vpn3protectplus may in some way damage your system – it won’t, at least not directly. What can happen is that as a result of its aggressive advertising campaigns, your device may potentially be exposed to malicious threats such as Trojans and ransomware viruses.
SUMMARY:
| Name | Vpn3protectplus |
| Type | Browser Hijacker |
Vpn3protectplus Removal
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
- Locate and clean up your phone’s calendar events if they are infected.
- Find browser extensions related to the threat and how to remove them.
Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment