*Source of claim SH can remove it.
Once you get infected by the Chromium virus, you will probably not notice any significant change until you start your Chrome browser. This is because the Chromium virus actually “becomes” your Google Chrome browser by replacing its shortcut with a fake one that seems like Google Chrome but is actually a shortcut for the Chromium virus. Once you start it, it would look and mostly behave like Google Chrome but there will be certain differences. For instance, random ads, pop-ups, and automatic redirects are likely to disturb your browsing. Also, the starting page, the new-tab page, and the default search engine of the browser would probably be different from the ones that used to be in your browser. In some cases, the search engine might seem like Google but actually, be a modified version of the Google search engine that is programmed to show you aggressive and unsafe ads in the search results or outright redirect you to unfamiliar pages whenever you perform an online search.
In addition, the Chromium virus is likely to gather different types of data from your computer and distribute it to third parties without your permission. Admittedly, most popular browsers, including the regular Google Chrome, do this as well. However, they try to be transparent regarding the types of data they collect, the third-parties they send it to, and the ways that data would be used. Also, the third-party partners of legitimate browsers that collect user data are also trusted advertisers that abide by the law. On the other hand, you won’t get any information about who your data is sold to by the Chromium virus or how it would be used. Unfortunately, there’s a very high chance that scammers, hackers, online crooks, and other cybercriminals may get their hands on your information after it has been transmitted to them by the Chromium virus.
Is Chromium a virus?
Chromium is not a virus – it is an open-source browser project which is basically the Alpha version of the Google Chrome browser. The idea of open-source software such as Chromium is that anyone could access its code and modify it to create new programs.
Many of the current most popular browsers (not counting Google Chrome) are based on Chromium. Those browsers include Opera, Vivaldi, Brave, and even Microsoft Edge. However, the fact that the Chromium code is freely available to anyone means that hackers and cybercriminals could also access it, modify it, and use it for their nefarious goals. This is how the Chromium viruses are created and it is also the reason why it is often rather difficult to find out what is wrong with a computer infected by a Chromium virus because most people wouldn’t suspect that anything based on Chromium would threaten their systems.
In addition, as we mentioned earlier, once the Chromium virus infiltrates your PC, it doesn’t make any significant changes that are immediately noticeable. It stealthily replaces the Google Chrome shortcuts with fake ones that open the virus so that people would be unknowingly using the modified Chromium browser (the Chromium virus) while surfing the Internet without realizing it. Of course, once you start the Chromium virus you will quickly notice that something’s not quite right – the changed browser settings and aggressive online promotions that weren’t there before will give away the presence of the virus but even then many people wouldn’t suspect that the whole browser that they are using at the moment is, in fact, a virus.
It is worth noting that the Chromium virus doesn’t always install as a standalone program. Sometimes, it may get integrated as an add-on with the Google Chrome browser that’s already in the system and simply change some of its settings to fit the goals of the hackers who have created it.
There are many different ways to catch a Chromium virus, including fake software update requests, low-quality free software bundles with the virus included in them, misleading web-ads and spam email links or attachments that automatically download the virus when you click on them, etc.
What is Chromium?
