*Aamv is a variant of Stop/DJVU. Source of claim SH can remove it.
Aamv
Aamv is a virus program for Windows computers that targets the files of the attacked victims, seeking to lock them via data encryption. The Aamv data encryption can only be removed using a unique decryption key that only the hackers have access to.
The purpose of this harmful type of computer malware is to force the victims to pay money for the decryption key for their files. As soon as the malware enters a given computer, it secretly launches a data-encrypting process that quickly renders all targeted files inaccessible without the presence of the decryption key on the computer. Once the virus completes its encryption, it notifies the attacked users via a pop-up message about what has happened to their files and how they could restore them. The message typically states that, in order to recover their data, the victims need to make a payment to the hackers behind Aamv. The payment is usually demanded in the Bitcoin currency because Bitcoin transactions are almost untraceable, which ensures that the hackers can remain anonymous. In fact, the use of Bitcoin for the ransom transactions is what allows the criminals behind most Ransomware viruses to evade the law and to keep harassing more and more users without fear of ever getting caught.
The Aamv virus
The Aamv virus is a serious malware threat capable of causing severe data loss by permanently locking the files of its victims. The encryption used by the Aamv virus will keep the victims’ data locked even if the virus itself is removed.

This is one of the main issues that people face when trying to deal with a virus infection of this type like .Coos, .Qlkm . It is very difficult to bypass the encryption if you don’t have access to the access key for it. Even if you remove the virus, the encryption would still remain on the targeted files. This, however, doesn’t mean that you shouldn’t try to eradicate Aamv. Removing this threat is the first step towards securing your computer and potentially releasing your files.
Some users may be wondering if paying the ransom may be a possible solution, to which we must say that it is inadvisable to go for this course of action. The problem with the ransom payment is that you never know if the hackers are being honest in their promises of sending you the decryption key after you pay them. It is, therefore, advisable to first try the potential alternatives, as these do not involve putting your money on the line.
The Aamv file recovery
The Aamv file recovery is the process of making your files accessible again after the Ransomware has locked them. The Aamv file recovery typically requires a decryption key, but there are some other potential alternatives one could try that may also prove effective.
Some of the alternative options will be shown to you in our guide at the bottom of this post. However, you must first complete the removal instructions for Aamv. Removing the virus is highly important because it will prevent it from further encrypting any more data on your PC.
SUMMARY:
| Name | Aamv |
| Type | Ransomware |
| Detection Tool |
*Aamv is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Aamv Ransomware

For the smooth and flawless completion of this guide, we recommend that you Bookmark this page so you can quickly get back to it if you are required to exit it during some of the steps.
Also, it is advisable that you enter your computer in Safe Mode with the help of these instructions: Reboot in Safe Mode

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Aamv is a variant of Stop/DJVU. Source of claim SH can remove it.
Start the removal process of Aamv by going to the Windows Task Manager (press together CTRL+SHIFT+ESC keys from the keyboard) and then carefully searching for ransomware-related processes in the Processes Tab. Look for questionable-looking or unusual entries that eat up too much of your CPU and Memory, but don’t forget that, sometimes, ransomware threats may disguise as legitimate processes and services.

If you have a reason to believe that a given process is malicious, there is a quick way to check it. Simply right-click on it and select Open File Location. Then, drop the files found on that location in our free online virus scanner below and run a scan:

When the scan completes, see the results and if the tested files are flagged as malicious, end the related process and delete the folders that contain them.

Next, use the Start and R key combination to open a Run dialog box on your screen. Once it appears, copy the following command in the text field and click OK:
notepad %windir%/system32/Drivers/etc/hosts
The executed command will open the Hosts file on your computer. Scroll to the bottom of the file and search for “Localhost”. Look for questionable IPs below Localhost, and if you detect any, please write to us in the comments. This could be an indication of possible system hacking.
The image below explains what you should be looking for:

After that, go to your Windows search field and type msconfig followed by pressing the Enter button. This will launch the System Configuration app on your screen:

Once in it, go to the Startup tab and seek for entries that are unfamiliar, have “Unknown” Manufacturer, or seem to be linked to the ransomware. Remove the checkmarks before the questionable entries, and leave checked only the entries you trust. If you are not sure about a given entry in the list, make sure that you google it in order to check if it is legitimate.

