Win64/Longage
Win64/Longage is a Trojan threat that can operate as spyware and collect information about the victim’s personal or professional life. To do that, Win64/Longage can keep track of everything the victim types through their keyboard or directly hack into their webcam and mic.
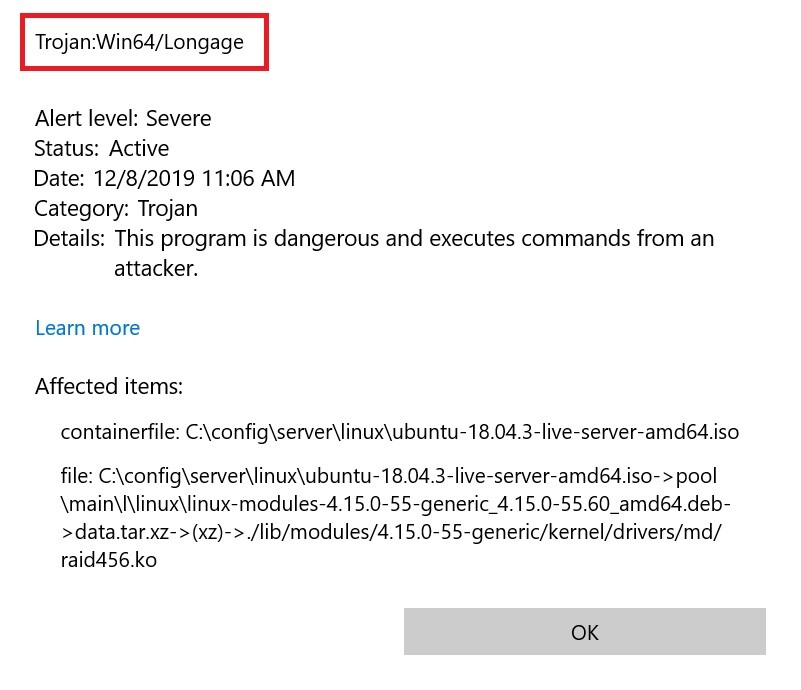
If you’ve been infected with a Trojan horse named Win64/Longage, the following article is exactly what you may need to remove the stealthy infection. Trojans like this one are some of the most dangerous types of malware and are also the most common. Three out of every four malware infections are typically triggered by representatives of this very malware group, according to recent statistics. That’s also the main reason why the Trojans are so well known even among people who are not so tech-savvy. Despite their fame, however, most web users still don’t have a very clear idea of what to expect from a Trojan Horse infection. Moreover, the contamination typically happens very secretly and many people don’t even realize when and how they have been compromised.
That’s why the news about the presence of Win64/Longage on your computer may have come to you as a real shock. In the next lines, however, we will give you some basic information about the capabilities of the Trojans, and once you’ve read that, you can scroll down to the detailed removal guide below, which can help you find and remove Win64/Longage from your system.
A Trojan Horse like the one you are dealing with now can have nearly unlimited ability to damage your system. Typically, this type of malware is extremely stealthy and can remain hidden deep inside the computer without displaying even the slightest symptoms. Something you probably want to know is what this malware is actually trying to achieve in your system. Sadly, there is no way to know that, unless you experience the negative consequences of its activity first hand. Of course, that’s not something you want to experience, and you should better have the Trojan removed before you find out.
Just to get an idea of its danger level, tough, we can mention some of the most common reasons the hackers use Trojans. Theft is one of the top malicious activities carried out by such threats – theft of digital information, that is. A Trojan Horse such as Win64/Longage can easily steal information that you store on your computer and send it to the hackers’ servers. This information may include your personal or work-related files, databases, images, videos and other bits of data that can later be used for various types of cyber crimes. Malware like this one may also secretly collect information about your bank accounts, profiles on social media, passwords, login credentials, etc., and again send it to the online criminals responsible for the malware attack. If it’s a more advanced piece of malicious code, the Trojan can provide the crooks with full remote access to your machine and let them delete, modify, replace, and corrupt anything they like in there. With its help the criminals can even sneak Ransomware inside your computer.
A piece of malware like Win64/Longage can also be programmed to use similar means to spy on you. It can, for instance, record your keystrokes, or hack your microphone or webcam. This way, not only will the hackers learn what you type on your keyboard, but also they will be able to hear and see you.
And, trust us, this alone is a serious enough reason to take all the needed actions to remove the Trojan infection right away. If you have never dealt with such malware before, we recommend you to stick to the instructions in the removal guide below or use a professional removal tool for automatic detection and removal.
SUMMARY:
Remove Win64/Longage Trojan
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Reply