Ymacco
Ymacco is a dangerous computer threat of the Trojan Horse family that installs secretly in the computer and can be tasked with different malicious activities. Ymacco makes changes in the system Registry in order to start automatically when Windows loads on startup.

Most threats of the Trojan Horse family are famous for their versatility and Ymacco is no exception. Once installed in the system, this stealthy piece of malware can secretly execute different harmful and illegal tasks depending on what the hackers who’ve created the virus are trying to achieve. In most cases, users don’t notice the virus’ presence because the malware tries to stay hidden in the system and show as few symptoms as possible. Still, from time to time, users do spot some red flags that tell them there’s something wrong with their systems. For example, Ymacco could lead to unusually high use of CPU and RAM and this could, in turn, affect the computer’s performance, causing slow-downs, screen freezes, unusual errors, etc.
In some cases, it is even possible that a computer infected with Ymacco could experience Blue Screen of Death crashes. A Blue Screen of Death Crash (BSOD for short) is when the computer encounters a serious error that it cannot resolve and so the machine restarts automatically and a blue screen with an error message appears. There could be many different reasons for a BSOD crash, including ones that are related to hardware (rather than software) problems. Still, a blue screen crash is a possible Trojan Horse symptom and so if your computer experiences it, especially if it’s more than once, you should definitely check the system for Ymacco or another Trojan Horse threat.
Ymacco Trojan
The Ymacco Trojan is a harmful piece of malware that can be used for espionage, data corruption, distribution of other threats, etc. The Ymacco Trojan gains persistence on the computer by making various changes to sensitive system settings.
One of the reasons it can be difficult to remove this Trojan is that the threat introduces changes to the system Registry, to the list of startup items, to the Hosts file, and potentially to some other system settings. Unless you make sure to revoke all those changes and find and delete the files that are related to Ymacco, you may not be able to fully delete the virus. In the manual guide shown below, we will explain where to look for the system changes made by the virus and how to revoke said changes. Alternatively, you can use the advanced anti-malware tool that is linked inside the guide to automatically take care of the Trojan. Of course, you can try both the manual removal method alongside the automatic one – this will give you the highest chance of success and should allow you to fully clean your system from all malicious and unwanted software.
Ymacco Virus
The Ymacco virus is a stealthy computer threat that enters the system with the help of other malware or after the user mistakenly downloads and runs a fake software installer. The Ymacco virus is very versatile and can be used for different malicious tasks.
Due to the versatility of the Trojan Horse threats, we cannot give you a single specific purpose for which Ymacco is typically used. What makes the viruses of the Trojan Horse category particularly problematic is that their creators can use them differently on different occasions and choose what type of harm the malware would cause this time after the infection has already occurred. The key is to make sure to delete the threat as soon as you notice its presence in the system. We already told you about the potential symptoms you may notice with this Trojan on your computer so look out for them and if you notice anything, go to the guide posted below and use the instructions and/or the removal tool included in it to secure your system and remove the Ymacco Trojan Horse.
SUMMARY:
| Name | Ymacco |
| Type | Trojan |
| Detection Tool |
How to remove Ymacco Trojan
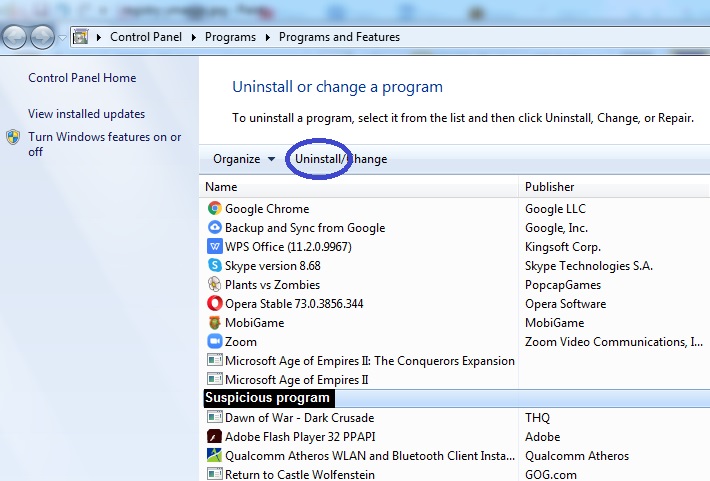
To remove the Ymacco Trojan, you must first try to delete the program that introduced it to your computer.
- Press the Windows key and the R key from the keyboard and type appwiz.cpl.
- Press the Enter button and try to find the program/app that infected you with Ymacco.
- To remove the Ymacco Trojan, select the suspicious program and then select Uninstall.
- Follow the uninstallation steps and if you are asked whether you want to keep anything from the program, select No.
- Restart your computer and see if the virus is still there.
In some cases, the above-mentioned steps should be all that is needed to delete the Trojan. However, oftentimes that won’t be enough and you will need to perform some additional actions to remove Ymacco and secure your PC. If you think the virus is still in the system, we suggest you follow the next steps in the order they are shown.
Step 1: Find and stop the malware process
The first thing you must do is go to your Task Manager and quit the Ymacco process:
- Use the Ctrl + Alt + Delete key combination from the keyboard and then click on Task Manager from the shown options.
- Open Processes in the Task Manager and try to find a suspicious process (or processes) linked to Ymacco.
- Sometimes. this Trojan could name its process as “svchost.exe“. This is the name of a legitimate Windows process and it could be difficult to tell if a process with this name in the Task Manager is from your OS or from the virus. If you see such a process in your Task Manager, right-click and then click on Open File Location.

