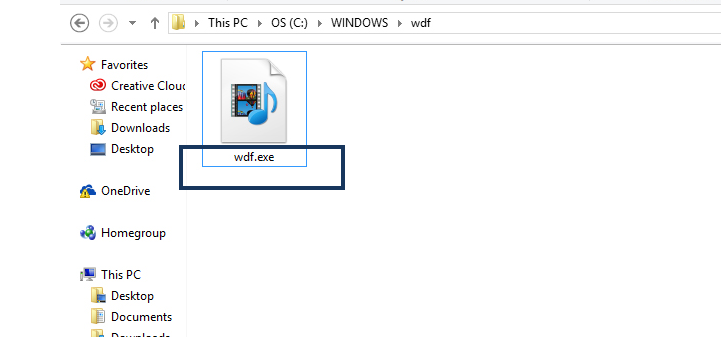
WDF.exe
If you would like to learn how to protect your PC from a Trojan horse named WDF.exe, or you are looking for an effective way to remove it, this is the page to be on! In the text that follows, we are going to describe the most common transmitters of this infection, its possible harmful effects and the steps to detect and remove it from your system. The good news is that you don’t need to be an expert to deal with WDF.exe, because with the help of the detailed Removal Guide below you will be able to safely identify the Trojan and delete it.
You can also use the professional removal tool and scan your PC with it to ensure that no remains are left hidden in the system. We invite you to stay with us until the end because we have some very useful information to share with you.
WDF.exe – a recent CPU mining Trojan threat, which could harm you!
WDF.exe is a recently reported Trojan horse infection, which has managed to sneak inside quite a number of computers. Some attacked users have contacted our “How to remove” team with a request to help them deal with this malware, which is capable of various harmful deeds. If we have to talk about Trojans in general, each and every representative is different and can be programmed for a specific criminal task. That’s why it is almost impossible to tell you what exactly WDF.exe is specialized in. Usually, the hackers program such malware individually, according to the specific task they want to use it for. This ability of the Trojans has made them a favorite tool of online fraud and theft in criminal circles. A virus -like WDF.exe, for instance, could easily be held responsible for some of the following malicious deeds:
- Destruction of files and software – A common harmful effect of being infected with a Trojan horse is the possible corruption and destruction it may cause. Targets could be all of your files, certain system processes, Registry keys or any software that can be found on the machine. The hackers could basically mess around with everything as they please, this way creating malfunction or total destruction of the computer.
- Espionage and data theft – Trojans are a perfect tool of spying and data theft. It is possible that WDF.exe could be programmed to secretly keep track of your activity from the moment you turn the computer on and copy your passwords, login credentials, keystrokes, credit or debit card details and other sensitive information that you keep on your PC. When the hackers get their hands on such sensitive details, they can easily use them to blackmail you, steal your identity or money and many other criminal activities.
- Distributing Ransomware and other viruses – Trojans like WDF.exe could easily exploit any system vulnerability and silently get inside the computer without any visible symptoms. Apart from this, the malware may also carry some other viruses along and introduce them to the system in a very stealthy way. The creators of Ransomware and other nasty infections commonly use this ability of the Trojans in order to infect hundreds of computers.
What we just mentioned above is just a small portion of the criminal activities that a Trojan can be involved in, that’s why our advice is to remove this malware immediately and thoroughly scan your PC with the help of reputed security software.
How to protect your PC from Trojans?
According to security experts, Trojans can be blamed for every two out of three online infections that happen through the internet. This statistic gives just a brief idea of how popular and widespread these threats are. Unfortunately, you never know when and how you may come across an infection like WDF.exe, because Trojans are so tricky and use so many malicious transmitters that it is literally impossible to avoid them all. However, there are a few useful tips that may help you to protect your system. For instance, you should know that the cyber criminals put a lot of efforts in camouflaging their malware into some harmless-looking online content. That’s why, you should be very cautious when coming across various websites and pages, especially sketchy sites full of nagging ads, pop-ups and blinking banners. Avoid clicking on anything you don’t trust and never open spam messages, email attachments, free installers, or “too-good-to-be-true” offers, as some of them may be compromised and end you up with an infection. Last, but not least, it is of utmost importance to have a reliable antivirus program and run regular scans with it to keep your system protected as much as possible.
SUMMARY:
WDF.exe CPU Miner Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Reply