What is the Access Virus?
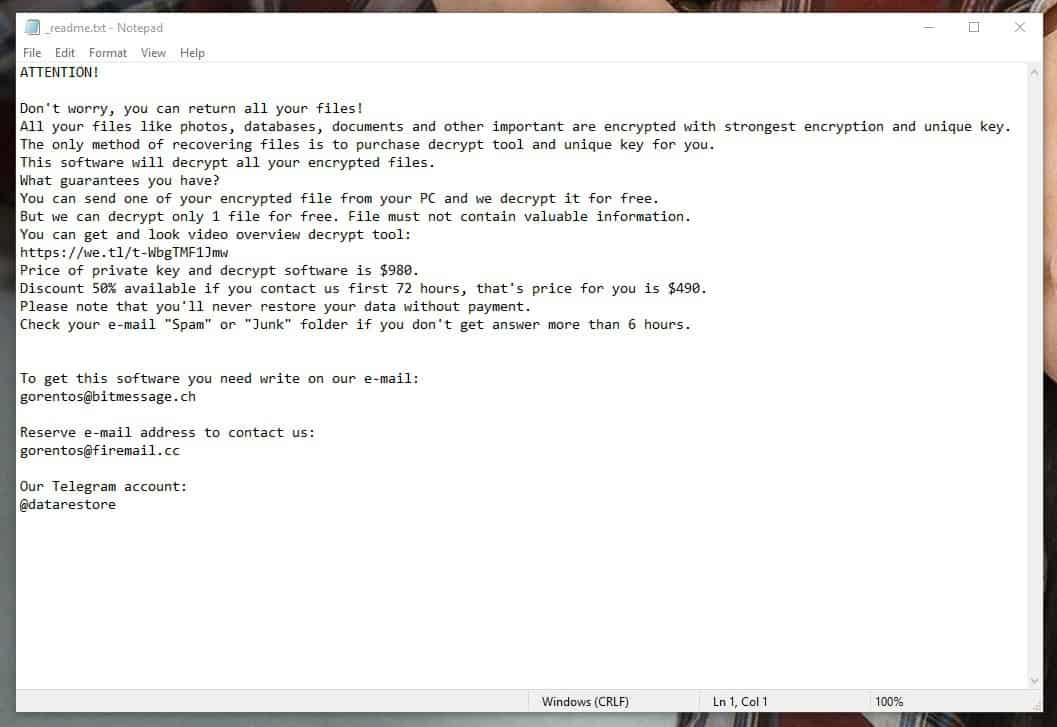
Most computer users have probably already heard about Ransomwa threats that the Ransomware cryptoviruses like Access represent and just how awful it could be if you get attacked by one such piece of malware. One of the main problems with these infections is how sneaky they are and how difficult (and oftentimes not fully possible) it is to deal with the aftermath of their attack. We are saying “attack”, but in reality, a Ransomware cryptovirus (Ndarod, Adame) wouldn’t exactly harm anything in a direct way – the way it causes damage is more subtle. Instead of doing something bad to your system or corrupting your files in some way, a typical cryptovirus would simply encrypt your data – this doesn’t harm the files, it simply keeps them locked from people who do not have the decryption key that corresponds to the applied encryption code. Needless to say, you wouldn’t have access to this key if a Access or some other cryptovirus has locked your files. The only people who would initially have possession of the said key are the hackers behind this malware program. And, after your files are made inaccessible, the hackers would tell you that if you pay them money, they would send you the access and you’d be able to open your files once again. Most security specialists that research such Ransomware infections, however, state that paying the requested ransom money is not a very advisable option. After all, the people you’d be sending your money to are anonymous Internet criminals – hardly the type of people you’d like to trust with your money. They may easily decide to not send you anything even after you have followed every instruction related to the payment of the ransom and sent them the demanded sum. Besides, there’s also the possibility that the key they send you (if they send you anything in the first place) may not work properly and may not decrypt your files. Of course, even if his happens, your money would still be gone for good – this isn’t like buying something and you cannot hope for any refunds from such hackers.
Our suggestion in how to handle .access files
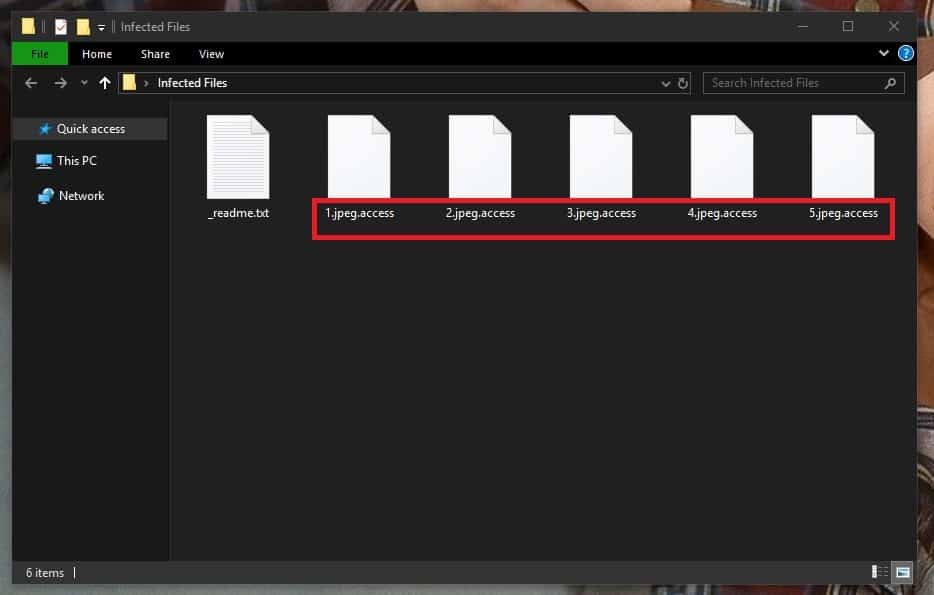
If you are indeed one of its many victims, then here is what we think may help you deal with this predicament. Down below this paragraph, you will find a guide with removal instructions for Access – follow the steps and, if you need the extra help, use the suggested removal software tool you’ll see linked below to eradicate the cryptovirus. After you do that, you can begin your attempts to restore your files through alternative means. We have a couple of file-recovery suggestions in a separate section added to the guide that you can use as your starting point. We don’t promise miracles and you should know that even our guide may not always work but it won’t cost money and would still allow you to eliminate the infection itself.
SUMMARY:
Access Ransomware Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply