Wannapeace
A highly advanced form of malware has recently been spreading on the web and infecting unsuspecting online users. The name of the ranger is Wannapeace – a Ransomware cryptovirus, capable of encrypting the victims’ files with complex cryptography and blackmailing them to pay ransom.
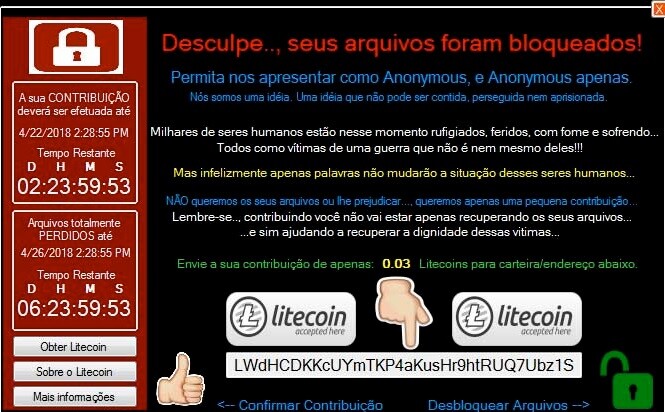
The Wannapeace Ransomware Lockscreen
The criminals, who stand behind the infection usually hold a special decryption key, which they offer after the encryption has taken place. If Wannapeace has already made it inside your system and you are now being ruthlessly blackmailed for the access of your own data, on this page, you will learn some useful facts about this type of malware and the possible methods to fight against it. For those users, who don’t want to pay ransom to the hackers, we have assembled a free removal guide, where you can find instructions for both – deleting the Ransomware and restoring some of your encrypted data. Due to the sophisticated level of this cryptovirus, however, no security expert can provide you with a 100% of recovery method. That’s why we cannot promise you a miraculous recovery from the attack of Wannapeace Rasnomware. Still, we believe that trying out every alternative is preferable than giving your money to some anonymous cyber criminals, which may never send you a decryption key. For this reason, we encourage you to read the next lines and give a try to the removal guide below.
The Wannapeace Ransomware
In the case of an attack with a ransomware like Wannapeace, the targeted files are not damaged, they simply get locked by an encryption code, but they remain on the system. This way of causing harm is a bit challenging for the conventional antivirus programs to recognize, that’s why, more often than not, the Wannapeace Ransomware infection can remain under the radar until a ransom message appears on the victims’ screen.
Ransomware viruses are some of the trickiest and sneakiest forms of malware. They can invade your computer without any visible symptoms, and detecting them before they have applied their encryption is almost impossible. The reason is, most antivirus tools are often unable to recognize the encryption process that the virus runs as malicious. Therefore, they leave it to finish without interrupting it or notifying you. In fact, the traditional virus definitions are programmed to spot processes, which corrupt, delete or damage the computer system and its data.
Why is it advisable to avoid the ransom payment and seek alternatives?
When dealing with cyber criminals, you can never be sure of their actions. Even if you strictly fulfill all the requirements they have in the ransom note, there is no guarantee that they will send you a decryption key. There is also no guarantee that this decryption key will work. The only sure thing is that you will be giving your money to some anonymous hackers, who will continue to trouble you and other online users with their blackmail scheme. Unfortunately, since the ransom payments are usually requested in cryptocurrency (such as Bitcoins) you cannot expect that the criminals will be traced and your money will be retrieved. Such payments are virtually untraceable and help the hackers to remain undetected by the authorities, so they may never get caught and you may never get compensated. With all this in mind, our “How to remove” team, as well as other leading security experts, will always encourage the victims of Ransomware to seek for alternatives and to avoid the ransom payment. One of the options is the guide below, which can help you remove Wannapeace from your system. Additionally, you may be able to get some of your files back without paying ransom by trying out the file-restoration instructions we have included in it.
Ways to protect your PC from Ransomware:
Compared to other malicious threats, the chances of successfully dealing with a Ransomware attack and its consequences are much lower. That’s why it is better to avoid contamination than trying to recover from a sophisticated file encryption. If you want to protect your machine from future Ransomware infections such as Wannapeace, it is very important to remember and apply the security tips that we will give you here. As a beginning, you should always use your common sense when browsing the web and avoid any suspicious link, ad, message or sketchy content. Landing on shady sites and installing unreliable software is also a potential way of catching Ransomware. For your safety, do not neglect the importance of having reputed antivirus software, which is able to detect malicious encryption processes or potential malware transmitters such as Trojans and other well-camouflaged infections. And last, but not least, backing up your files regularly and keeping them safe on an external device can help you restore them anytime, even if Ransomware attacks you. That’s why it is a good idea to create copies of your most important data and store it safely to prevent falling victim of a nasty data blackmail scheme.
SUMMARY:
| Name | Wannapeace |
| Type | Ransomware |
| Detection Tool |
Remove Wannapeace Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment