Zipe
Zipe is a malicious piece of software that is most frequently referred to as a ransomware cryptovirus. This is because Zipe uses a powerful encryption algorithm to lock its victim’s files and to blackmail them for a decryption key.
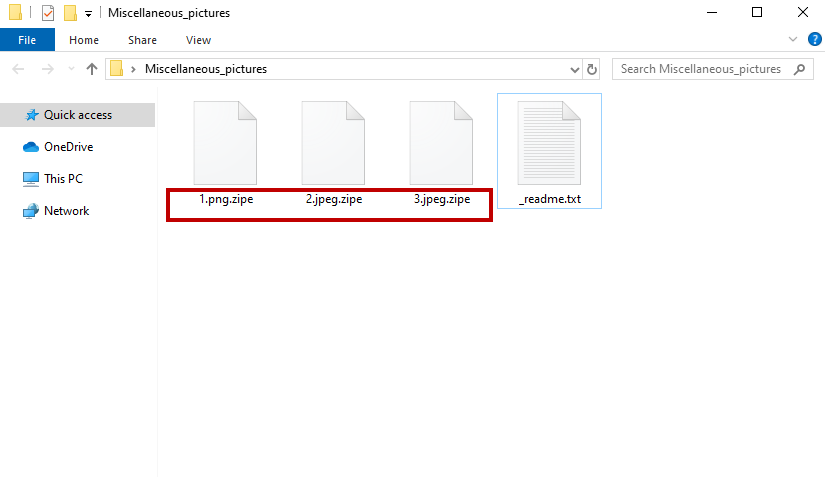
The Zipe Virus will start encrypting your files as soon as it has infected your system.
This type of ransomware virus will usually affect a wide variety of file types including digital documents, text files, images, databases, archives, audio and video files and more. Therefore, if you have been infected with Zipe, it is likely that you will be restricted from accessing a large portion of your digital information. Unfortunately, this can often be devastating for the infected users who don’t have backups of the encrypted files because they may never be able to regain access to them. The attacks of threats like Zipe can have an even more serious impact for big organizations and businesses who may lose data that is essential for their operations.
Sadly, the hackers who create ransomware target everyone and seek ransom payments from their victims in exchange for providing a decryption key. They usually place a ransom notification on the screen of the infected computer where they inform the victims about the attack and give them an ultimatum to transfer the required money. This is a simple tactic that relies on people’s panic and frustration. Moreover, the hackers don’t want you to know that there might be other ways through which the encrypted data can be recovered. That’s why they set a deadline and push you to make an immediate payment. On this page, however, we have published some alternative methods that may help you recover your data from system backups or shadow copies. But above all, we’ve come up with a free removal guide that explains how to remove Zipe from your computer in a quick and reliable manner.
The Zipe virus
The Zipe virus is a particularly dangerous piece of malware that seeks to encrypt user files and uses them as a premise for blackmail. Moreover, the Zipe virus is very sneaky and can remain under the radar of most security programs.
The fact that the process of file encryption is not a harmful process by itself helps the ransomware to remain literally invisible for the antivirus software since it doesn’t trigger any actual system corruption or destruction. File encryption is well incorporated in our daily lives and allows information to be shared between a certain number of people, while shielded from prying eyes. For instance we use encrypted text messages, emails, financial records, and passwords on a daily basis with the assurance that no one can access this information unless they have the decryption key. In case of a ransomware infection the situation is similar with the only difference that our data is encrypted without our knowledge and we are the ones that don’t have the decryption key for it.
The Zipe file distribution
The Zipe file distribution is often carried out via malicious web ads, spam messages and infected email attachments. However, users can get infected with the Zipe file also thanks to a previous infection with a Trojan horse.
Normally, the ransomware virus is attached to some intriguing message that prompts you to click on it. Once you do so, you get infected without any visible symptoms and after some time you are greeted by a scary ransom message on your screen. Paying the ransom, however, is not the only option and it isn’t the most reliable one either. That’s why we encourage you to remove Zipe from your system and give a try to other alternatives that may save you money and your files.
SUMMARY:
| Name | Zipe |
| Type | Ransomware |
| Detection Tool |
Remove Zipe Ransomware
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.

Leave a Comment