*Zpww is a variant of Stop/DJVU. Source of claim SH can remove it.
Zpww File
A piece of data getting turned into a Zpww file is similar to having your favorite novel suddenly translated into an alien language. The transformation is so complete that even the most dedicated linguist can’t revert it to its original form. This is the artistry with which this encrypts files. In more technical terms, ransomware like the Zpww file encrypting virus uses advanced algorithms to convert data into a scrambled, unreadable format. Think of it as an intricate puzzle designed in such a way that only a specific piece, the decryption key, can solve it. Without this unique key, reversing the encryption becomes akin to attempting to read that alien-translated novel without a dictionary. Hence, it’s imperative to secure this key for any hope of restoring the encrypted files to their original state.
The only way to decrypt Zpww ransomware files is through the decryption key, but that key is in the hackers’ hands. Because of this, your options are to pay the ransom they demand for the key or seek alternative ways of acquiring that key. We recommend the latter option. Check out the decryption tool at the end of our post – it can be used for free and may help you recover your files without performing a ransom payment.
In order to remove the Zpww ransomware virus and get your files back, our recommendation is to carefully follow the steps detailed in our guide. After that, you can try the free recovery tool posted at the end of the guide. It could potentially allow you to gain the decryption key for your files without the need to pay a ransom for it.
Zpww Virus
Ransomware threats, such as the Zpww virus, represent a distinct breed of malware designed to encrypt victims’ files, holding them hostage until a ransom is paid. Unlike traditional viruses which might simply damage or replicate files, ransomware takes your data captive, making access impossible without a specific decryption key. The Zpww virus is a member of the notorious Djvu ransomware family, known for its prolific and destructive variants. This lineage also boasts other notorious examples like Itrz and Itqw. While all malware disrupts a user’s digital environment in one form or another, ransomware, particularly from families like Djvu, employs an extortion-focused strategy, making it uniquely threatening in the cyber landscape.
Zpww
The Zpww ransomware virus employs an array of distribution techniques to infiltrate unsuspecting systems. Some of the most prevalent methods include phishing emails embedded with malicious attachments, exploiting software vulnerabilities, and bundling with pirated software or cracked applications. Beyond these, hackers may also utilize trojan backdoors, which grant them unauthorized access to victim systems. The true cunning of these cybercriminals lies in their stealth and manipulation. They craft convincing email messages mimicking legitimate institutions, thereby luring victims into unknowingly activating the ransomware. Additionally, the dishonest people behind Zpww may use drive-by downloads, secretly installing the malware when a user visits a compromised website. By constantly evolving their methods and using sophisticated deception tactics, these adversaries ensure their malicious payloads reach a broad spectrum of potential victims.
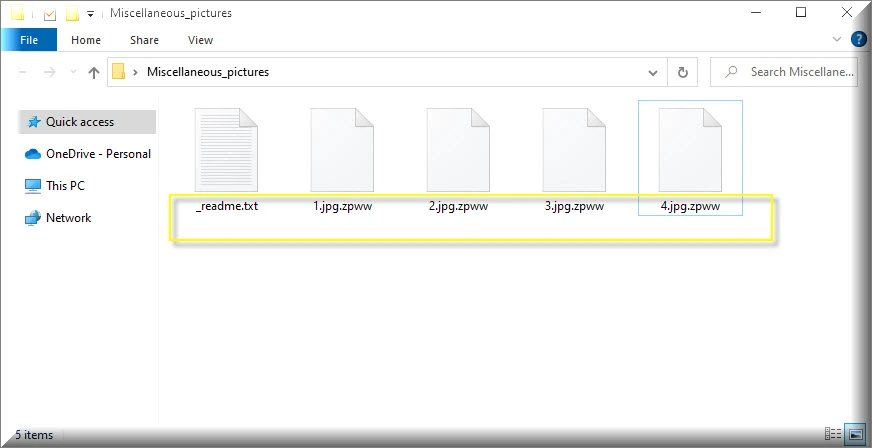
.Zpww
.Zpww is a file extension applied to your files by this ransomware and it signifies that the original content has been encrypted, locking you out from accessing your own data. This extension essentially acts as the ransomware’s calling card, identifying its malevolent activities. Reversing this encryption is not a straightforward task; the encoded information can typically only be unlocked with a unique decryption key, held hostage by the attackers. If you notice the .Zpww extension on your files, immediate action is crucial. Disconnect from the internet to prevent further damage, backup affected files, and utilize reputable antivirus software to detect and remove the ransomware. It’s also recommended to seek expert advice regarding decryption possibilities before considering paying any ransom.