Chromium is an open-source software project that contains the original code for the Google Chrome browser. Chromium can be freely accessed and modified to create new browsers and browser components and it is the basis for popular browsers such as Microsoft Edge and Opera.
There isn’t a single “Chromium” browser or a stable version of it. Instead, many parties (but not Google) have created their own versions of a Chromium browser and made it publicly available for free. Most of those browsers are similar and function as simplified versions of the Google Chrome browser having fewer features and a more minimalist interface.
Due to the open-source nature of the Chromium project, some cybercriminals use it to develop malware and disguise it as the Google Chrome browser in order to trick users into downloading it and running it on their computers.
If you have a suspicion that you are dealing with a Chromium virus at the moment, it’s best if you directly begin completing the following guide once you are finished reading this article.
Summary
| Name | Chromium ( a Virus injected in the Chromium) |
| Type | Browser Hijacker/ PUP (takes the place of your browsers) |
| Danger Level | Medium or High |
| Symptoms | Pop-up ads, random opening of web pages, Chromium taking the place of your browsers |
| Distribution Method | Spam e-mails, infected files, non-verified downloads |
| Detection Tool |
*Source of claim SH can remove it.
How to Uninstall Chromium
To get rid of Chromium, you can try to uninstall the Chromium browser/virus from your Control Panel. If deleting Chromium from the Control Panel makes the virus symptoms stop when you browse the Internet, you won’t have to complete the rest of the guide.
- From the Start Menu, click on Control Panel and then select Uninstall a Program.
- From the displayed list of programs, find and click on the Chromium icon (not Google Chrome!).
- Click on the Uninstall button and follow the on-screen uninstallation instructions.
- If you are asked if you want to keep your personalized settings, select No.
- Look for other suspicious programs in the list and uninstall them too.
Once you complete the uninstallation, restart the PC, go to your main browser and see if the virus symptoms are gone. If the Chromium virus continues to disrupt you, complete the rest of this guide carefully to remove everything related to the virus that may be left in your system.
Chromium Virus Uninstall Guide for Windows
This is a more detailed and expansive uninstall guide for Chromium. Follow the steps in the order they are shown and if you come across any difficulties or don’t understand something, be sure to leave us a comment outlying the problem and we will be sure to get back at you at the earliest opportunity.
Step 1.
The first step for most troubleshooting guides is always to enter Safe Mode on your computer. This is important because it only allows processes essential tot he system to start with Windows, leaving out any non-essential processes (some of which are likely linked to the problem). If you don’t know how to boot into Safe Mode, follow the provided link that will bring to a page where you can find out how.
Step 2. Find Unwanted Processes
*Source of claim SH can remove it.
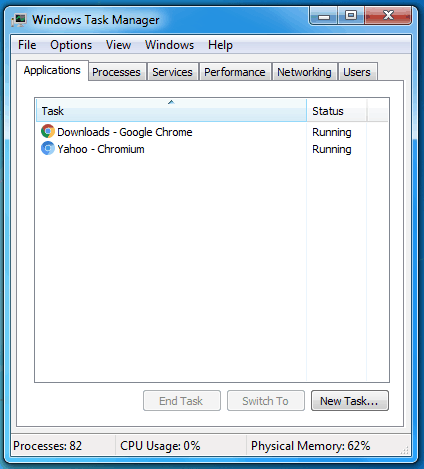
- Go to the Task Manager of your computer – you can open it by pressing together Ctrl + Shift + Esc on your keyboard.
- Select Processes and try to find the process run by the Chromium virus (it might go under a different name).
- If you don’t see a process named “Chromium”, seek other processes that have unfamiliar names and that are using up significant amounts of computer resources – RAM memory and processing power (CPU).
- If you see a resource-intensive process that doesn’t seem to correspond to any of the programs running on your PC at the moment, there’s a high chance that said process is from the virus.
- Look up the name of the suspected process to make sure that it isn’t a regular system process that you aren’t supposed to quit.
- If the suspected process is not from your system, right-click on it and select the Open File Location option.