*Aamv is a variant of Stop/DJVU. Source of claim SH can remove it.
Next, move to your Registry Editor app – type Regedit in the windows search field and press Enter to open it. Once it gets launched, press CTRL and F keys from the keyboard together and type the virus’s Name in the Find box that appears.
Click on the Find Next button to search for the ransomware in the registry. Delete any results that are found, but make sure that you are very careful because a wrong deletion may corrupt your entire system in a serious way.
Attention! Do Not delete entries that are not related to the Ransomware! If you need any help to detect the malicious entries, please use a trusted removal tool.
Next, go manually to each of these folders by typing them as they are shown (with the % symbol) in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
When you get to these folders, check if the ransomware has added something new to them. When you reach the fifth folder called Temp, make sure that you delete everything that is found there.
If during any of the steps you run into trouble or have questions, we encourage you to leave us a comment below this post, so we can assist you.

How to Decrypt Aamv files
After you have removed Aamv from your computer with the help of the steps above, the next thing that you may want to do is to recover your encrypted files. This task may not be that easy, but the information below can surely help.
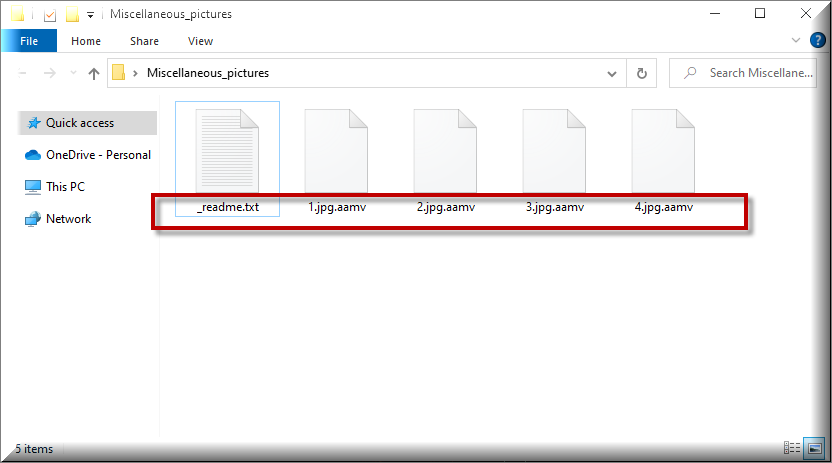
Data encrypted by ransomware may be difficult to recover, especially for victims who are faced with such a threat for the first time. Moreover, ransomware decryption techniques may differ depending on the ransomware version that has attacked the system, making data recovery even more difficult. For this reason, it is very important to identify the variant you are faced with in the first place. Usually, you can look at the file extensions of the encrypted files to find this information.
Even though most victims are impatient to get back their files as soon as possible, data recovery should not begin before a full virus scan with a sophisticated anti-virus application is run on the compromised computer. What is more, you shouldn’t even look into ways to recover files until the virus scan shows that there are no viruses or traces of the infection because if you skip this step, any files that you may potentially recover may become encrypted again.
New Djvu Ransomware
STOP Djvu ransomware is a newly discovered variant of ransomware that encrypts data and demands payment from victims. This malware has been reported worldwide, and victims have reported that it appends the Aamv extension to encrypted files. The good news is that people who have lost data due to the Aamv encryption should not pay the ransom, since decryptors such as the one in the link below may be able to assist them in recovering their information.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
You may decrypt files encrypted with Aamv by downloading the STOPDjvu application from the URL and executing it, but you should first review the license agreement and read the instructions for use on the page. We have to note that despite the fact that the decryptor seems quite powerful, it does have several restrictions. This program can’t decode all encrypted files, especially if they were encrypted online or with an offline key that is not in its database.
If you find yourself in trouble and need more help to remove Aamv, feel free to use the professional removal program linked on this page and this free malware scanner that can check individual files.

Leave a Comment