Zpww Extension
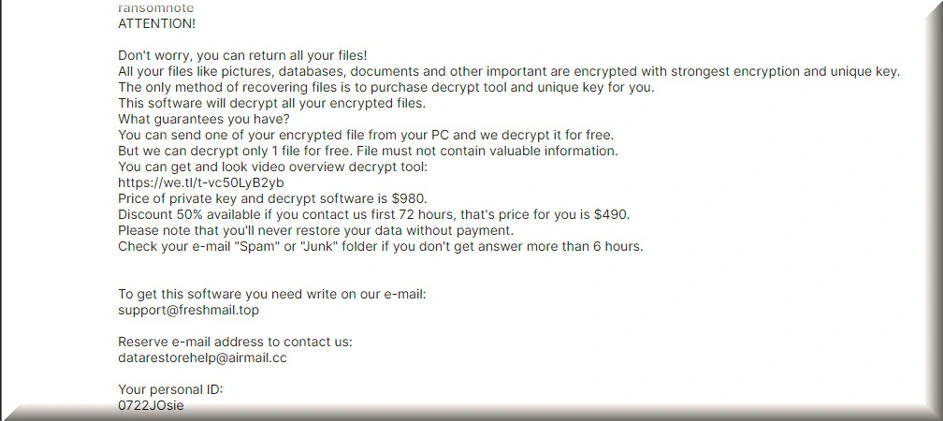
Files tagged with the .Zpww extension are encrypted and are no longer available to the user. This encryption is the ransomware’s method of holding your data hostage. Accompanying this encryption, users often discover a ransom note, a digital letter from the culprits. This message serves multiple purposes: it informs victims of the breach, elucidates the hacker’s demands, usually a sum of money, and might provide “proof” of decryption ability via a sample decrypted file. The note’s tone can range from faux-concerned to overtly threatening, a psychological ploy to incite urgency. Some may even claim a time-limited offer, pressuring victims to pay swiftly if they want to get rid of the Zpww extension. Though couched in promises, paying doesn’t guarantee data retrieval, making the extortion both manipulative and treacherous.
Zpww Ransomware
The Zpww ransomware is indiscriminate, targeting a diverse range of victims, from individual users to large corporations, hospitals to educational institutions. Hackers capitalize on the preciousness of data, knowing that its inaccessibility can cripple operations or induce personal distress. While the immediate reaction might be to pay the demanded ransom, acquiescence is perilous. Payment not only funds cybercriminals’ future endeavors but also offers no guarantee of data recovery. Victims of the Zpww ransomware might end up moneyless and still data-deprived. Instead, consider alternative solutions: maintaining updated backups to restore files, using free professional decryption tools (see below), or seeking expertise from cybersecurity firms. By resisting ransom payments and adopting preventative measures, users and organizations can defy such threats and bolster their digital defenses.
What is Zpww file?
An “Zpww file” doesn’t carry harmful ransomware. Instead, it is a regular user file that’s been encrypted and rendered inaccessible due to the ransomware’s attack. While its content remains unaltered, without a decryption key, it remains locked. To make sure you don’t ever get an “Zpww file” on your computer again, regular system backups are paramount. Store these backups offline or on cloud services to ensure easy restoration. Installing robust antivirus software, regularly updating software, and practicing vigilant online behavior can also deter ransomware threats. If infected, users should first remove the ransomware using trusted malware removal tools. While the ideal solution is using a decryption key, often, resorting to backups or professional decryption services can offer a viable path to data recovery.
