This page aims to help you uninstall Pokki Update “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
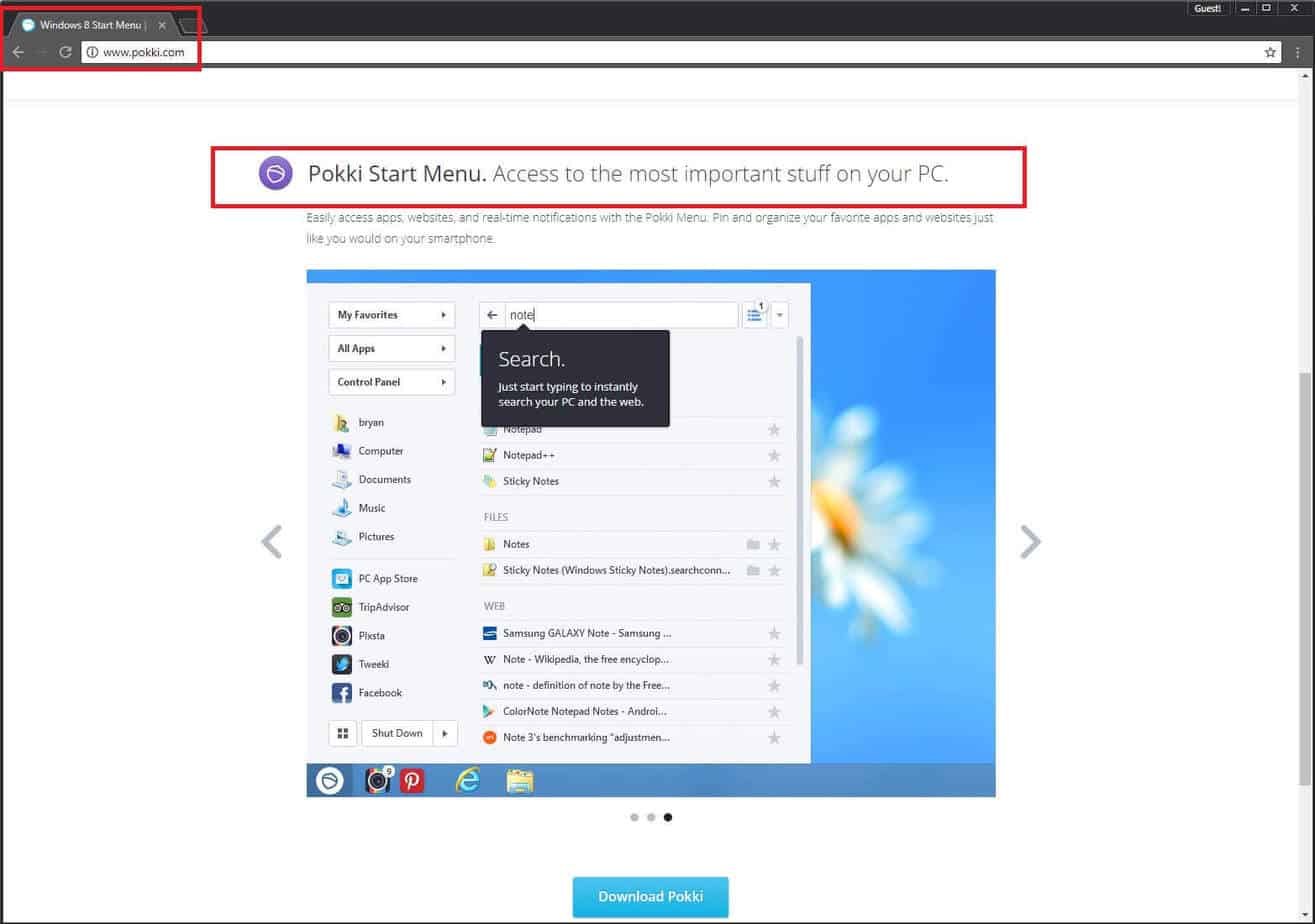
The article you are reviewing at the moment is focused on Pokki. This program is a form of ad-producing software the only usage of which is to display ads in different colors and shapes. Another typical aspect of all ad-broadcasting programs is that they normally target all your browser apps and affect them by making them behave in an annoying way – even the most popular ones such as Firefox or Chrome, might get infected. All the programs capable of doing that are called Adware and we will be talking about them in detail below.
