Xmrig.exe
A virus such as Xmrig.exe, for instance, can be delivered in the form of fake offers, software update notifications, misleading links, different pirated software, torrents, illegal websites or other shady components that you may install on your system. Having Xmrig.exe on your computer may result in serious damage of vital system processes, corruption of software, theft of sensitive personal data like passwords, login credentials, banking details, work-related information, etc.
If you are concerned about the safety of your computer, you most probably have informed yourself about the danger that Trojan viruses represent. These nasty viruses are among the most dangerous computer threats that one may come across on the Internet. In case you land on your system one of them, you should expect all kinds of harm – from system errors and sluggishness to serious damage of the OS, data deletion, disk formatting, contamination with Ransomware and insertion of other viruses, theft of data and much more. In the paragraphs that follow, we will discuss one recently reported representative of the Trojan Horse group named Xmrig.exe. As per the information that we have, this new threat is rapidly gaining more and more victims and causing various disorders and damage. If you have any suspicion that your PC might have been contaminated with this particular threat, we highly recommend that you do not leave this page and read the information that our “How to remove” team has provided below. We have published some very helpful information about the nature of the Trojan horses, the places where they typically can be found, the infection methods they use, the possible harm they may cause and, of course, some useful tips which may help you keep your machine secured against them. In fact, we can offer you help for detecting and remove Xmrig.exe from your system – there is a free Removal Guide below as well as a professional malware removal tool, both of which are meant to assist you in finding the malicious code and removing it.
Specifics of the Trojans.
Something important that needs to be mentioned about the Trojan threats before you decide how to deal with them is that they are extremely stealthy and difficult to detect. These malicious programs rely on all sorts of camouflage in order to infiltrate the system and remain hidden for as long as possible. Typically, to get the victims tricked into clicking on them, the Trojans present themselves as random files, legitimate-looking ads, pop-ups, too-good-to-be-true web offers, spam messages, different email attachments and interesting links. Practically anything could be a potential carrier of this sort of infections. There really are many possible ways of landing such a nasty threat. That’s why, what we usually advise our readers is to be really cautious while surfing the web and to use reliable antivirus software to protect their computer because not everything that seems intriguing is really reliable.
Another very problematic trait of the Trojan horse threats is that they can typically remain unnoticed inside the machine for quite a long period of time. In most of the cases, it takes weeks or even months for the victims to realize that they have been infected and this is because these viruses lack any typical symptoms. Unlike other computer threats which quickly trigger certain visible system errors, significant sluggishness, higher RAM and CPU usage or some unusual crashes, such red flags may totally lack in case of an infection with a Trojan horse (though they can still be present depending on the specific situation). That’s why, the best way to detect and remove such malware on time is to run regular scans with professional antivirus software. In order to ensure optimal protection against the latest threats such as Xmrig.exe it is also very important to keep your security software’s virus definitions updated.
What kind of issues may Xmrig.exe cause to your computer?
The type of damage a threat like Xmrig.exe may cause may greatly vary. The reason is, this Trojan, (as well as most other representative of this malware group) can be specifically programmed to perform different types of criminal activities. Their versatility is practically unlimited and they can be utilized in numerous ways. Such viruses can even insert other nasty viruses such as Ransomware, Spyware, and Worms inside your system. With the help of this threat, the hackers can gain complete remote access to the entire machine and take control of its processes and data. That’s why, to avoid such a scenario, it is essential to detect and remove the Trojan quickly.
SUMMARY:
Xmrig.exe Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
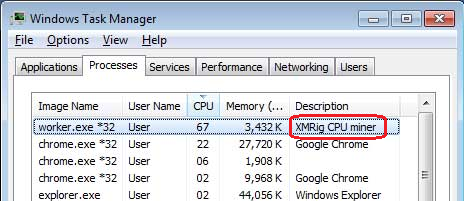
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning. You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone

Leave a Reply