SUMMARY:
| Name | Zpww |
| Type | Ransomware |
| Detection Tool |
*Zpww is a variant of Stop/DJVU. Source of claim SH can remove it.
Before you start Before you begin to complete this guide, there are several important factors that you should bear in mind.
- The first one is that it’s best if you keep your computer disconnected from the web while you are trying to eliminate Zpww. This is to prevent any potential interaction and communication between the virus and the server of its creators.
- Secondly, you are also advised to plug out any external devices with storage space of their own (e.g. phones, external HDDs, flash memory sticks, etc.) – this will hopefully prevent the virus from encrypting the data stored on them.
- The third thing we should mention is that you should probably postpone the Zpww removal if you have decided to pay the ransom (something that we discourage) for when you have already acquired the decryption key. If you delete the threat, you may not be able to retrieve the decryption key after paying the requested sum.
- Lastly, may Ransomware threats automatically delete themselves once they’ve completed the encryption of the victim’s files in order to leave no traces of themselves that may help with the decryption. If you think Zpww is already gone from your computer, we still advise you to complete the next guide in order to be sure that the threat is indeed not in the system.
Now, without further ado, let us show you the removal guide.
Zpww Ransomware Removal
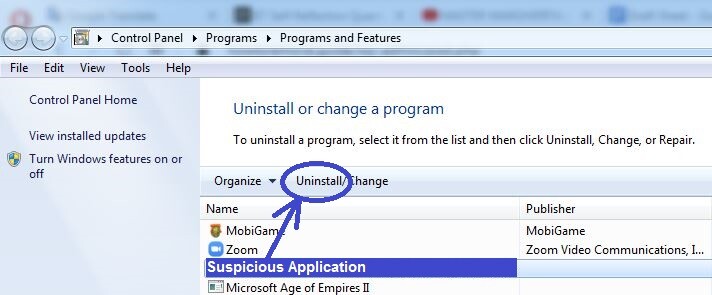
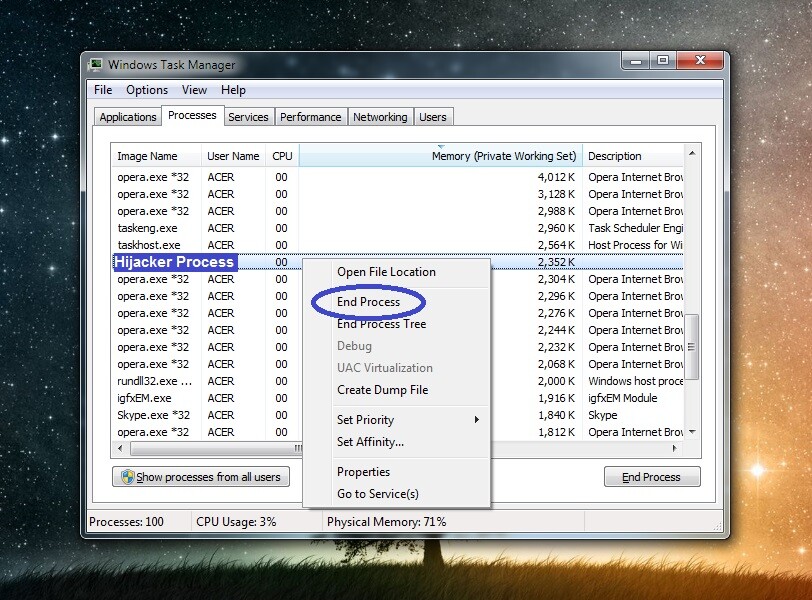
To remove Zpww, it is crucial that you delete any potentially hazardous programs and stop all questionable processes in the PC.
