*Vvew is a variant of Stop/DJVU. Source of claim SH can remove it.
Vvew
Vvew is a ransomware infection that functions as a cryptovirus. Cryptoviruses like Vvew are probably the most problematic ransomware sub-category, as they are highly advanced threats that employ data encryption as a means of rendering their victims’ files inaccessible.
One of the best methods you can use for data protection is encrypting your valuable files so that no one else is able to access, modify or use your data. However, this same method of encryption is what makes many unfortunate users incapable of accessing their own private files if a ransomware cryptovirus has infected their computer.
The Vvew virus
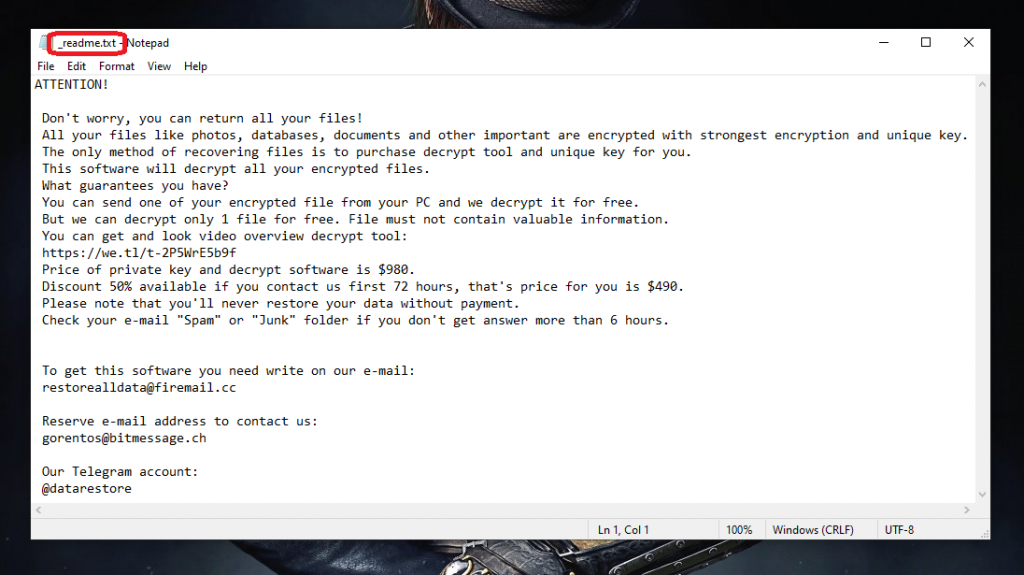
Once the Vvew virus enters the targeted PC, it places its complex encryption on most (if not all) of the files that it finds on the machine’s hard drive. After this, the Vvew virus displays a message in which the hackers responsible for the malware attack state their demands.
Those demands typically involve the payment of a certain amount of money – the users are supposed to pay a ransom if they are to restore their personal data to its previous accessible state. In most cases, there are some specific instructions that the malware victims are supposed to follow when paying the ransom.
For instance, the money is typically required in the form of some cryptocurrency and is supposed to be sent to a certain cryptowallet. For some of you, going for the payment may actually seem like an easy way out of this, especially if the requested sum isn’t that significant. However, we must remind you that you can’t really trust the hackers. If they decide to, they may simply keep the money you send them without really releasing your files. Because of this, alternative solutions and methods such as the ones below is what we would advise you to go for instead.
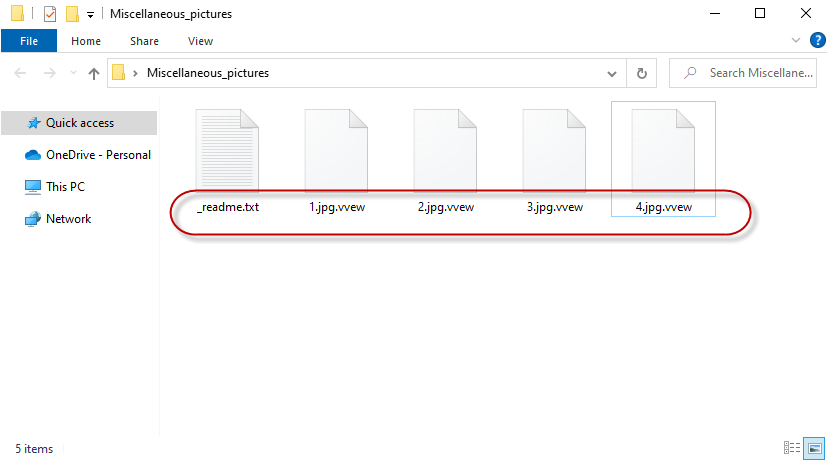
The Vvew file encryption
A major problem with the Vvew file encryption is that it is new and complex and there is still not too much information about it. This means that the alternative methods that may work against other ransomware cryptoviruses may not be as effective against the Vvew file encryption.