- If there is more than one process named svchost.exe, open the file locations to all of them.
- In the location folder, scan the files present in it using the following malware scanner available on our site for free:Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is free and will always remain free for our website's users.This file is not matched with any known malware in the database. You can either do a full real-time scan of the file or skip it to upload a new file. Doing a full scan with 64 antivirus programs can take up to 3-4 minutes per file.Drag and Drop File Here To Scan
 Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.
Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared. - If the scanner detects malware in any of the tested files, this means that the process you suspect is linked to the malware and must be stopped so go to the process, select it, and then click on End Process in the bottom-right.
- Check the Task Manager for other suspicious and questionable processes and if you notice any, do the same with them.
Step 2: Enable Safe Mode
It is possible that you may have missed some malicious processes while completing the previous step so it is advisable to complete the rest of the guide with Safe Mode enabled. When Safe Mode is enabled, Windows won’t any processes that aren’t essential to the computer’s functioning to start automatically which should keep the Ymacco processes disabled while you are troubleshooting. If you need instructions on how to enable Safe Mode, you can find them in the provided link.
Step 3: Disable Ymacco Startup entries and refresh the Hosts file
Next, you must revoke some of the settings changes made by the virus.
- Open the Run window again (Winkey + R) and time type mscofig and hit Enter.
- In the newly-opened window, select Startup and see if there are items there that don’t belong.
- Look for entries with unusual names or ones that have Unknown listed under manufacturer and uncheck those from the list.
- Click on Apply and then on OK so that the changes you’ve made would take place.

