This page aims to help you remove .zepto File Virus. These .zepto File Virus removal instructions work for all versions of Windows, including Windows 10. This virus is also known as zeptojs or zepto.js
.zepto File Virus on the rise! What you need to know to protect your files
There are many malicious programs throughout the internet, but few of them are as problematic and as hard to deal with as are ransomware viruses. Ransomware is a fairly new type of virus that is very different from any other type. While most harmful programs such Trojan Horses and other malware are there to either mess up your PC’s system, spy on you or steal money from your online bank accounts, ransomware programs will not do any of that. Their agenda is quite different and unique. In this article we will give you some general information about .zepto File Virus – one of the latest of ransomware viruses. For those of you, who have gotten here because their computers have already been infected by the nasty software, we have several possible tips and suggestions for what you can do next. Zepto used to be the most popular ransomware infected, even more then Zeus Virus Detected.
Zepto.js is the reason why you should never open email attachments
As with most other types of ransomware Zepto is most commonly distributed with the help of spam emails. Please note that most email boxes do a decent job of sending most spam emails into the spam folder, where you are unlikely to open them. However, this is not always the case. Some intelligently written spam emails can make it into your inbox and they can carry the file needed to infect your PC. In the case of zepto there are two variations:
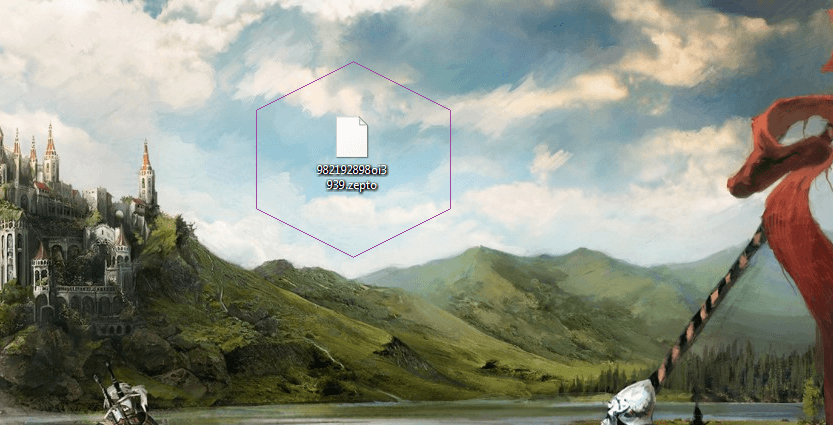
- zepto.js or any other file name ending with .js. When you try to open such a file it will automatically download and run the real virus executable without giving you any indication of the fact. At a glance it will appear that the file did nothing and you’ll probably quickly forget about this oddity, at least
- a .wsf or .docm file. These could be named in a way similar to the zepto.js or again carry an entirely different manner. These two can appear to be less suspicious than a .js file, because they look like a word document or a movie/sound file but in reality they are just as dangerous. The .docm file will either be blank or it will have instructions to make you enable the micro and infect your computer. The .wsf file is even worse – If you try run it it will produce an error and nothing more, but your PC will be infected as the ransomware executable starts working invisible in the background.
You should be extremely careful when handling emails with file attachments. If your work demands you to open emails from strangers make sure you always have these file scanned for viruses before you actually run them on your PC/laptop.
What does .zepto File Virus do?
As we already mentioned, these viruses work quite differently compared to any other malicious software. If your machine gets infected by .zepto File Virus, there will be a certain period during which the virus will stay hidden. During this period, it will copy all your files into encrypted copies, while also deleting the originals. If a file is encrypted, this means that you won’t be able to gain access to that file. Since, as we said, the original files get deleted after they’ve been copied, when the process is over, you’ll be left with files that you won’t be able to open. When it’s all done, the virus will notify you about its presence by showing you a message. This message will tell you that you’re required to pay a certain amount of money in the form of bitcoins, for example, in exchange for the code for the encryption. Bitcoins are a cyber-currency that are very difficult to be traced to the receiver. This leaves the hacker in full anonymity, meaning that there’s almost no chance for them to be brought to justice or for you to ever get your money back, should you pay the ransom. Apart from the ransom demand, instructions on how to get bitcoins and transfer them to the cyber-criminal will be provided in the message.
Possible courses of action
Unfortunately, if you’ve already received the message, there’s not much that can be done. Paying the ransom is one of the possible options but we advise against going for this one since you may be simply wasting your money. There’s just no guarantee that the hacker would send you the code even if you make the money transfer. Therefore, instead of going for the ransom payment, we suggest that you try our guide on how to remove ransomware viruses and restore your files. Know that there are also a lot of free decryptors – these are tools created to deal with some specific ransomware viruses. On our site, we have a list of such decryptors (link in the guide) that are constantly updated. Unfortunately, there’s no decrypting tool for all ransomware programs and since .zepto File Virus is one of the newest, the chances that its code has already been busted are quite low. Furthermore, it’s possible that our removal guide might not be able to resolve all problems caused by this nasty virus. Still, this is a much better alternative, compared to giving money to a criminal. Besides, security software companies are working night and day to come up with solutions for newly created viruses, so don’t lose hope.
Important tips
Lastly, take a few more moments to read some essential tips that may help you fend off potential ransomware infections in the future.
- Have a backup of all your files – this can literally nullify the impact that ransomware may have on your computer.
- Pay attention to your PC’s behavior. If ransomware is currently encrypting your files, you can intercept it. If you notice higher CPU or RAM usage than normal, less free disk space than you think you should have and a general slow-down of your machine, it might be due to the encryption process that’s currently taking place. If that’s the case, shut down your PC ASAP and bring it to an IT professional!
- Avoid shady sites and have a good anti-virus program. .zepto File Virus may get into your PC with the help of another virus, such as a Trojan Horse.
- Be careful when opening new e-mails from unknown senders. If the letter seems suspicious, do not open it! Spam e-mails are one of the most common methods for ransomware distribution.
SUMMARY:
| Name | .zepto File Virus |
| Type | Ransomware |
| Detection Tool | Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
.zepto File Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Reply