- Use the list of program installs in the Control Panel to see all programs on your computer and eliminate the ones you think may be problematic.
- Check the processes listed in the Task Manager – if you think any of them are from Zpww, quit them.
- Reverse any changes made by the virus in the System Registry, the Hosts file, or the Startup items list.
- Finally, to remove Zpww from your computer, search your PC for virus files and delete them.
Detailed explanations and helpful tips for each step can be found below.
Detailed Guide

There is a list of all the programs on your computer that can be accessed by going to Start Menu > Control Panel > Programs > Programs and Features. In that list, you must look for anything installed close to the date Zpww infected you and uninstall it if it seems suspicious or unfamiliar.
If you decide that a given program should be deleted, select it in the list, then go to the Uninstall option from the top, and follow the steps that appear in the uninstallation wizard that pops-up. Do not allow the uninstaller to keep any data related to the unwanted program on your computer – make sure that everything gets eliminated.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Zpww is a variant of Stop/DJVU. Source of claim SH can remove it.
Press (together) the following keys from your keyboard, [Ctrl]+[Shift]+[Esc] and go to Processes in the next window. Try to find in the list any processes that may be related to the Zpww Ransomware (note that it’s likely that the virus processes are no longer running). There are two main red flags that may show you which of the processes could be from the Ransomware.
The first one is if the process is using unusually high amounts of processing power (CPU) or virtual memory (RAM) as shown in the list.
The second one is if the process itself has an unusual or unknown to you name.
If, considering those two factors and using your common sense and personal judgement, you think you’ve found a process that may be harmful, try finding some information about it on the Internet – chances are that, if the process is indeed from the virus, you will quickly find relevant information that confirms your suspicions.
There’s also one other way to see if the process may be harmful that we recommend. Right-click the suspected process, click the File Location option (the first one), and then use a reliable scanner tool to test the files located there. We’ve provided below such a scanner that you can use for free directly from the current page.


Naturally, if any of the files you scan are shown to be threats, this means the process is likely malicious and should be stopped, so go ahead and do that and then delete tits entire location folder.

The next thing you need to do is get the PC into Safe Mode – in most cases, this should prevent the virus from launching any more of its processes and disrupting your progress with its removal.

*Zpww is a variant of Stop/DJVU. Source of claim SH can remove it.
Now you should make hidden files and folders on your PC visible and then find and delete any Ransomware data present on your PC.
Start by opening the Start Menu, typing in it Folder Options, and hitting the Enter key. After that, select the View section and find and check the Show Hidden files, folders, and drives option. Next, uncheck the Hide extensions for known file types and Hide empty drives in the Computer folder options and click on OK.
After that, paste in your Start Menu each of the next lines and press the Enter button after each one.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete only the most recent files (the ones created since the virus arrived) in each folder except Temp, where you must delete everything.

The next thing to do is to go to the System Configuration settings by typing msconfig in the Start Menu and selecting the first icon. Then you must check the Startup section for questionable and unfamiliar apps/programs/services and/or ones that have unknown developers. Such items need to be disabled after which you should click on OK.
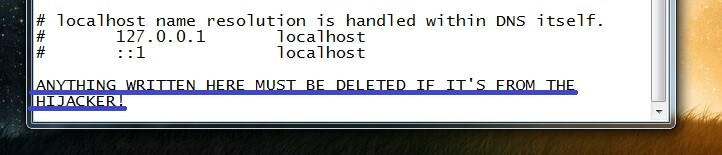
After that, you need to also check the Hosts file by going to Computer/(C:)/Windows/System32/drivers/etc and opening the Hosts file from there.
Select the Notepad app when asked to choose a program and then copy the text written below Localhost (see the picture) and paste it in the comments section. We will have a look at it and let you know if it is from the virus and if it needs to be deleted.