- Copy this line: “notepad %windir%/system32/Drivers/etc/hosts” and place it in the Start Menu.
- A file notepad file named “C:\Windows/System32/Driver/Etc/Hosts” should show up in the results so open it.
- Check the bottom part of the text, the part where it says “Localhost” and see if below it there is any text.
- If you see text written there, you must copy it and past it in the comments below this article. We will have a look at it and tell you if anything needs to be done about the Hosts file.
- Normally, there shouldn’t be any text below Locahost and if there is, this means that a third-party program has made changes to the Hosts file. To determine if that third-party program is a virus, we must see what the added text is (it would usually be some strange-looking IP addresses).
- If it turns out the added text in your Hosts file is from Ymacco, you must delete it and then press Ctrl + S from the keyboard to apply the changes and save them to the file.
Step 4: Check the system Registry
As we mentioned earlier in the article, Ymacco makes changes in the computer’s Registry to gain persistence and to start alongside Windows on startup so simply removing the Ymacco startup item from the System Configuration program will likely not be enough to stop the threat from launching its processes when you boot up your PC.
Warning!: To complete the current step, you will have to find Ymacco items in your computer’s Registry and delete them. However, it can sometimes be difficult to tell if a Registry item should be deleted or left alone. You must be very careful here and only delete items from the Registry if you know for a fact that they are related to the threat. Otherwise, you could end up causing even more harm to your computer. To prevent this, we suggest consulting us via the comments if you are in doubt and only after that delete the suspicious Registry item(s) in question (if we tell you that deleting them is what you must do).
- Go to the Run window (Winkey + R) again, type regedit, and select OK.
- When your OS asks you for permission to start the app, click on Yes.
- Press Ctrl + F in once you are in the Registry Editor and type Ymacco in the search field.
- Select the Find Next button and delete the first item that gets found (if an item is found).

- Search again, delete the next item and repeat this process until there are no more search results for Ymacco.
- Manually go to this folder in the left panel of the Registry Editor: HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run. - Click on that folder from the left and then find the following item in the right panel and delete that item: Windows Defender Updater = “%User Temp%\cc3a68ce1dad95ce662e1c51f1568e3a.exe / start”.
- Check the following two other locations in the Registry for suspicious-looking folders/items and if you notice anything sketchy there that seems linked to the virus, tell us about it in the comments and if we confirm the folder/item must be removed, delete it from the Registry:
- KEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
Step 5: Delete Ymacco files
To finalize the removal of the malware, you must find the files that it has created in your system and delete them.
- Open the Start Menu and type “%Temp%” in the search field.
- Find the files named “info.txt” and “cc3a68ce1dad95ce662e1c51f1568e3a.exe” and delete those files.
- Type “%LocalAppData%” in the Start Menu, hit Enter, and find a file named “GDIPFONTCACHEV1.DAT” and delete it.
- Restart the computer and use it for a while to see if any of the malware symptoms appear again.
Final Notes
In most cases, if the steps shown in this guide are completed correctly, the virus should be gone by the time you are done. It is, however, possible that some files or settings introduced by Ymacco are left in the computer even after you’ve finished the guide, in which case it would be a good idea to seek the help of a professional anti-malware tool such as the one included on the current page. If you still see signs of the virus’ presence on the computer even after you’ve gone through the guide and completed each step exactly as it is shown, it is best to use the removal program to delete whatever’s left of the Trojan in the system. In addition to cleaning your computer from the malicious program, the removal tool can also keep the machine safe in the future from a wide variety of malicious threats so we recommend using it in order to add an extra layer of protection to the security of your system.

So, i deleted all of the file, runned multiple scann and everything, so for now the computer is fine, i have just only one file, in the “HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main” where is i feel a litlebit sketchy, there are 2 thing, one of them is a (default) settings and a OperationalData his type is REG_QWORD and his value is 0x00000005 (5) so that file is dangerous and i need to delet it, or that file is safe, and im saved from the virus ?
Hi Sandor,
leave this file, you are going to be fine.
Hello, how about this one? I hope you can help me with this.
file: C:\Users\Asus\AppData\Local\Temp\Rar$EXb3312.7111\AdobeAcrobatProDC2021.001.20150\AdobeAcrobatProDC2021.001.20150.exe->(RarSfx)->Crack.exe
containerfile: C:\Users\Asus\AppData\Local\Temp\Rar$EXb3312.7111\AdobeAcrobatProDC2021.001.20150\AdobeAcrobatProDC2021.001.20150.exe
Hi Ejay,
what is this? After i saw this path “C:\Users\Asus\AppData\Local\Temp\Rar$EXb3312.7111\AdobeAcrobatProDC2021.001.20150\AdobeAcrobatProDC2021.001.20150.exe->(RarSfx)->Crack.exe” i assume you are using some cracked software. They often contain malware and trojans that can harm your OS. That is why i suggest to you to download the software provided on this page and do a full scan.