- Scan the files in the File Location folder with the following free online scanner:Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is free and will always remain free for our website's users.This file is not matched with any known malware in the database. You can either do a full real-time scan of the file or skip it to upload a new file. Doing a full scan with 64 antivirus programs can take up to 3-4 minutes per file.Drag and Drop File Here To Scan
 Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.
Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.- If you want, you can also use a security tool of your own for the scans.
- If even a single file gets flagged as malware, right0click on the suspected process again and select End Process Tree.
- Then go back to the file location folder and delete it with all the files that are in it.
- If you see an error message when deleting the folder because a file(s) in it cannot be deleted, open the folder and delete the other files.
- After everything else from this guide is completed, try to delete the file location folder again.
Step 3. Remove Chromium Virus From Start-Up Locations
- Type System Configuration under the Start Menu and click on the first item.
- Open Startup and remove the ticks from all startup items that are unfamiliar and may be linked to Chromium.

- If there are items with unknown manufacturers, uncheck them too unless you recognize them and know they are trusted.
- Click on OK once you are finished and proceed to Step 4.
Step 4. Hosts file
*Source of claim SH can remove it.
- Copy this “notepad %windir%/system32/Drivers/etc/hosts“, place it in the search field under the Start Menu and open the file that shows in the results.
- In the notepad file that opens, the last line of text should be LocalHost – if there’s anything written below it, copy it and place it in the comments.

- After we look at the text you’ve sent us, we will tell you if the lines below LocalHost are from the virus. If they are, you must delete them from the Hosts file.
- After you delete what’s below Localhost, save the file by clicking on File > Save.
Step 5. Check DNS settings
- Press the Winkey to open your Start Menu and type Network Connections.
- Press Enter to open the first result.
- When the folder with your different network connections shows up, right-click on the one that’s currently in use and select Properties.
- Click on Internet Protocol Version 4 (ICP/IP) from the list of items and then click on Properties.
- Check the Obtain DNS server addresses automatically if the option isn’t currently enabled.
- Go to Advanced > the DNS tab and delete all servers listed there by selecting them and clicking on Remove.
- Click OK on everything to save the changes and exit the DNS settings.

Step 6. Remove Chromium Virus From All Browsers
If any of your browsers have been affected by the Chromium Virus and have had changes made to them without your permission, you must complete this last step to ensure that there is nothing left on the computer related to the unwanted software.
First, go to the affected browser(s) icon, right-click on it, and go to Properties.

From the Properties window, select the Shortcut tab and delete everything that is written in the Target field after “.exe“. Click on Ok to save the changes and then open the browser itself.

This next part of the current step slightly varies for each specific browser so we will show you how to complete it for some of the most commonly-used browsing programs.

Delete Chromium Virus from Internet Explorer and Edge
- Once you are in Internet Explorer, select the Gear icon and then select Manage Add-ons.

- Delete any add-on from the browser that seems connected to the Chromium virus.
- Select Internet Options from the main browser menu.
- If the homepage URL has been replaced by the Chromium virus, delete that homepage address and type another one from a trusted and reliable site (such as Google.com).
- Click on Apply so that the changes could take place and exit the browser.
Delete Chromium Virus from Firefox
- In Firefox, select the three vertical lines in the top-right corner and go to Add-ons.
- In the Add-ons page, look for items that you think may be linked to the virus and uninstall them. Do not be afraid to remove all add-ons if you are uncertain which one is not supposed to be there – you can always reinstall the safe ones at a later time.

- Go to Options from the browser menu, type Clear in the Options search box, and select Clear Data.
- Make sure that the two checkboxes are ticked and click on Clear.
Delete Chromium Virus from Chrome
- Start Chrome, click on the icon with the three dots (upper-right corner) and go to More Tools > Extensions.
- Do the same think like with the two previous browsers removing any extensions that may be linked to the Chromium virus.
- If an extension refuses to get uninstalled, click on the toggle button below it to disable that extension and then select Remove immediately after.

