This page aims to help you remove [email protected] for free. Our instructions also cover how any [email protected] file can be recovered.
[email protected]
[email protected] is an infection that uses encryption to block the access to your files. If you have been infected with [email protected], .Nesa or .Karl we’re sorry to inform you that what has compromised your computer is a Ransomware cryptovirus.
In short, the way this infection works is it encrypts the files on your computer, and then it offers to give you the key for the decryption in exchange for a ransom. Sadly, removing the virus here won’t be enough to restore those files – they’re going to stay encrypted until the corresponding decryption key gets applied to them. In this guide, however, we will give you a step-by-step manual on how to proceed after the encryption of the information in your system.
The [email protected] virus
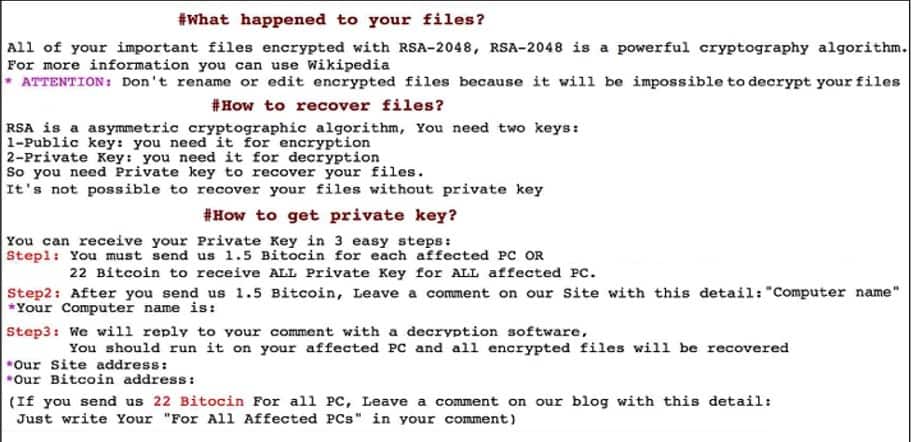
The [email protected] Virus will leave a ransom note, similar to this one
The [email protected] virus can sneak inside your computer secretly. If the [email protected] virus succeeds in its secret file-encrypting operation, it will inform you about the ransom demand via a note displayed on your screen. The message will typically notify you that your personal files have been encrypted, and will require you to send a certain amount of money as a ransom to the hackers who stay behind the infection. In return, the crooks will promise to send you a special encryption key which is supposed to reverse the encryption. Typically, if you don’t pay within a certain deadline, the ransom-demanding message may say something about doubling or tripling the ransom amount, or even destroying the decryption key. This is typically done to put some pressure on the victims, and prevent them from searching for an alternative solution.
The [email protected] file encryption
The [email protected] file encryption is the most challenging aspect of the Ransomware attack. Breaking the [email protected] file encryption may not be possible without the corresponding decryption key. However, paying the hackers may also not be a good idea.
The cases of Ransomware infections are rapidly increasing in numbers every day, and one of the main causes for this is the stealthiness of those threats. The hackers spread such viruses via various web locations, and blackmail the web users to transfer money to their cryptocurrency accounts. Cryptocurrencies (such as Bitcoins) are almost impossible to trace, so if you pay the requested sum, tracking it back to the receiver is almost impossible.
Also, here’s one other thing to consider: people who try to hack into the computers of others and extort money from them shouldn’t really be trusted. There is no guarantee that they will send you the decryption key they’ve promised you, or that it will work. That’s why we suggest you don’t pay them the ransom, and instead first explore the alternatives you can use to remove the infection, and restore your files without paying.
To keep your computer safe, it is needless to say you should always have a trusted antivirus program, and you should avoid opening messages from unknown senders, particularly if they include attachments or redirect links. You should also keep away from obscure websites that could possibly hide viruses like this one within their pages.
SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Detection Tool |
Remove [email protected] Virus
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

please-i-have-virus-on-my-pc-which-make-it-to-malfunction
please i dont have money and i living in iran and my all pictuer is encryption
please i have virus i do not have money please remove the virus
i don’t know how
i don’t have bitcoin please please another way please i poor guys i m from algeria please i begging u please
Plzz help i am a poor guy i dont have bitcoins and i dont want my data back i just want to finish it from my pc it just encrypted my windows usb
If you just want to remove the virus, follow the instructions from the guide and/or use the recommended removal tool – this should be enough to eliminate the malware.
Iam from Egypt