*Source of claim SH can remove it.
W4SP Stealer
W4SP Stealer is a malicious piece of software that operates in secret and starts harmful processes inside the computer it manages to infect. Online security experts classify W4SP Stealer as a Trojan horse and advise users to immediately remove it from their system.
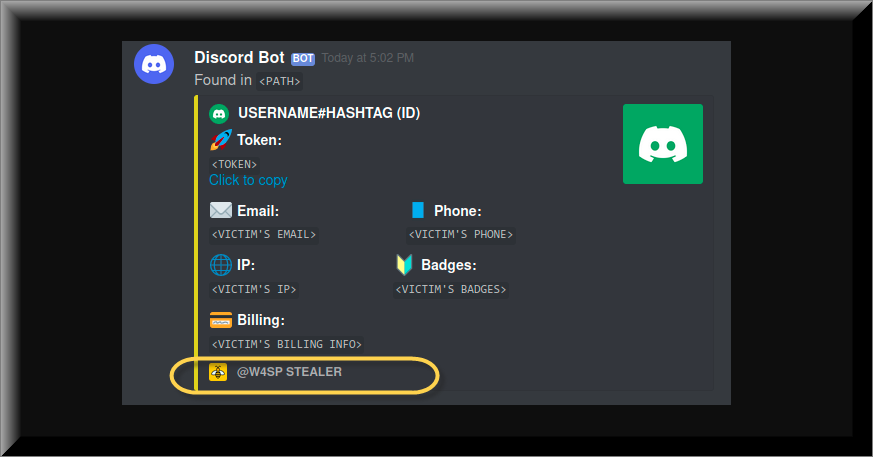
In general, Trojan horse viruses are very versatile and the criminals who create them can program them to perform a lot of different and unrelated illegal tasks. For instance, some Trojans, like this and Novpopen.exe are set to target the data that you store on your system and steal it, others may try to spy on your online and offline activities. Many Trojan-based threats may secretly execute malicious processes in the background of the system or invite other harmful programs such as ransomware, spyware, rootkits and viruses inside your compromised device. Unfortunately, there is nothing that could indicate to you what type of harm precisely to expect in case that you get infected. What’s more, most Trojans are so stealthy and operate so secretly, that you may not even know that your machine has been infected since there will be no visible symptoms that can serve as a red flag.
On this page, our focus will be on one sophisticated threat of this kind that is called W4SP Stealer. A number of web users have recently faced this particular Trojan and some of them have contacted our “How to remove” team with a call for help. That’s why, in the paragraphs below we decided to shed some more light on the specifics of W4SP Stealer and the steps that its victims need to take in order to detect and remove it.
The W4SP Stealer Malware
The W4SP Stealer Malware can spread online with the help of various transmitters but most commonly they can be found inside spam messages, different email attachments, especially those sent from unknown senders, torrents, cracked software installers, malicious web ads and illegal sites.
SUMMARY:
| Name | W4SP Stealer |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
Please follow all the steps below in order to remove W4SP Stealer!
How to remove W4SP Stealer
- First, click the Start Menu on your Windows PC.
- Type Programs and Settings in the Start Menu, click the first item, and find W4SP Stealer in the programs list that would show up.
- Select W4SP Stealer from the list and click on Uninstall.
- Follow the steps in the removal wizard.
Read more…
What we suggest you do first is, check the list of programs that are presently installed on the infected device and uninstall any rogue software that you find there:
- From the Start Menu, navigate to Control Panel ->>> Programs and Features ->>> Uninstall a Program.
- Next, carefully search for unfamiliar programs or programs that have been installed recently and could be related to W4SP Stealer.
- If you find any of the programs suspicious then uninstall them if they turn out to be linked to W4SP Stealer.
- If a notification appears on your screen when you try to uninstall a specific questionable program prompting you to just alter it or repair it, make sure you choose NO and complete the steps from the removal wizard.
Remove W4SP Stealer from Chrome
- Click on the three dots in the right upper corner
- Go to more tools
- Now select extensions
- Remove the W4SP Stealer extension
Read more…
- Once you open Chrome, click on the three-dots icon to open the browser’s menu, go to More Tools/ More Options, and then to Extensions.
- Again, find the items on that page that could be linked to W4SP Stealer and/or that might be causing problems in the browser and delete them.
- Afterwards, go to this folder: Computer > C: > Users > *Your User Account* > App Data > Local > Google > Chrome > User Data. In there, you will find a folder named Default – you should change its name to Backup Default and restart the PC.
- Note that the App Data folder is normally hidden so you’d have to first make the hidden files and folders on your PC visible before you can access it.
How to get rid of W4SP Stealer on FF/Edge/etc.
- Open the browser and select the menu icon.
- From the menu, click on the Add-ons button.
- Look for the W4SP Stealer extension
- Get rid of W4SP Stealer by removing it from extensions
Read more…
If using Firefox:
- Open Firefox
- Select the three parallel lines menu and go to Add-ons.
- Find the unwanted add-on and delete it from the browser – if there is more than one unwanted extension, remove all of them.
- Go to the browser menu again, select Options, and then click on Home from the sidebar to the left.
- Check the current addresses for the browser’s homepage and new-tab page and change them if they are currently set to address(es) you don’t know or trust.
If using MS Edge/IE:
- Start Edge
- Select the browser menu and go to Extensions.
- Find and uninstall any Edge extensions that look undesirable and unwanted.
- Select Settings from the browser menu and click on Appearance.
- Check the new-tab page address of the browser and if it has been modified by “W4SP Stealer” or another unwanted app, change it to an address that you’d want to be the browser’s new-tab page.
How to Delete W4SP Stealer
- Open task manager
- Look for the W4SP Stealer process
- Select it and click on End task
- Open the file location to delete W4SP Stealer
Read more…
- Access the Task Manager by pressing together the Ctrl + Alt + Del keys and then selecting Task Manager.
- Open Processes and there try to find a process with the name of the unwanted software. If you find it, select it with the right button of the mouse and click on the Open File Location option.
- If you don’t see a “W4SP Stealer” process in the Task Manager, look for another suspicious process with an unusual name. It is likely that the unwanted process would be using lots of RAM and CPU so pay attention to the number of resources each process is using.
- Tip: If you think you have singled out the unwanted process but are not sure, it’s always a good idea to search for information about it on the Internet – this should give you a general idea if the process is a legitimate one from a regular program or from your OS or if it is indeed likely linked to the adware.
- If you find another suspicious process, open its File Location too.
- Once in the File Location folder for the suspicious process, start testing all of the files that are stored there by dragging them to our free online scanner available below.
- Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is free and will always remain free for our website's users.This file is not matched with any known malware in the database. You can either do a full real-time scan of the file or skip it to upload a new file. Doing a full scan with 64 antivirus programs can take up to 3-4 minutes per file.Drag and Drop File Here To Scan
 Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.
Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared. - If the scanner finds malware in any of the files, return to the Processes tab in the Task Manager, select the suspected process, and then select the End Process option to quit it.
- Go back to the folder where the files of that process are located and delete all of the files that you are allowed to delete. If all files get deleted normally, exit the folder and delete that folder too. If one or more of the files showed an error message when you tried to delete them, leave them for now and return to try to delete them again once you’ve completed the rest of the guide.
How to Uninstall W4SP Stealer
- Click on the home button
- Search for Startup Apps
- Look for W4SP Stealer in there
- Uninstall W4SP Stealer from Startup Apps by turning it off
Read more…
- Now you need to carefully search for and uninstall any Hostingcloud. racing-related entries from the Registry. The easiest way to do this is to open the Registry Editor app (type Regedit in the windows search field and press Enter) and then open a Find dialog (CTRL+F key combination) where you have to type the name of the threat.
- Perform a search by clicking on the Find Next button and delete any detected results. Do this as many times as needed until no more results are found.
- After that, to ensure that there are no remaining entries lined to W4SP Stealer in the Registry, go manually to the following directories and delete them:
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run/Random
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main/Random
The hackers who create the W4SP Stealer malware threat rely on camouflage and social engineering tactics in order to trick the unsuspecting web users into clicking on the harmful payload. They often mask their malware as some seemingly harmless type of web content or an intriguing message in order to attract the potential victim’s attention. Normally, one click is enough to infect the computer and activate the Trojan.
Once it has been activated, a threat like W4SP Stealer can start executing the malicious deeds it has been programmed for. At the beginning of this post, we mentioned some common uses but what you should keep in mind is that that after completing an attack on a single machine, certain Trojans may be repurposed remotely to do something different from the original mission. That’s why it is of critical importance to detect and remove the malware before it has unleashed all of its malicious potential. The quickest way to deal with the Trojan is to run a full system check with reliable antimalware tool and follow its instructions. Alternatively, you can try to detect and remove the malicious files manually with the help of a detailed removal guide like the one that you will find below. Just make sure you don’t experiment with your Trojan-removal skills if you haven’t dealt with such malware before as you may do more harm than good if you delete the wrong files.

Leave a Comment