General details regarding Adware:
All the programs characterized as Adware have been created to act as marketing tools. Indeed, this ad-producing product has exactly such a purpose: to broadcast as many pop-ups, tabs or banners, as it is actually possible. The parties interested in creating and using this kind of software are the producers of the goods that are advertised; the providers of the services offered; and the creators of Adware themselves. The product manufacturers and service providers actually pay the software developers to write the most effective promotion-oriented software (the one displaying the largest number of ads in the most effective way). After that, some of the promoted products may be bought by the people seeing the ads, thus their manufacturers might profit. This is a win-win situation – every party involved in the scheme is happy in the end, except for the irritated users who accidentally end up installing any form of ad-producing software.
In what ways may Adware get spread?
What might appear somewhat suspicious about all ad-producing programs is that they do not get spread in a clear way. In the majority of the cases, you could find such software as a part of a contagious website or a torrent, or as a component of a video-sharing platform, etc. Nonetheless, oftentimes Pokki and the other products of this kind could be lurking inside bundles and you might end up getting tricked into willingly installing them on your device. If you still have no idea about what software bundles are: they represent free software in many forms – games, apps, programs. There is nothing dangerous about such bundles in general. Still, Pokki may be hiding inside them and this might not be stated anywhere in the description of such a bundle, which is suspicious.
An important tip: We know that you perhaps want to try a version of certain software for free, and it may be spread in bundles. In this case, to keep being Adware-free, you need to learn how to install such bundles in a proper way. If you do that right, no ad-producing program will ever annoy you. Just follow this ultimate piece of advice: whatever you install on your PC, make sure you go with the Advanced or the Customized wizard feature. If you do that, each detail regarding the bundle will be stated and you will be able to select what you really want from all of its content, and what you don’t want to install. Then you will just have to opt out of the unnecessary products like Adware, for instance.
The info above perhaps has left you with the impression that Adware is as dangerous as malware…
Still, this is not the case at all. Adware, because of the way it may broadcast its ads, and the way it could get distributed, has been regarded as potentially unwanted for a long time, however, it has never been classified as malware. And you are going to see why – there are substantial differences between Adware and malware. For example, Ransomware and Trojans are seen as the most harmful malware subcategories. What such viruses could do is to hack your PC without your approval, just by themselves, for this purpose using a weakness of your system (or any program). After that their dangerous activities usually involve destroying data or corrupting it; encrypting files and asking for a ransom in exchange for their recovery; espionage; tracking your private online activities or directly on you using your webcam; infiltrating your banking and social media accounts and using them for stealing money, etc.
SUMMARY:
| Name | Pokki Update |
| Type | Adware |
| Detection Tool |
Pokki Update “Virus” Uninstall
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Hello.
I Am Having Some Trouble Getting Rid Of This No Good Adware Pokki Start Menu.
When I Downloaded The Pokki Start Menu I Thought It Was SafeWhen I Looked Up Pokki The Google Results Showed
How To Delete Pokki Virus I Took Action And Downloaded Adwcleaner It Found It I Scanned 4 Times Then adwcleaner dissappred right out of the blue with out permission I clicked the windows button and I saw Start Menu And I learned the virus was still there I went to task manager no results of pooki I went to files to open up adwcleaner than it closed
there is no more Pooki but the start menu is still there how do I uninstall EVERYTHING by the way pooki is not in the uninstall place. What softwares can I use to get rid of it or anything. P.S. I scanned and adwcleaner detected pooki then deleted than disappeared without consent I did not even notice
You can try using the instructions provided in the guide or the recommended anti-malware tool available on this page (or both).