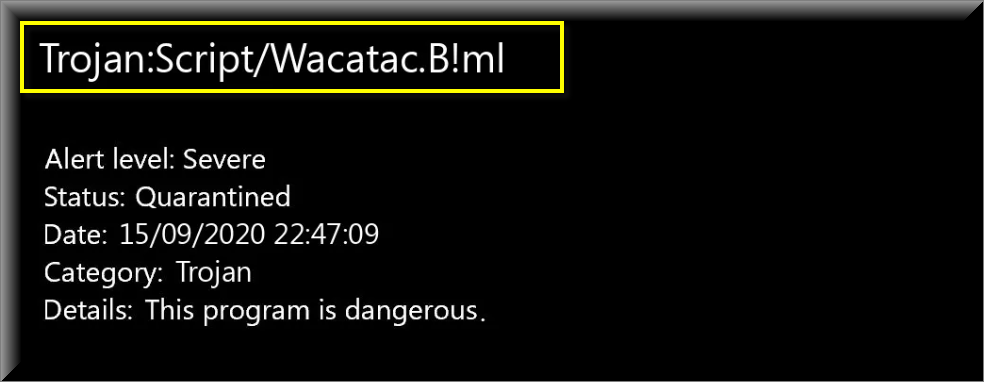
Wacatac B ml
If the insidious Wacatac B ml Trojan horse virus has managed to get inside your computer and is currently operating inside it, then you should really make sure to read all the info presented here. Wacatac B ml is a really serious malware threat and the sooner you begin your attempts at removing it, the higher the chances for a successful removal with minimal negative consequences.
Of course, we can’t guarantee that even if you remove the infection within the next 30 minutes that there will be no damage but it’s still preferable to act quickly instead of leaving it for later.
As we said, Wacatac B ml is a Trojan and this means a couple of things. First and foremost, it means that it might be difficult to locate the malicious data related to the malware within your system which is why we have provided our readers with a guide on how to locate and remove Wacatac B ml and we’ve also added a suggested removal tool to our guide for further assistance in case any of you might need it.
The second important thing to note about Trojans Wacatac B ml and Energy.exe is that they can oftentimes be used in a variety of ways in order to complete different criminal tasks. From system corruption and deletion of important data to personal espionage and gathering of intelligence which could then be used to blackmail the victim and harass them in other ways.
The Trojan Script Wacatac B ml
Taking over the targeted computer is also something that many representatives of the Trojan category like the “Trojan Script Wacatac B ml” might be able to do. Other potential uses of a Trojan like the “Trojan Script Wacatac B ml” like distributing Ransomware might also be possible, making this virus category one of the most versatile types of malware.
As said above, the timely removal of the threat is essential which is why we advise you to have a look at the following guide manual.
Taking your PC’s protection into your own hands
Having a reliable antivirus is a good thing but the reality of things is that the best protection you could offer your PC is your own vigilance and cautious behavior while you browse the Internet. Make sure not to visit any websites that could be unsafe or illegal as those are oftentimes hubs for malware distribution. Not only that, but you should also avoid downloading any suspicious software from questionable developers.
Opening spam e-mail attachments and attachments to shady web messages in general is also a big no-go. All in all, you must really pay attention to what you are doing online since the main reason for the majority of Trojan horse infections is none other than the users’ negligence and lack of care. Of course, this is not to say that having a good antivirus isn’t something that is of great importance as well but in the end, most hackers rely on the mistakes of the users as the one thing that would get their malware programs inside more and more machines so bear that in mind and stay safe out there!
SUMMARY:
| Name | Wacatac B ml |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | You might notice freezes, system crashes, increased CPU and RAM use and other similar forms of unusual PC behavior if you have a Trojan. |
| Distribution Method | A Trojan can be distributed with the help of spam messages, malicious online commercials, pirated software downloads, other backdoor malware, etc. |
| Detection Tool |
Remove Wacatac B ml Trojan
If you are looking for a way to remove Wacatac B ml you can try this:
- Click on the Start button in the bottom left corner of your Windows OS.
- Go to Control Panel -> Programs and Features -> Uninstall a Program.
- Search for Wacatac B ml and any other unfamiliar programs.
- Uninstall Wacatac B ml as well as other suspicious programs.
Note that this might not get rid of Wacatac B ml completely. For more detailed removal instructions follow the guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment