This page aims to help you remove the .Adame Ransomware Virus for free. Our instructions also cover how any .Adame file can be recovered.
.Adame
Adame is a dangerous computer virus that will keep your files inaccessible to you until you fulfill the demands of the hackers. Adame runs an encryption process in the system, thereby locking the files. After this, Adame demands a ransom payment for the decryption key.

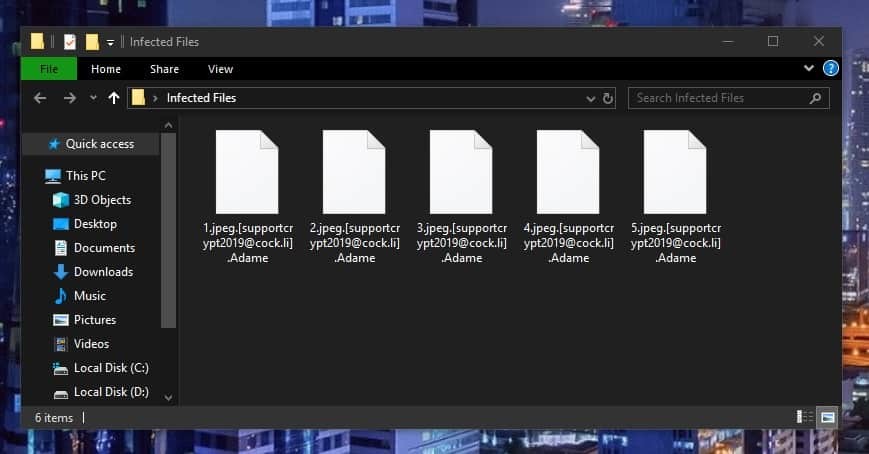
The article that you are going to read will help you get better acquainted with a newly launched computer virus identified as .Adame Ransomware. The virus class under which .Adame falls is the popular Ransomware – harmful form of software which employs encryption in order to seal the users’ personal files. Right after the encryption operation has been fully carried out, a pop-up message telling you about the virus infection gets generated on your PC screen. The daunting Ransomware message informs the targeted user about the virus invasion and also about the fact that the cyber criminals who stand behind it request a ransom transaction in return for the locked data. The ransom payment is needed for the successful unsealing of the locked computer data with the help of a special decryption key and unless the user pays, the personal files could possibly stay inaccessible for good. If you have come here searching for help because your data files have already been taken hostage by the .Adame Virus, it is advisable to read through the next lines and then visit our manual guide for eliminating Ransomware.
The Adame Ransomware
Adame is a virus that locks personal data in Windows computers. Adame is categorized as Ransomware because it demands a ransom payment from the users who want to be able to access their files again. If no payment is made, the files stay locked.
Whenever attacked by Ransomware cryptovirus such as .Adame, you need to bear in mind that malware programs of this class have a unique approach and way of completing their agenda. An enormous problem with Ransomware is the fact that many software security applications have difficulties spotting the infection and preventing it from finishing its file encryption process. What can cause the ineffectiveness of many software security applications would be the fact that malware pieces like .Adame, .Godes, .Lokas are usually not likely to actually cause any harm to the system or the data on the infected machine. The file encryption code the nasty virus applies to prevent you from accessing your documents doesn’t really cause damage to the data. It is just that the sneaky Ransomware turns this harmless process against you. The sealed files are on the system, yet, they are inaccessible without the application of a special decryption key.
The Adame File
Adame is a Windows malware virus that blocks access to important files stored on the attacked computer. Adame doesn’t release the files until the user carries out a ransom payment following the instructions provided in a ransom note that the virus generates.
Usually, the success of any Ransomware infection very much depends on misinformation, intimidation and stress and panic among the users who have become victims of this virus. Logically, what we focus on in this brief article is to help you get well informed about all the features and potential solutions to those infections, to make sure that you aren’t easily intimidated. Moreover, you should know that paying the ransom never guarantees you that the files are going to be unlocked and things will be back to normal. That’s why our advice is to seek other possible options, which aren’t associated with paying the requested money because even completing this payment cannot benefit you much. The crooks may simply disappear with the money without sending you anything in return or the decryption key they give you may not work. And the worst is you won’t be able to get your money back. For this reason, we suggest you to first try out our recommended alternative – the directions inside the Guide at the end of this post. We have even tried to formulate a way to decrypt data from system duplicates, which is additionally shared with you down below.
SUMMARY:
Remove Adame Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Reply