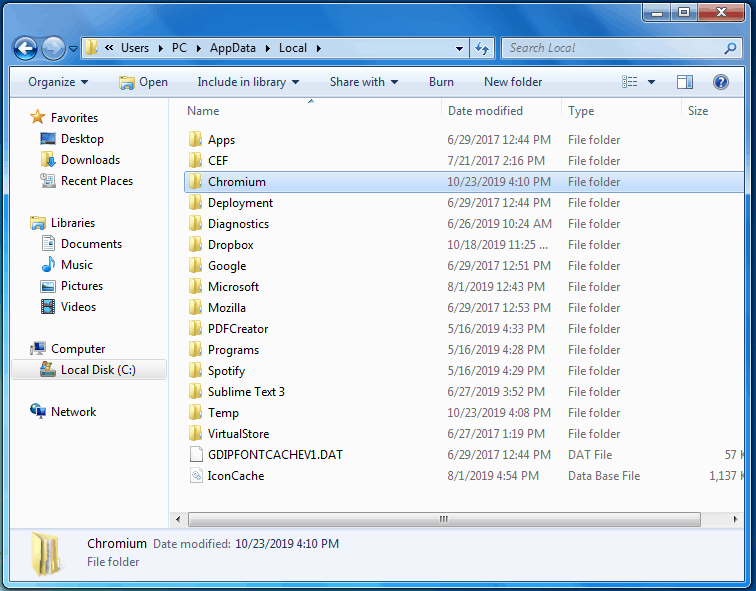
- Go to the following folder on your computer: Computer\C:\Users\*User Account Folder\App Data\Local\Google\Chrome\User Data.
- If you cannot find the App Data folder, it is likely hidden and you need to make the hidden files and folders on your computer become visible. Follow this link to find out how you can do that.
- If you cannot find the App Data folder, it is likely hidden and you need to make the hidden files and folders on your computer become visible. Follow this link to find out how you can do that.
- Rename the folder titled Default to Backup Default and then restart your PC.
How to Delete Chromium?
This final step from the guide will require you to go to the Registry of your computer and make changes to it by deleting items that are connected to the Chromium virus. Since many sensitive and important system and software settings are in the Registry, you should be really careful not to delete the wrong thing. That is why, in case of doubt, you should always first request our assistance through the comments section, telling us about the Registry item(s) you are unsure about. Only once (if) we confirm that the item(s) in question are to be deleted should you proceed to remove them from the Registry.
- Press the Windows key and the R key from the keyboard to open Run.
- Type regedit and hit the Enter key to start the Registry Editor.
- Click on Yes when Windows asks for your Admin permission.
- Go to the Edit menu in the Registry Editor and select Find.
- Type Chromium in the search box and click on Find Next (the search may take a while, be patient).
- Select the item that gets found, press Del, and confirm the command by clicking on Yes.
- Repeat mini-step 5 and 6 until there aren’t any more entries named Chromium in the Registry.
- Go to the following directories in the left panel of the Registry Editor:
- HKEY_CURRENT_USER/Software/
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run/
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main/
- If you find any suspicious-looking folders in them that have unusually long names and/or names that seem to consist of randomized letters and numbers, delete those folders too.
- It is very important to not delete anything unless you are certain it is from the virus. If you are unsure about whether you should delete a given item, ask us about it in the comments before you proceed with the deletion!
Final Notes
In case the completion of the manual steps from this guide didn’t resolve your problem with the Chromium virus, we suggest you try out the powerful anti-malware tool that you can find posted above. It will quickly detect the remaining malware data and delete it for you. In addition, this security app can keep your system protected against many other types of viruses and malware, adding an extra layer of protection to your PC.