Still, if Vvew, Ooxa or Oori is currently on your PC, blackmailing you for the access to your data, we still believe that paying isn’t really the best option you have. Instead, what we would advise you to do is follow the instructions from the guide on this page and remove the infection with their help. After you do that, you can try some alternative data-recovery options. We have some file-restoration suggestions in a separate section of our guide that you can use so be sure to give them a go. Again, we don’t want to give any unrealistic promises but it’s still better to first exhaust all other options before considering paying the hackers behind Vvew.
SUMMARY:
| Name | Vvew |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
*Vvew is a variant of Stop/DJVU. Source of claim SH can remove it.
Before beginning the removal
Before beginning the completion of the steps below, it’s recommended that you first read the following notes and bear them in mind during the removal.
- Ransomware viruses like Vvew are able to encrypt data located on external devices that are currently linked to your computer, so it’s essential that you disconnect any such devices as soon as possible.
- It’s a good idea to disconnect your PC from the web and keep it disconnected throughout the completion of the guide in order to prevent Vvew from potentially attempting to communicate with its servers.
- Paying the ransom is highly inadvisable, yet, if you think this is your best option and want to go for it, then we recommend holding off the completion of the guide until the payment is completed, and you’ve hopefully received the decryption details.
- Sometimes, it may seem that the virus is gone from the computer after the encryption of your files is complete. Even in those cases, however, it’s still strongly advisable to perform the guide in order to ensure that there’s truly nothing left from the Ransomware.
Remove Vvew Ransomware
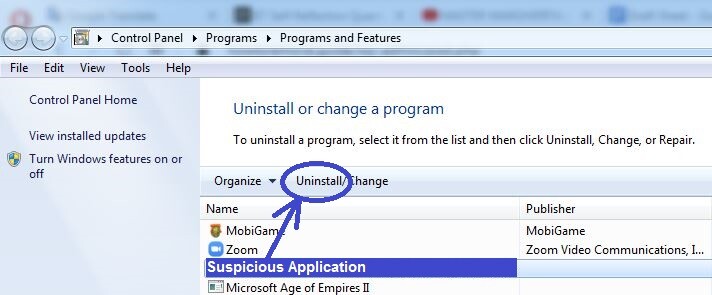
- To remove Vvew, you need to start with cleaning the Programs & Features list from any rogue and potentially harmful items by uninstalling them.
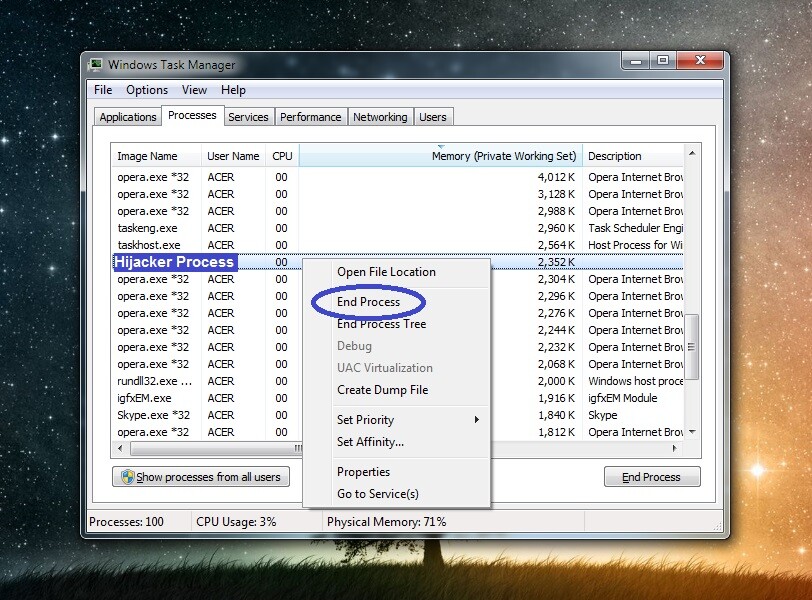
- After that, you should check the Task Manager for questionable processes and quit any such processes that you may find.
- Next, go to the following folders and delete from them any malware-related data. The folders are: AppData, LocalAppData, WinDir, ProgramData, and Temp.
