Winsrv
Winsrv is a malware that belongs to SdBot. bhk family of computer worms and IRC backdoor trojans. Trojans like this one can often operate as backdoors for other malware, such as Ransomware, Rootkits, or Spyware, and assist them in secretly sneaking inside the system, and launching their malicious actions in stealth.
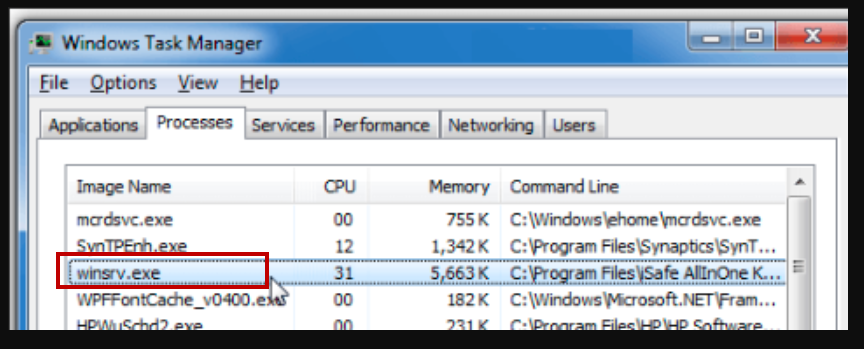
The Winsrv virus helps malware to perform malicious activities
You’ve all heard about the dreaded Trojan Horse viruses – malicious software programs capable of harming your PC and your virtual identity in all sorts of ways. The thing is that, though not all Trojans are the same and not all of them are all that harmful, there’s a good reason why this malware category is considered one of the nastiest, most dangerous and most problematic ones out there. Today, we will focus our attention on one particular example of this insidious virus group – a Trojan Horse that goes under the name of Winsrv Virus. Because it is rather likely that a lot of this article’s readers have actually come here because the malware has already infiltrated their systems, we have made sure to provide all of you with a detailed guide where you can find a number of instructions and steps showing you how you can potentially eliminate the threat and make your PC safe again. In case Winsrv is presently inside your computer system, be sure to visit the guide and carefully execute each one of the presented steps in order to remove the virus and restore your computer back to normal. In addition, we have also suggested on this page an anti-malware tool that, too, can help you in your struggle against the dangerous Winsrv Trojan Horse virus so bear that in mind. One other thing to mention here is that it is still important you read the remainder of the article before going to the guide – the information we are about to share with you will help you gain a better grasp with regards the different characteristics of this particular malware group which would, in turn, enable you to better protect yourself and your PC from such infections in future.
The Winsrv.exe Virus
We already mentioned some of the more common ways in which a virus like Winsrv can be distributed – malvertising, spam messages, shady sites, fake online requests and prompts as well as other similar methods. Now, that you know what to keep an eye out for, make sure that you avoid any web content that seems to have some suspicious characteristics – normally, it isn’t all that difficult to discern potentially dangerous content from such that is unlikely to pose any threat. To wrap this up, we must also remind you to keep a good, strong antivirus program on your PC and update it on a regular basis as this is oftentimes the only relatively reliable way in which you can detect an infection from a virus like Winsrv.
Winsrv what is it?
Winsrv malicious file is used to run malware on your computer or to launch some of its components. Finding this file, the system requires an immediate scan of your computer with reputable antivirus.
Something that most such infections share is their infamous ability to infiltrate one’s system with little to no contamination signs and symptoms. A typical way in which Trojans tend to get inside users’ computers is by presenting itself to its victims as a seemingly harmless and maybe even useful piece of content. It could be a suggested software product that the user is prompted to install when visiting a certain (unreliable) website or it could be an update request that is actually a disguised Trojan Horse download link. Oftentimes Trojans take the form of different files – executables or ones with unknown formats. More tech-savvy or, at the very least, more cautious users might be able to restrain their curiosity and avoid opening such shady-looking content but this is not always the case and, also, everybody can make a mistake and if that mistake is made in the wrong moment, Winsrv or some other similar malware program might get inside their computer. Again, hackers who create Trojans are very good at disguising their viruses, thus making their distribution easier.
Another important thing to point out with regards to this particular malware group is how such viruses are used and what they could actually do once inside a PC’s system. Well, the thing is that Trojans are extremely versatile – most such viruses can be re-programmed and, thus, re-purposed to carry out all sorts of illegal activities. For instance, a virus the likes of Winsrv might get tasked with damaging and corrupting the infected PC’s system or the data that is stored inside it but it could also be utilized for the purposes of espionage and personal data collection which data can then be used in blackmailing or for direct money theft (in case the hackers get their hands on the victim’s banking account’s credentials. Another possibility is when the virus takes over the infected machine and forces it to use most of its resources (RAM, CPU even GPU memory) to carry out certain tasks – cryptocurrency mining, spam e-mail distribution, DDoS attacks, etc. On top of all that, it is even possible that the Trojan loads another virus into the already infected system – a common example is when a malware like Winsrv downloads a Ransomware virus inside the targeted computer.
Bear in mind that the uses we mentioned here are certainly not all possible ways in which a Trojan Horse malware can be utilized.
SUMMARY:
| Name | Winsrv |
| Type | Trojan |
| Detection Tool |
Remove Winsrv.exe Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Comment