Your iPhone Has Been Hacked
“Your iPhone Has Been Hacked” is a browser-redirecting tool that will keep spamming the browsers on your iPhone with sudden and unpleasant page redirects, and will change their settings (e.g. homepage, search engine, etc.). Additionally, “Your iPhone Has Been Hacked” will also cause obstructive pop-ups and banners to appear on your screen and force you to tap on them in order to remove them.
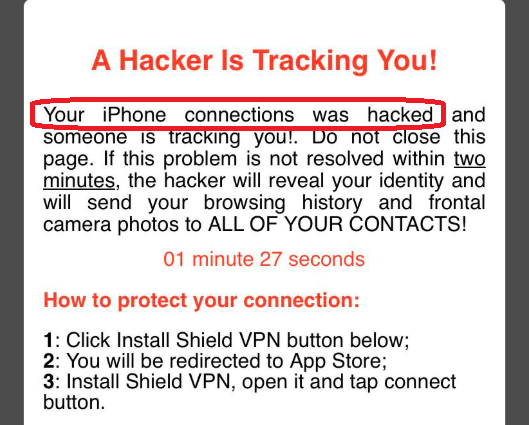
The “Your iPhone Has Been Hacked” pop up will claim your phone has been compromised.
Despite the fact that this unwanted app is technically not a virus, it is most certainly something that you would not enjoy having on your iPhone. The aggressive site-promoting and ad-displaying activities of this software could heavily obstruct your browsing experience and make it very difficult to use your device normally.
In addition, one should also not ignore the potential risks that the presence of such an app on the device could lead to. Bear in mind that not all of the ads and sponsored page redirects that browser-hijacking tools like “Your iPhone Has Been Hacked” generate are what one could call safe. It is, therefore, not impossible to have your Safari or Chrome browser automatically rerouted to some obscure and potentially harmful web location where your device may get infected with viruses, Trojans, and other serious malware threats. It is, therefore, essential that you do your best to avoid any interaction with the pop-ups, banners, and sites “Your iPhone Has Been Hacked” redirects you to until you remove the unwanted app from your iPhone.
Speaking of removal, if you think you may need help uninstalling this undesirable iPhone application from your device, don’t worry – we have you covered. The next lines will give you instructions on how to delete the undesirable software and return your iPhone to its normal state
SUMMARY:
| Name | “Your iPhone Has Been Hacked” |
| Type | Browser Hijacker |
“Your iPhone Has Been Hacked” Removal
You are dealing with a browser hijacker that can restore itself. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
- Locate and clean up your phone’s calendar events if they are infected.
- Find browser extensions related to the threat and how to remove them.
- Ensure your passwords were not stolen or tampered with.
You can find the removal guide here.

Leave a Comment