- Last but not least, revoke any rogue changes made to the system’s Startup items list, Hosts file, Task Scheduler, and Registry.
This is only a brief rundown of the entire removal process. For further details, we recommend reading the in-depth removal steps we’ve shown below.
Detailed Vvew removal steps
Step 1
For this first step, you need to open the Start Menu, type in it Programs and Features, and click the first result. Then scroll down, look through the list of installed programs, and be sure to uninstall any items that seem suspicious, unwanted, and rogue. It would be a good idea to sort the Programs and Features list by date, so that the most recent installs are shown at the top, because if there are any harmful programs currently on your computer, they’ve most likely been installed relatively recently.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Vvew is a variant of Stop/DJVU. Source of claim SH can remove it.
Now go to the Task Manager by pressing Ctrl + Shift + Alt and then click on the Processes tab. In it, sort the entries by their Memory or CPU usage and look at the most resource-intensive items. If, among them, you see any unfamiliar entries with questionable names that don’t seem linked to any of the legitimate programs that you have on your computer, be sure to look up the names of those processes and see if there’s any information on the Internet about them being potentially harmful. Also, go to the File Location folder of each such process by right-clicking on it and selecting Open File Location, and then scan each file in the folder that opens using the following free online malware scanner.


If, after you research any suspicious processes in your Task Manager, and after you scan their files for rogue code, one or more processes turn out to be potentially harmful, right-click them, click End Process, and then delete their File Location folders.
Step 3
Restart your computer and then boot the PC into Safe Mode – this should help you with the rest of the guide by preventing Vvew from restarting any of its rogue processes and thus making its removal more difficult.
Step 4
*Vvew is a variant of Stop/DJVU. Source of claim SH can remove it.
Search for Folder Options in the Start Menu search box, open the Folder Options settings, and go to View. There, make sure that the Show hidden files, folders, and drives setting is enabled, and then select OK.
After that, type “%AppData%” in the Start Menu, hit Enter, sort the items in the newly-opened folder by creation date, and delete everything created since the virus infected your computer.
Next, do the same thing with these other four folders:
- %WinDir%
- %LocalAppData%
- %ProgramData%
- %Temp%
Once you go to the Temp folder, you will need to delete everything that’s in it. Since there would typically be thousands of items there, it’s easier to simply press Ctrl + A to select everything and then press Del to delete all items.
After that, remember to go to your Recycle Bin and empty it to make sure that all unwanted and/or rogue files are fully deleted.
Step 5
Once again, use the Start Menu search to find each of the next items, open those items, and then complete the respective actions we’ve shown below.
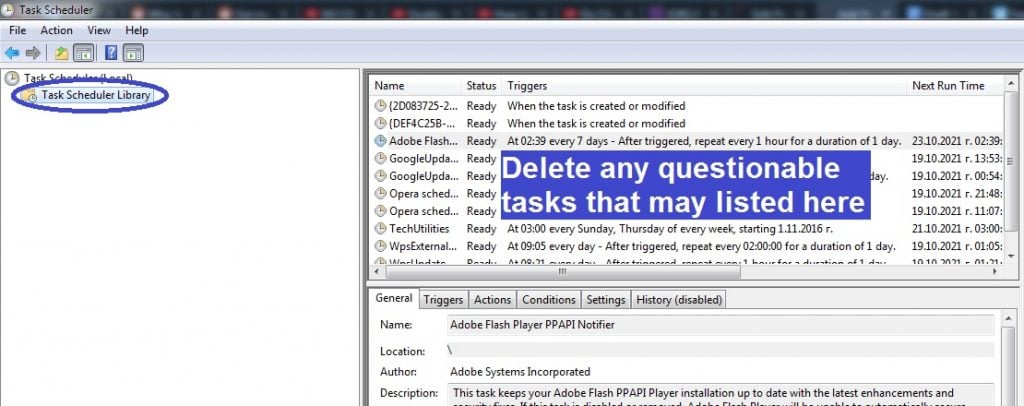
Task Scheduler – Once the Task Scheduler shows up on your screen, click its Task Scheduler Library folder in the top-left, then look at the entries shown in the right panel, and delete anything you think may be linked to Vvew.