Next, go to the system’s Registry, by clicking on the Start Menu, typing regedit, selecting the first shown app, and then clicking on Yes.
Now open the Registry Editor search by pressing Ctrl + F, type the Zpww name, and perform the search. Any item that gets found should be deleted, after which you must do another search to look for more Zpww items.
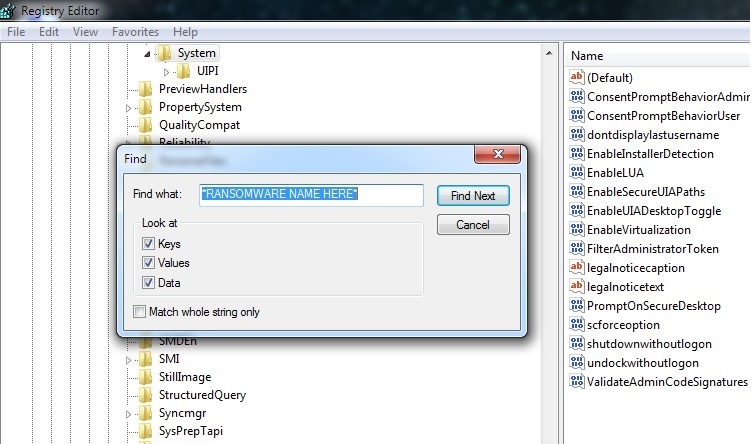
Make sure that everything from Zpww is deleted and then proceed with finding these three locations in the left panel of the Registry:
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
There, look for sketchy-looking items with random names such as “dh9r83h29f498u1398j249f82984r” and if you find any, delete them. If you cannot be sure about a given item, ask for our help through the comments instead of deleting the item, as it may not be from the virus, in which case deleting it could cause further problems.
If the manual steps didn’t help
If deleting the virus manually doesn’t seem to be feasible in your case, we recommend trying out the removal tool posted on this page. The reason why you may need to use such a professional removal program to take care of the Zpww infection is because it is possible that there’s a secondary virus in your computer that is helping the Ransomware remain in the PC in spite of your removal attempts. For that reason, it is highly advisable that you scan and clean your computer with a reliable security program such as the one we just mentioned.
How to Decrypt Zpww files
Enduring a cyber intrusion can be overwhelming. Yet, deciphering the nature of the attack is instrumental in crafting a response. A sudden appearance of unfamiliar file extensions could suggest the type of ransomware you’re up against. In this context, the Zpww ransomware stands out as a rising cyber menace.
Spotting the malicious agent marks the start. The subsequent priority is ensuring its thorough removal, guarding against additional file lockouts or system anomalies. In this pursuit, it’s beneficial to refer to the comprehensive steps detailed previously, augmented by the cutting-edge malware elimination software provided.
STOP Djvu Unveils Another Iteration
Known for its menacing exploits, the Djvu ransomware family’s subcategories, branded STOP Djvu, are equally destructive, encoding indispensable user information. The Zpww emerges as a member of this subset, distinctly imprinting its presence by affixing the .Zpww tag. If you notice such a modification, you’re dealing with Zpww.
While its advent may be concerning, it’s not the end of the road. Importantly, certain files, especially those touched by offline encryption, can potentially be salvaged. A dedicated decryption platform offers some reprieve for those affected. Access it here:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
After securing the software, initiate its functionalities with elevated permissions. An ensuing dialogue box will appear; it’s prudent to opt for “Yes.” Acquaint yourself with the associated terms and directives provided. Trigger the ‘Decrypt’ mode to initiate the retrieval process. While it’s heartening to have a fighting chance, staying vigilant about inherent pitfalls, like unique encryption methods, is imperative.

Dear adddmistartor , i have many many file on my hard dick. i need yur help to fix my file.
thank you so much.
Yousef
Hi Yousef,
did you follow the guide? What kind of help do you need? To recover the files or to remove the virus?