Hi Sun,
these are fine. Contact us if you need any help.
After I followed all the steps and deleted chromium my chrome browser was insanely slow every time I opened it my CPU would spike idk what is happening.
is this site a true site?
Hi Luis,
can you be more specific ? i didn’t quite understand you.
We wouldn’t suggest our readers software that is not safe to use. Which Remover tool are you exactly referring to?
Hey i installed CCleaner and for some reason after my CCleaner got installed chromium icon just appeared on my desktop and in my task bar so i did go in control panel and uninstalled after that i saw no things hijacking my browser or pop-ups after like 2 months or more i saw my DISK USAGE was 100% and i called my brothers he knows about computers and he told me that may be some malware i simpy played Steam games and i didnt download any unsafe files from internet not even music ! After that i factory reset my pc after that My pc was going slow ..And i heard malware could have Restore Point i got so scared that it may come back after 1 month i saw my cooling fan was just from it self going high i thought that was dust but it was completly clean i scanned my system with AVAST Antivirus nothing was there and i was just checking my system files and i saw 1 or 2 files having alot of numbers i thought that was some system files but when i went in Chromium was there and just copying some files from my D: Drive and from my Web Browser history i got so scared ..When i entered in that file AVAST automaticlly said infection detected i tried going in safe mode it will not allow me i couldnt do anything but there were no popups or hijacking my browser PC was just slow after that i got MAD and i simply took my system down and deleted everything i even removed win8.1 after that i installed new Win8.1 is there any possibilty that he can come back because i have same HDD ? I know this is a long story but i want you everything to know 😀 ! Please answer,thanks !
If you have re-installed everything, there’s probably no need to worry. How is your PC behaving now? Are there any problems after you re-installed Windows?
Probably not. Still, scanning the folder might not be a bad idea. Tell us in the comments if anything got detected.
Remove the IP address that you’ve send us as well as any other similar address and then save the file.
Could you please rephrase your question?
Since those IP’s are more than likely coming from the unwanted software, we advise you to delete them and then save the changes to the Hosts file.
Getting the free version of SpyHunter would provide with the scanner function of the program which would detect any suspicious and potentially unwanted or harmful files on your PC but you will need to manually remove them. If you opt for the paid version of the program, it will also provide you with a removal tool that will almost always succeed in removing the problematic software. In addition to that, even if the program fails to resolve your issue, you have the option to ask for live support from the program’s developers so that you can receive a custom fix method for your specific situation.
Those addresses aren’t necessarily harmful yet they should still be removed from your Hosts file since they aren’t supposed to be there. Be sure to delete them and save the changes to the Hosts file.
I tried the conventional ways one but couldn’t advance it more because I don’t want to risk myself by meddling with system files & registries, so I tried to download your recommended software and installed it… the bad news is, installation error (your software can’t be installed in my PC).
What error dos it give you? Also, do you have Administrator rights on the PC that you’re using?
Hi, i have been following these steps and stuck in step 4, I can see below the local host, they are some ip adress that are supiscious
127.0.0.1 down.baidu2016. com
127.0.0.1 123.sogou. com
127.0.0.1 http://www.czzsyzgm. com
127.0.0.1 http://www.czzsyzxl. com
0.0.0.1 msplus.mcafee. com
I have tried opening the DNS, however there are no rogue dns to remove whatsoever. How?
Remove those IP’s from yout Hosts file because they mustn’t be in it.
Where do you want to get back to?
what does these mean?
# unchecky_begin
# These rules were added by the Unchecky program in order to block advertising software modules
0.0.0.0 0.0.0.0 # fix for traceroute and netstat display anomaly
0.0.0.0 tracking.opencandy. com.s3. amazonaws. com
0.0.0.0 media.opencandy. com
0.0.0.0 cdn.opencandy. com
0.0.0.0 tracking.opencandy. com
0.0.0.0 api.opencandy. com
0.0.0.0 api.recommendedsw. com
0.0.0.0 rp.yefeneri2. com
0.0.0.0 os.yefeneri2. com
0.0.0.0 os2.yefeneri2. com
0.0.0.0 installer.betterinstaller. com
0.0.0.0 installer.filebulldog. com