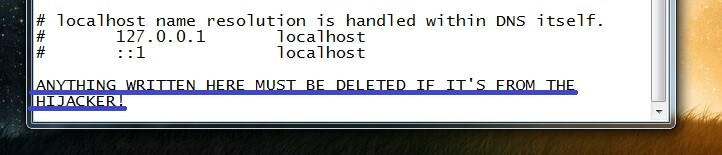
notepad %windir%/system32/Drivers/etc/hosts – This will open a notepad file named Hosts – your task is to see if there’s anything written at the bottom of the file, right below “Localhost“, copy what may be written there, and send it to us in the comments. After we see your comment, we will let you know if the text you’ve sent us from your Hosts file needs to be deleted.
Msconfig – Go to the Startup tab and, if there is an Open Task Manager option there, click it. Next, once you are at the list of Startup items, look for anything unfamiliar or questionable, disable it, and then click on OK.
Regedit.exe – To access the Registry Editor, first click on Yes to provide your Admin permission. Once the Editor opens, press Ctrl + F, then type the name of the virus in the search bar that shows up, and click Find Next to look for related items. If an item gets found, delete it and search again to see if there are more rogue items.
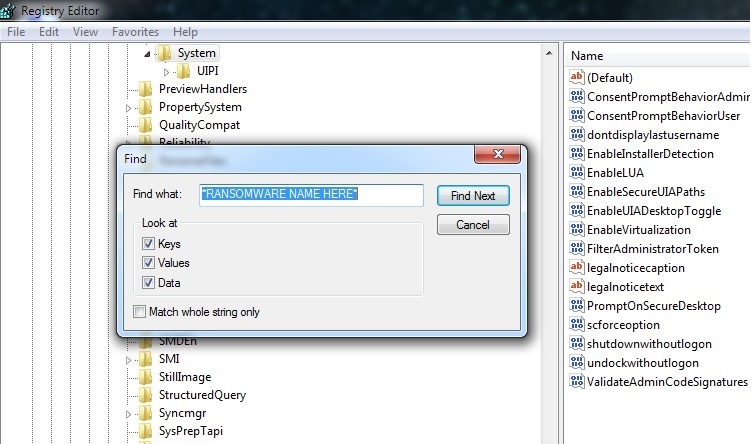
Once you delete everything related to Vvew, manually find and open the following three locations in the left panel of the Registry Editor.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
In each of those locations, look for entries with questionable and unusually long names that seem randomly generated. If you come across any such items, let us know in the comments, and we will soon reply to you, telling you if you’d need to delete those items.
Is Vvew still there?
In case the virus is still on your computer, it’s recommended that you make use of the specialized anti malware tool that can be found linked on the current page, as it can deep-scan your system and automatically eliminate any remaining rogue files and settings. Additionally, it can also keep your computer secure in the future and fend off any incoming malware threats, preventing them from entering the system.
Also, if you are not quite certain whether the virus is still there, we remind you about our free online malware scanner that you can use to test suspicious files on your system and see if there’s any malicious code contained in them.
How to decrypt Vvew files
To decrypt Vvew files, you’ll need to a unique private key that matches the public key that has been used to lock your files. You may be able to acquire the needed private key and decrypt the Vvew files using a specialized free Ransomware-decryption tool.
Note, however, that before you make any attempts to restore your files, you must be certain that the Ransomware is no longer present on your computer. If you are sure that the malicious program has been removed, you can use the next instructions to try to recover your locked data.
Bear in mind that, for the next steps to work, you will need one or, preferably, several file pairs, where one of the files in each pair is encrypted, and the other one is an accessible version of the same file. To form such file pairs, look for accessible copies of your encrypted files in external drives, cloud storages, smartphones, tablets, email accounts, other computer, etc. If you manage to form several such file pairs, you can try the next steps to hopefully recover your data.
- Go to this link, select the first of the Choose a file options, navigate to an encrypted file from one of the pairs and open it.
- Next, select the second Choose a file button, navigate to the accessible file version from the same pair, and load it onto the page.
- After that, click Submit and wait as the key-extraction process commences. If the process is unsuccessful, try again with a different file pair.
- Once you manage to extract a decryption key, visit this link and download the decryption tool you will find there.
- When you download the tool, right-click it, click Open as Administrator in the context menu, give your Admin approval to run the program, and then accept the terms of use.
- Finally, once the tool opens, navigate to a drive or folder where there are encrypted files and select the Decrypt button. Wait for the decryption to complete and see if your files have been unlocked. If some or all of the files don’t get unlocked, repeat the entire process using a different pair of files.

anybody knows how to decrypt files which are the effected from VVEW virus
Hi madhawaka vanderslott,
at the bottom of the guide you can find helpful links that will lead you to a decryption software. Follow the steps and you will be fine.