Windows Warning Alert
Browser hijackers such as the Windows Warning Alert can be very annoying and for someone who’s never had anything to do with one before – they can also be pretty startling. All the unwanted changes caused by these programs can get users thinking they might have contracted some virus or malicious program.
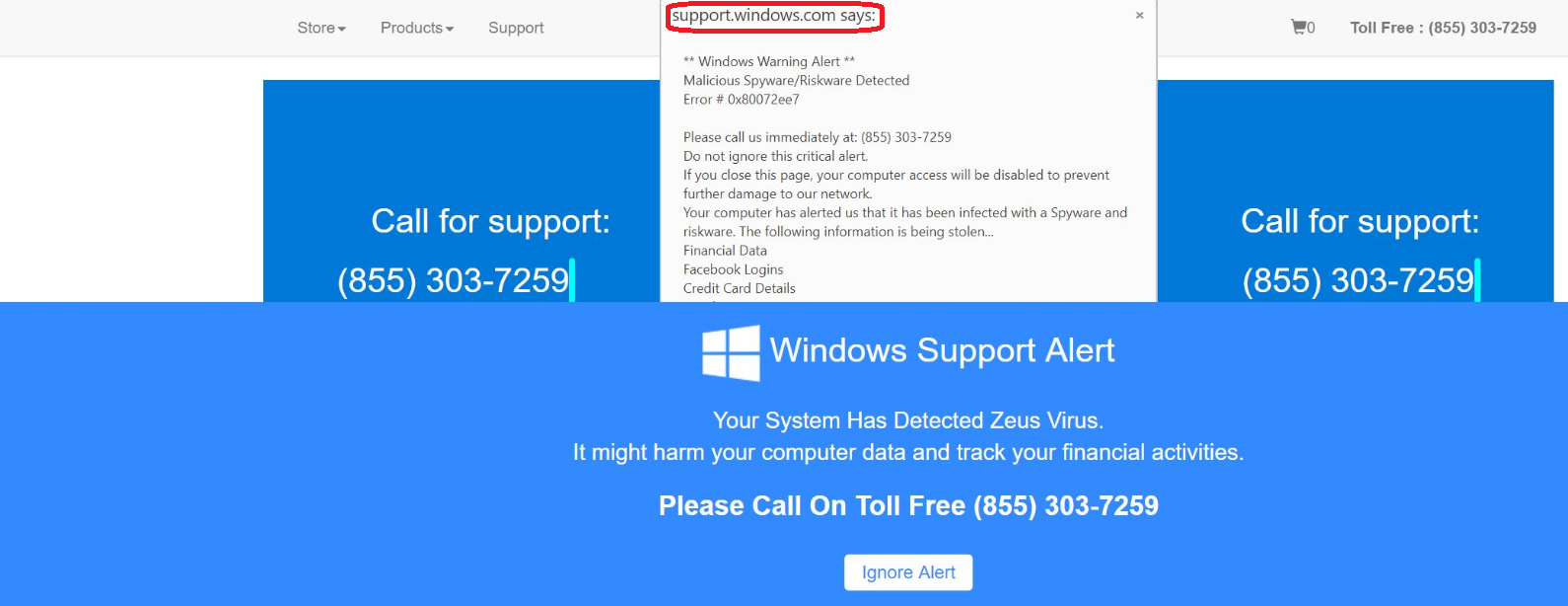
The Windows Warning Alert will display pop up messages.
These changes include a new homepage or default search engine in your favorite Chrome, Firefox, Opera, Edge or other browser of choice. In addition, many users report frequently being redirected to various sponsored websites. Furthermore, every website you visit seems to have clusters of ads on it: popups, banners, in-text links, box messages and more. This sudden bombardment with online ads like this is irritating, frustrating and can frankly be quiet hindering, especially if it’s something you need to deal with on a daily basis. One of the latest browser hijackers that we have been receiving reports about is called Windows Warning Alert Scam. Like most hijackers, removing Windows Warning Alert Scam may take a little extra effort, as opposed to any regular program. And we have just the thing to help you do that – our special removal guide below.
The Windows Warning Alert Scam
The Windows Warning Alert Scam is classified as a browser hijacker and they are online advertising tools, serving the interests of the marketing industry and, more specifically, those vendors and distributors of products and services that get promoted with the help of the all those ads.
Programs like Windows Warning Alert Scam are, as pointed out above, often confused with viruses. In fact, if you go online and search for any given browser hijacker, you will likely find lengthy articles and forum posts describing them as malicious. And the truth couldn’t be farther away. There are some substantial differences between malicious programs such as Trojans, ransomware, worms and the like and browser hijackers like Windows Warning Alert Scam. For one, a hijacker cannot self-install on your system, which is exactly what viruses do. And more importantly, hijackers don’t aim to cause any damage to your computer or to you. As for malware – that is precisely the purpose it exists for!
You could actually call software of this type a rather profitable (and legal!) business model. The developers make money based on Pay Per Click and Pay Per View remuneration systems, whereas tons of products and services gain more exposure in return. So, that is to explain the insane amount of advertising that’s been going on as you browse the web, ever since Windows Warning Alert Scam appeared on your computer. However, as great as this may sound, these advertising-driven programs often also turn to rather unsavory tactics to accomplish their mission. For one, they can track and monitor your browsing activity. That way they can gain a better understanding of your interests at the current moment. And this is important for the purpose of optimizing the advertising campaigns and squeezing out more profit out of those clicks and views. After all, you will be more likely to interact with an ad that’s advertising something of interest to you, rather than just some random ad.
However, seeing as most users don’t know they have actually authorized these processes themselves, they don’t really see why they should tolerate them. This is also one of the reasons why browser hijackers like Windows Warning Alert Scam are generally referred to as potentially unwanted programs or PUPs. Furthermore, they have other unwanted side effects, such as slowing down your computer and potentially just compromising its overall performance. In addition, software of this type can also make your computer more susceptible to external threats, like the viruses we talked about earlier.
But if you authorized the advertising processes of Windows Warning Alert Scam without knowing it, how can you possibly know to prevent them? It’s really quite simple. The vast majority of infections with browser hijackers occur as a result of rushing through the installation process of other software. Windows Warning Alert Scam was likely incorporated in the setup of some program you recently downloaded and installed. The key is to avoid using the more comfortable and ‘lazy’ installation options, such as the Default or Automatic ones. Instead, opt for the more detailed Advanced or Custom options that will give you more freedom to manually customize the setup. That way you will also be able to exclude any added components, such as hijackers, from the setup.
SUMMARY:
| Name | Windows Warning Alert Scam |
| Type | Browser Hijacker |
| Detection Tool |
Windows Warning Alert Scam Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Comment