0.0.0.0 d3oxtn1x3b8d7i.cloudfront. net
0.0.0.0 inno.bisrv. com
0.0.0.0 nsis.bisrv. com
0.0.0.0 cdn.file2desktop. com
0.0.0.0 cdn.goateastcach. us
0.0.0.0 cdn.guttastatdk. us
0.0.0.0 cdn.inskinmedia. com
0.0.0.0 cdn.insta.oibundles2. com
0.0.0.0 cdn.insta.playbryte. com
0.0.0.0 cdn.llogetfastcach. us
0.0.0.0 cdn.montiera. com
0.0.0.0 cdn.msdwnld. com
0.0.0.0 cdn.mypcbackup. com
0.0.0.0 cdn.ppdownload. com
0.0.0.0 cdn.riceateastcach. us
0.0.0.0 cdn.shyapotato. us
0.0.0.0 cdn.solimba. com
0.0.0.0 cdn.tuto4pc. com
0.0.0.0 cdn.appround. biz
0.0.0.0 cdn.bigspeedpro. com
0.0.0.0 cdn.bispd. com
0.0.0.0 cdn.bisrv. com
0.0.0.0 cdn.cdndp. com
0.0.0.0 cdn.download.sweetpacks. com
0.0.0.0 cdn.dpdownload. com
0.0.0.0 cdn.visualbee. net
# unchecky_end
Well, it means that you should probably delete the IPs from the Hosts file where you found them. Those aren’t supposed to be there so make sure you remove them from the file and save the changes.
# unchecky_begin
# These rules were added by the Unchecky program in order to block advertising software modules
0.0.0.0 0.0.0.0 # fix for traceroute and netstat display anomaly
0.0.0.0 tracking.opencandy .com.s3.amazonaws. com
0.0.0.0 media.opencandy. com
0.0.0.0 cdn.opencandy. com
0.0.0.0 tracking.opencandy. com
0.0.0.0 api.opencandy. com
0.0.0.0 api.recommendedsw. com
0.0.0.0 rp.yefeneri2. com
0.0.0.0 os.yefeneri2. com
0.0.0.0 os2.yefeneri2. com
0.0.0.0 installer.betterinstaller. com
0.0.0.0 installer.filebulldog. com
0.0.0.0 d3oxtn1x3b8d7i.cloudfront. net
0.0.0.0 inno.bisrv. com
0.0.0.0 nsis.bisrv. com
0.0.0.0 cdn.file2desktop. com
0.0.0.0 cdn.goateastcach. us
0.0.0.0 cdn.guttastatdk. us
0.0.0.0 cdn.inskinmedia. com
0.0.0.0 cdn.insta.oibundles2. com
0.0.0.0 cdn.insta.playbryte. com
0.0.0.0 cdn.llogetfastcach. us
0.0.0.0 cdn.montiera. com
0.0.0.0 cdn.msdwnld. com
0.0.0.0 cdn.mypcbackup. com
0.0.0.0 cdn.ppdownload. com
0.0.0.0 cdn.riceateastcach. us
0.0.0.0 cdn.shyapotato. us
0.0.0.0 cdn.solimba. com
0.0.0.0 cdn.tuto4pc. com
0.0.0.0 cdn.appround. biz
0.0.0.0 cdn.bigspeedpro. com
0.0.0.0 cdn.bispd. com
0.0.0.0 cdn.bisrv. com
0.0.0.0 cdn.cdndp. com
0.0.0.0 cdn.download.sweetpacks. com
0.0.0.0 cdn.dpdownload. com
0.0.0.0 cdn.visualbee. net
# unchecky_end
Remove all of these from your Hosts file by deleting them and then saving the changes to the file – those IP addresses aren’t supposed to be there and are almost certainly part of the problem.
How do I remove them?
What are you trying to remove? Please, be more detailed.
How do I remove those IP addresses from my Host file?
Just open the file and delete them as you’d delete text from any other text file and save the changes to the file afterwards.
I have this chromium virus. i think i got most of it off but i recall seeing something else that was associated with it when i was deleting and i forgot to write it down. It started with a “P” like pankan or something like that. Is this a virus too that need to be removed and what is the proper spelling so i can search for it. Thanks!
We do not know exactly what you are talking about. Where did you find this?
Thank you so much!
You are most welcome!
alright so, I had dealt with this before. I simply deleted it. But from another website, I got it, and couldn’t find it, so I simply removed it from the computer in the Control Panel. Both of these made my computer really laggy and it had things glitch out. I think it also started some random youtube links I had open at the time.
So, what is your situation right now? Are you still having issues?
if you have windows 10, I suggest opening the control panel, right here. https://uploads.disquscdn.com/images/e9ef46b604b458a50cb58b604404c3c9fbd11b5847e83567a6fdcdfb46533791.png
Thanks this is very detailed and helpful
ahhhh help im trying to uninstall it but it’s not coming up in my list of things to uninstall :(((((((
Complete the other steps – it is common for such software to not be present in the list of programs in the Control Panel.
I can’t install the anti virus software you recommended even though I downloaded it.
Hi Tawseef,
you can remove the program from your Programs List in Settings/Control Panel in Windows, though we recommend you to keep the antivirus software to keep your system safe
Hi Tawseef,
did you double click the install file, so you can start the installation? What is the issue you are encountering?
when I try to uninstall it it states, even after entering a pin “please contact a system admin” and it won’t uninstall chromium. Help?
Hi Tony,
did you follow the removal guide?
Hello. I downloaded spyhunter. Will I still need to do the following steps too?
Hi Shareena Baurhoo
You have to run Spyhunter and it will take care of the rest. You don’t have to go through the guide.