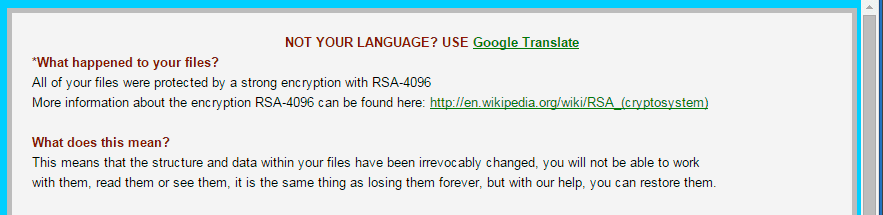
This page aims to help you remove .XXX Virus. These .XXX Virus removal instructions work for all versions of Windows. A message called Howto_restore_files will be generated once the virus latches on to you. This is the newest variant of the Teslacrypt ransomware, called Teslacrypt 3.0. It uses a new encryption method – RSA-4096 – as the beginning of the ransom message attests with the words “All of your files were protected by a strong encryption with RSA-4096.”
Take the time to read this, it is probably important that you do.
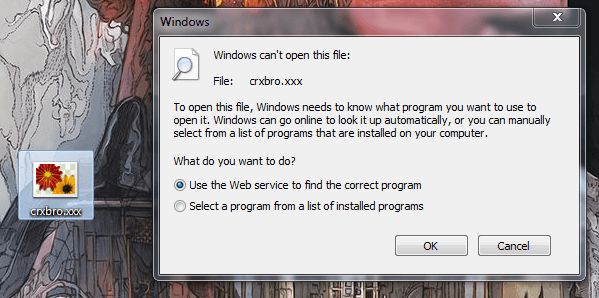
.XXX Virus is a computer virus of the most loathed and feared variety nowadays – Ransomware. You have already saw your files turned to inaccessible gibberish with a strange extension after the files’ names. Also a note of sorts would be posted on your desktop for you to read and try to comprehend the sad truth that you are indeed in a world of trouble. Your files are claimed to be encrypted and the only way for you to decrypt them would be to pay a certain amount of money – a ransom. Here is what the beginning of the message looks like:
Ransomware – methods of operation
Ransomware viruses like .XXX Virus are known to infiltrate the victim’s system via way of another malware. In most cases the most probably culprit would be a Trojan horse. Once inside your computer a scan will be performed and your most often used files will be singled out. Note that the list will not have included and system files. After that the encryption process is on and soon you will be left with pondering what has befallen you. Your old files have been replaced with these encrypted duplicates and you will definitely need a decryption key to break down the encryption, at least that part is true. But there is another way for you to get your old files back, so hopefully we will be able to help you in that regard as well.
Alternatives to paying the ransom
That is probably a part of the article that might really interest you. There are alternatives to paying the ransom and in fact we would encourage you to completely exhaust them before even considering paying money for the decryption key. We are going to elaborate a bit more on that last part.
- First and foremost there are no guarantees or anything close to it that you will indeed get what you will be paying off. Never forget that who will be dealing with are not some pranksters or jokers. These people are flat out cyber criminals and if ever caught will probably spend some years behind bars. So there’s every chance that instead of getting your old files back you will get nothing, or as in some documented cases – demands for more money.
- Secondly – take a moment to try and look at the big picture. Yes, we fully realize this might be hard at the moment when you are personally victimized thanks to the people responsible for .XXX Virus. But if you do you will probably see that the only way for you to stop these people is by refusing them your money. Make no mistake, the ransomware extortion is an enormous stream of revenue for the criminals. We are talking about millions of dollars. There are creating more and more ransomware software and constantly evolving at that. It is up to you and all others affected to stop the stream of money leaking towards the hackers.
- In conclusion: there is always a chance that the online community will find a way to break the encryption. People are constantly working on that, but it is far from easy and even farther from a foregone conclusion that it will be a successful undertaking. Then there’s another way that we are going to explain below in more detail. No guarantees that it will work for everyone, but we believe this is the safest and most probably way that you will get your information back.
SUMMARY:
| Name | .XXX (a variant of Teslacrypt, called Teslacrypt 3.0) |
| Type | Ransomware |
| Detection Tool |
.XXX Virus File Extension Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment