XHAMSTER
XHAMSTER is an advanced form of computer malware capable of entering your computer unnoticed and quickly locking up all of your most important files. XHAMSTER can be described as a file-encrypting Ransomware virus that won’t release the victim’s files until a ransom is paid.
A new Ransomware-based cryptovirus which goes under the name of XHAMSTER is the malware we will be discussing in this article. This threat is very different from other computer threats (such as Trojans, Spyware, Viruses, etc.) because, unlike them, XHAMSTER is not only very hard to remove, but it also tries to secretly perform something very malicious without actually harming the system or corrupting anything on it. What this Ransomware does is, it tries to extort money from its victims via blackmailing.
To do that, the malware gets inside the system without being noticed, usually with the help of some of its numerous transmitters, and applies a complex encryption code to the files stored on the machine. Typically, the file types which get encrypted by the Ransomware belong to categories like documents, images, videos, audios, spreadsheets, and other commonly used files types which may be valuable to the user.
The moment they become encrypted, the victim becomes unable to open them in any way. And this is where the blackmailing part comes into play.
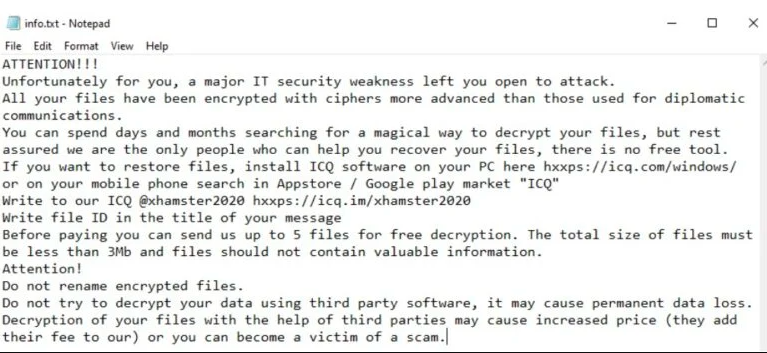
The hackers behind XHAMSTER ask for a ransom payment in BitCoins (or in another untraceable cryptocurrency) – if they receive the ransom, they promise to provide their victims with the corresponding decryption key for their files. The amount of money that the crooks usually ask for may vary and there is often no guarantee that it won’t increase over time.
Typically, the Ransomware infection reveals itself with the help of a ransom-demanding notification immediately after the file-encryption process gets completed. The victims are given only a short period of time to pay the money and are promised to receive the special decryption key needed for their data. Those who don’t pay, however, are threatened to never access their files again.
The XHAMSTER virus
The XHAMSTER virus is a newly-discovered threat of the Ransomware variety – a type of computer infections that target the files of their victims with the goal to lock them. The XHAMSTER virus creates a decryption key that can unlock the files and offers it to the user against a payment.
The users who back up their most important files on a regular basis and keep backup copies on an external drive won’t be heavily affected by the attack of XHAMSTER and Voom. They can easily restore those files and don’t have to pay the ransom to the hackers. The only thing users with data backups need to do, is to safely remove the infection from the computer before they start any file-recovery process.
The removal guide below can be very helpful when it comes to this task, but to ensure that you have successfully deleted all the Ransomware traces, it is also advisable to run a full system scan with a professional malware removal tool.
The XHAMSTER file decryption
The XHAMSTER file decryption is the action required to recover the files that this Ransomware has locked up. The XHAMSTER file decryption, however, can typically only be completed through the use of the corresponding decryption key.

