WannaRen
WannaRen is a new malware virus that falls under the widespread Ransomware file-locking category. Like other Ransomware viruses, WannaRen uses advanced encryption to make most or all of the user’s files unavailable so that the hackers can later demand a ransom for the decryption key.
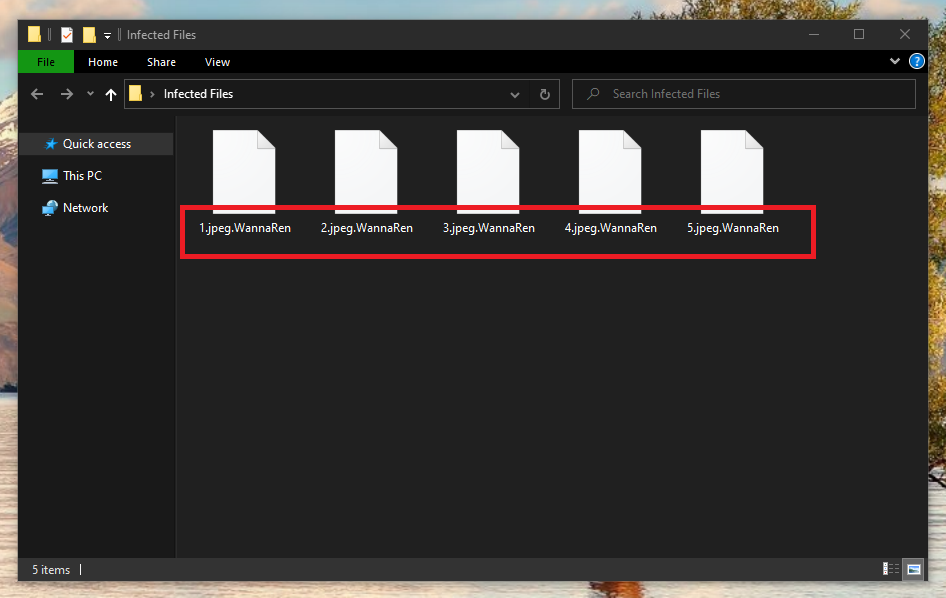
The WannaRen Virus file encryption
This money extortion scheme is very common nowadays and it is responsible for thousands (if not millions) of users losing access to their files each week. The purpose of viruses like WannaRen is simple – they seek to make the most important files of their victims inaccessible so that, later, the hackers can blackmail the users for a ransom payment. If the payment is made, a special unique key would be sent to the victim that would allow him or her to remove the data-encryption from their files. This is, at least, what the hackers would tell you in a message displayed by the virus immediately after the encryption is completed. If none of the files locked by WannaRen are of any particular importance to you, you have the option of ignoring the encryption and simply removing the virus (we will show you how to do that). Since Ransomware viruses usually don’t cause any other harm in the system, there wouldn’t be anything else that the hackers could use as leverage for blackmailing you. If, however, the virus has managed to find and encrypt data which is valuable to you (and if you don’t have said data backed up), then you’d be faced with a particularly unpleasant problem that you must approach carefully and rationally or else the situation may get even worse.
The WannaRen virus
The WannaRen virus is a file-encrypting Windows infection that locks its victims’ files using a sophisticated encryption algorithm. The WannaRen virus demands payment in exchange for the unique decryption key that can set free the locked files.
If you have had some important files of yours encrypted by this insidious malware program, then you are advised to take some time to learn about the potential alternative solutions to this issue instead of directly transferring the demanded sum. Since there’s no way of knowing whether the hackers would allow you to restore your data after you make the payment, it is best if you leave this option as your last resort variant. We have posted some recovery suggestions after the removal instructions in our guide and though we can’t promise you that any of the alternatives will work in your case, it is still a good idea to try them and see for yourself.
The WannaRen file encryption
The WannaRen file encryption is a process that uses a sophisticated algorithm to make your files inaccessible through regular means. The WannaRen file encryption has a corresponding decryption key that is unique for every computer that this virus has attacked.
This means that the files on your computer cannot be unlocked by the decryption key generated for the encrypted files of another WannaRen victim. However, some of the suggestions from our removal guide may allow you to bring back the encrypted data without the need to actually acquire the matching key for your files. Again, we cannot promise anything, but the only way to know if the alternative methods would work is if you try them out.
SUMMARY:
| Name | WannaRen |
| Type | Ransomware |
| Detection Tool |
Remove WannaRen Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment