*Xatz is a variant of Stop/DJVU. Source of claim SH can remove it.
Xatz
Xatz is one of the newest Ransomware variants. Xatz has recently been unleashed and is now seeking to extort money from its latest victims.
You’re probably here because this awful type of malware has affected you too, but by checking out this site you’re already halfway through solving your problem. You will find a detailed guide on this site that will help you remove this virus from your computer. We will also provide you with some basic information about Xatz, and its specifics, which will help you understand the principles under which it typically operates, and we will also share with you some useful tips to help you prevent future infections. Be warned, however, that Ransomware is by far the worst of all cyber threats that you may face. You should approach the removal guide below with the understanding that some of the encrypted files on your system may not get restored, although we have provided several steps that you can try as an attempt to do just that.
The Xatz virus
The Xatz virus belongs to the fastest growing malware type out there – the Ransomware. You may get infected with Xatz via spam letters, deceitful clickbaits, and pirated software.
The most popular methods used by criminals to spread infections like Xash, Gash involve malicious ads. These are called malvertisements, and the virus will be transmitted to your device once you have clicked on one. Occasionally, ads would be created specifically for that purpose, but most hackers use real, legitimate ads, and infect them with the virus, thus turning them into malware transmitters. Of course, you will be more likely to land on a malvertisement if you frequently go to dubious forums, torrent sites, or sketchy pages. You may also come across a Trojan Horse transmitter when opening an email, or an attachment from an unknown sender. Therefore, it is safer when browsing the web to generally keep away from any banners, popups, or other such advertising materials, and to be cautious when you open different emails in your inbox.
Many infections with Xatz may also occur with the help of a Trojan Horse. The Trojans are typically sent via spam emails inside attachments, making them look remarkably genuine. Cyber criminals are trying to mimic popular online retailers, institutions, and businesses, as this is more likely to gain the victim’s trust. When the attached file is opened, the Trojan gets activated, and then the Ransomware is immediately downloaded onto the unsuspecting user’s computer.
The .Xatz file encryption
The .Xatz file encryption is the consequence of the Ransomware’s attack. Usually, the .Xatz file encryption gets applied to most of the victim’s personal files.

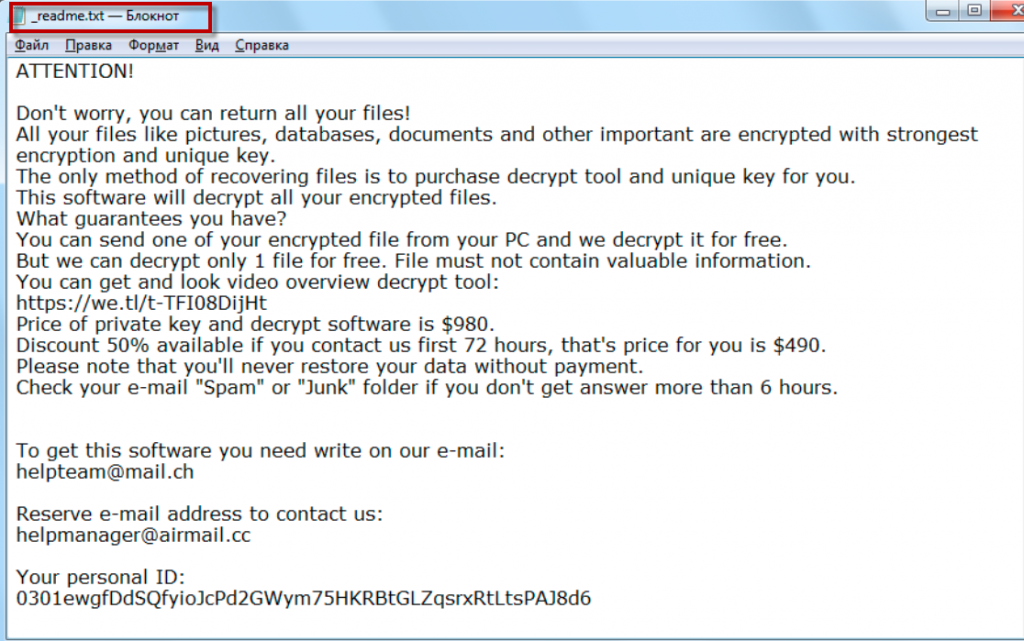
This encryption renders the affected data inaccessible, and requires a special decryption key to be reversed. To obtain that key, however, you will be asked to pay a certain amount of money. A special ransom-demanding notification will inform you about how to make the payment, but security experts warn that going for the payment hides certain risks. For instance, there is no guarantee that once you pay, you will really receive the decryption key. Moreover, there is no guarantee that the key will work. Therefore, our suggestion is to keep your money, and try some alternative means. As a start, you can use the removal guide below, and follow its instructions. Ideally, with its help, you will be able to remove the Ransomware, and get back at least some of your files.
SUMMARY:
| Name | Xatz |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Xatz is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Xatz Ransomware

For the next steps, you’ll need to restart your computer in Safe Mode. This will reduce the number of processes and apps operating on your computer to the most essential ones and will hopefully make it easier for you to spot and remove the ransomware and its entries.
After rebooting your computer in Safe Mode, return to this page for the remaining instructions. To avoid losing this removal guide, save it as a bookmark in your browser and reload it as soon as your computer restarts.
Next, go to the Windows Search bar, type msconfig in it, then hit Enter. Next, at the top of the System Configuration window, click the “Startup” tab:

If Xatz has added any potentially risky startup items to the list, uncheck them and then click the OK button to save your changes. The startup entries associated with the virus will be disabled as a result of this action.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Xatz is a variant of Stop/DJVU. Source of claim SH can remove it.
In the second step, open the Task Manager (CTRL + SHIFT + ESC) and go to the Processes Tab to check whether any malicious Xatz-related processes are running in the background of the system without your knowledge:
Right-click on a process that appears to be dangerous and open the File Location of that process. In this way, you will be able to see the files associated with that process.

Run the files through the free virus scanner below to discover whether they’re infected with malware:

Scan results that identify even a single file as possibly dangerous indicate that the process is infected. In such a scenario, stopping the operating process and removing the malicious files from the File Location should be the next action from your side.
![]()
Next, open a Run window by pressing and holding the Start Key and R together. After that, copy the following line, paste it in the text filed of the Run box and click OK:
notepad %windir%/system32/Drivers/etc/hosts
The Hosts file will open in Notepad as soon as you do this. Search for malicious IP addresses like the ones shown in the sample image below under Localhost, and let us know if you find any in the comments section at the bottom of this page.

![]()
*Xatz is a variant of Stop/DJVU. Source of claim SH can remove it.
Identifying and erasing any harmful Registry entries that the ransomware may have secretly added is the most challenging phase of eliminating Xatz.
Please note that unless you are an experienced user, you should avoid making any manual changes to the Registry and instead remove harmful files from your computer using a professional removal application (such as the one recommended on this page).
If you are confident enough to deal with registry files without harming your system, type Regedit in the Windows search bar and press Enter. This will start the Registry Editor.
When the Editor opens, use the CTRL and F key combination, and carefully type the malware’s name into the Find box. If any entries with that name are detected in the Registry after you start a search, they should be carefully deleted because they may be linked to the infection.
After you’ve cleaned the Registry Editor and closed it, we recommend that you look for dangerous files in a few other locations on your computer.
Type each of the lines below in the Windows Search Field and look for items that were added around the time the ransomware was installed:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Look through the directories for any suspicious subfolders or files, and empty the Temp folder from all of its files.
![]()
How to Decrypt Xatz files
The successful recovery from a ransomware attack necessitates careful evaluation of the specific ransomware variant that has infected you, as well as the strategies and techniques required to remove it. The ransomware’s variant can typically be detected thanks to the extensions it adds to the files it encrypts. If your machine has been infected with the Xatz variant, there is a tool below that may be able to help you recover your data.
Before you jump to decrypt ransomware-encrypted data, however, you must first ensure that the infection has been completely removed from your machine. For this reason, we highly recommend that you carefully delete Xatz using the manual steps above and scan the system for hidden malicious entries using professional anti-virus software or an online virus scanner.
New Djvu Ransomware
STOP Djvu is a new variant of the Djvu Ransomware that is threatening users all over the world. This new variant typically adds the .Xatz extension to the files it encrypts, which helps the victims recognize it.
Unfortunately, as we all know, decoding data encoded with new variants of ransomware may be a tough task. However, there is still hope for the victims of STOP Djvu if an offline key was used to encrypt their files. What is more, there is a decryption program that users can use to recover their data. To access it, simply open the URL below and click the Download button on the page to download the decryptor to your PC.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
The process of decryption
Make sure the decryptor file is ran as administrator and press the Yes button to open it. Before proceeding, read the license agreement and the brief instructions displayed on the screen. To decrypt your data, click the Decrypt button. Please keep in mind that the program may not be able to decode files encrypted with unknown offline keys or online keys.

Leave a Comment