In case you don’t have data backup copies to recover your encrypted information from, it is advisable to explore some alternative file-recovery suggestions, such as the ones mentioned in the guide below. Paying the ransom is generally not a good solution to the Ransomware problem and should only be considered as a last resort option, when every other alternative has failed. This is because, first of all, giving your money to the hackers is a direct sponsorship of their blackmailing scheme, and second, there is no guarantee that you will receive the decryption key from them. The hackers may simply vanish once they receive the payment, or they may decide to ask you for more money if you have agreed to pay once.
SUMMARY:
Remove XHAMSTER Ransomware

The removal of XHAMSTER from a computer requires some preparational work, just as is the case with most harmful software. To begin, we recommend that you save this page by clicking the Bookmark symbol at the top right of your browser’s URL bar. This will help you to easily reload the guide after you restart the system.
And speaking about a restart, the next thing that you will need to do is to restart your computer in Safe Mode by following the steps on this link.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
If your computer is infected with XHAMSTER, it is highly likely that different harmful processes are running in the background of the system without your knowledge. Detecting and stopping these processes is crucial if you want to get rid of the ransomware successfully.
That’s why the next thing that we recommend you to do is to look for processes that consume a lot of resources, can’t be linked to any legitimate program on your computer, or have names that sound like legitimate programs but have a few characters changed here and there. You can do this by opening your Task Manager (CTRL+SHIFT+ESC key combination) and clicking on the Processes tab.
If you find a process that you aren’t really sure about, right-click on it and open its File Location folder to see if it’s actually hazardous or not.

If you don’t have a professional antivirus program at hand, you can use the powerful free online virus scanner below to scan all files in the File Location folder:

Even a single harmful file in the results is a sure sign that the related process should be ended immediately. So, if you find a suspicious file in the scan summary, right-click the process it belongs to and select End Process. After that, go to the File Location folder and remove the files that are harmful.
![]()
When a computer is compromised by malware, there could be modifications in the Hosts file, with added malicious IP addresses that the threat actors can use to hack into the system. For this reason, you need to access the Hosts file by copying the following line in a Run window on your screen. To open a Run window, press the Start Key and R together, then copy/paste the line below and click OK:
notepad %windir%/system32/Drivers/etc/hosts
The Hosts File should open in Notepad. Search for the phrase Localhost in the text and pay attention to any IP addresses that don’t look trustworthy:

If you find something that you believe could be dangerous, please post a comment about it after the guide. In the event that we find something disturbing, we will reply to you with advice on what to do.
Next, close the Hosts file and type msconfig in the Windows Search bar, then press Enter. In the System Configuration window, select the Startup tab as shown below:

You’ll see a list of Startup Items, where you should look for any entries that the ransomware may have inserted. Removing the checkmark from the checkbox of a Startup item you are unsure of allows you to turn it off. Any suspicious entries, such as those with minor alterations in their names or those created by an unrecognized manufacturer, should be checked out online.
![]()
If XHAMSTER’s harmful entries have been added to your system’s Registry, a complete removal of the ransomware may be impossible unless you remove these entries. Therefore, you must search the Registry for any XHAMSTER-related items and delete them in order to remove the threat successfully.
One thing to keep in mind while dealing with Registry files is that doing so incorrectly might result in catastrophic system corruption. If you have any doubts about an entry that appears suspicious, you should use a professional removal program to double-check it rather than delete it.
For a quick search of ransomware-related entries in the Registry, start the Registry Editor by pressing Windows key and R together, then type Regedit in the Run window and press Enter. Then, open a Find box by pressing CTRL and F, and enter the ransomware’s exact name in the text bar. After that, press the Find Next button. Any entries matching the ransomware’s name must be carefully removed.
Aside from the Registry, there are five more locations where you should search for XHAMSTER-related files manually. To open each of them, go to the Windows Search bar, paste each of the locations listed below exactly as they are shown and press Enter:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Filter the list of files in each location by date to look for files that were added recently (an indication that they may be connected to the infection). XHAMSTER may have created temporary files in Temp, therefore it’s best to select and remove all files from that location completely.
![]()
How to Decrypt XHAMSTER files
Once the ransomware has been removed, you’ll want to figure out how to decrypt your files. In order to complete this task, you’ll need a separate set of instructions. Therefore, we encourage you to check out our comprehensive file-decryption guide, and learn more about the best free file-recovery methods explained in it.
Please leave a comment below if you have any questions about removing XHAMSTER. We’ll be happy to assist you. If you face any trouble, use the anti-virus software linked on this page, or try our free online virus scanner to scan the infected machine for hidden dangerous files that are preventing the threat from being eliminated.

Leave a Reply