Ahui may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Ahui is a variant of Stop/DJVU. Source of claim SH can remove it.
Ahui
Ahui is a new addition to the infamous ransomware virus family and dealing with it is not easy. Ahui has most probably encrypted your valuable files and is currently preventing you from accessing them.
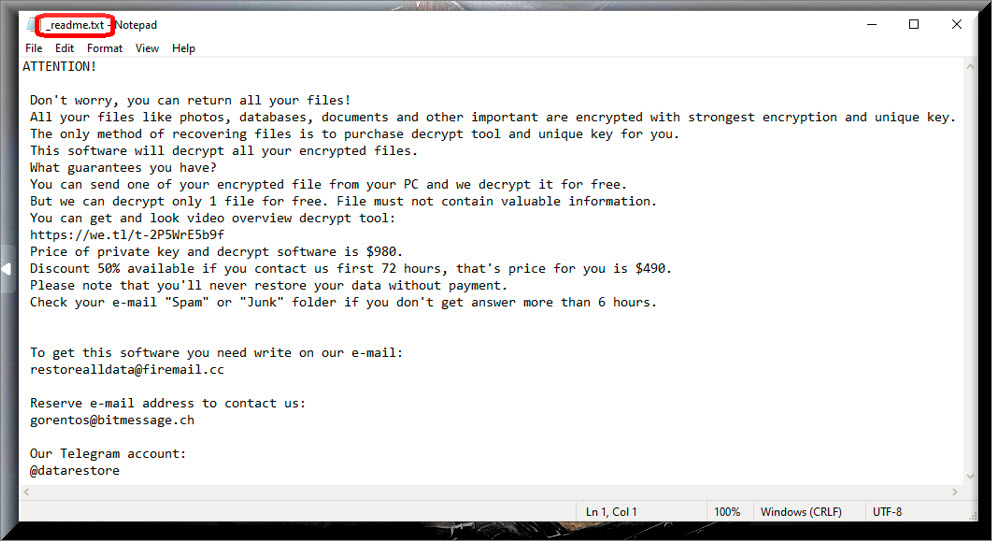
What’s more, some anonymous hackers have most probably placed a disturbing ransom notification on your screen and asked you to pay a ransom in order to free your data. You don’t have to deal with these criminals alone, though. We will try to give help you on this page so check out the alternative courses of action that our team has suggested and carefully decide what would be the best way to recover your files without paying the ransom.
Among all the known computer threats, this is definitely among the top worst forms of virus programs. Ransomware infections such as Ahui infiltrate users’ computers and typically place a complex encryption on their most valuable files or block the access to the whole PC. This is obviously a criminal scheme for online blackmail because the hackers who create and use these cyber threats ask their victims to pay a certain amount of money as ransom in exchange for their regained access to the files. When the ransomware infection targets the user’s files and locks them through an encryption process, a decryption key is normally offered for a limited period of time and the victims have to purchase it from the crooks if they want to get things back to normal.
The Ahui virus
The Ahui virus uses advanced methods to infect more and more computers and the infection typically happens in complete stealth. The Ahui virus rarely has any visible symptoms and can hide in various online transmitters.
For this reason, its timely detection and interception are oftentimes rather unlikely. The hackers typically insert the ransomware in seemingly harmless ads, links, pop-ups, legitimate-looking websites, spam messages, email attachments and social media shares which the average user would oftentimes be unable to recognize as malicious. Most of the infections happen when the victims are misled about the real nature and purpose of the malware transmitter and interact with it.
Another way to end up with Ahui, Neon or Neqp on your PC without having a clue about it is if a Trojan horse compromises your system. This very popular and nasty malware can insert other viruses inside your system with ease and ransomware infections can also get distributed in this way. Sadly, many antivirus software programs may not prove to be effective in the timely detection of the threat. That’s why it is very important to invest in a reputed security tool that is from a good developer and which has real-time and quality ransomware protection.
The Ahui file encryption
The Ahui file encryption is very complex and makes it very difficult to deal with. However, there are workarounds for the Ahui file encryption that don’t involve purchasing a decryption key from the hackers.
Paying the money is, of course, a possible course of action and might sometimes actually get your files back but there are no guarantees that you won’t simply waste your money in vain. Generally, it is inadvisable to pay if you can help it because in many cases you might not receive any decryption details in return even if you have closely and accurately followed all of the hackers’ instructions.
Our team doesn’t recommend that you give your money to the criminals either, simply because you cannot trust their promises. They may vanish with the ransom payment without sending you a decryption key or they may blackmail you for more money without giving you any guarantee for the future of the encrypted files. Keeping the nasty Ransomware virus on the computer is also not a good idea because, as long as it is present in your system, the machine is not safe for further use.
That’s why, what we would suggest you do first is remove Ahui and take the matters in your own hands without relying on the hackers. For that, you can use the professional Ahui removal tool or the free manual guide available on this page. There you will find step-by-step instructions as well as some file-restoration tips. If you have external backups of your data or copies on a cloud or other devices, you can use them to recover some of the encrypted files. Contacting a professional of your choice is also an option. Take the needed time to figure out what the best course of action would be in your particular case and try to avoid sponsoring the ransomware’s criminal scheme as much as possible.
SUMMARY:
*Ahui is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Ahui Ransomware

To begin the process of removing Ahui, first you need to unplug any external devices (such as USBs and other connected devices) from the infected system. Next, disconnect the ransomware-attacked machine from the Internet. In this way, the ransomware (and any other malware that could possibly be lurking on the system) will no longer be able to get instructions from its servers through the Internet, and the devices that have been disconnected from the computer will not be damaged.
Safe Mode reboot will be necessary as a second step. This link has instructions on how to boot your computer in Safe Mode if you don’t already know how. Once the system reboots, return to this page (you may bookmark it right now to access it quickly later) and then follow the instructions in step two, which are listed below.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
*Ahui is a variant of Stop/DJVU. Source of claim SH can remove it.
In the second step, you will need to use the Ctrl, Shift, and ESC keys together to open the Task Manager on the computer that has been infected. Select the Processes tab from the list of tabs at the very top of the screen. Once you’ve sorted the processes by memory and CPU use, you can go through the list and check for any processes that are eating up a lot of resources with no obvious reason or processes that have strange names.

Right-clicking on the questionable process and then choosing Open File Location from the context menu is the next thing to do. This will allow you to scan all the files associated with the process and check them for malware using the scanner provided below.

When the scan is complete and the File Location folder is found to contain threats, the related running process must be stopped. Right-click on the process that contains dangerous files and select End Process from the context menu to end it. After that, remove the files detected by the scanner from their respective folders to clean up your system.

As a next step, you’ll need to press Win+R at the same time to open a Run box. Type the command listed below in the Run and hit Enter to execute it.
notepad %windir%/system32/Drivers/etc/hosts
If you do this, a file titled Hosts will open in a Notepad window. You may check to see if your Hosts file has been changed without your knowledge by searching for the phrase “Localhost” in the file’s text and looking for any strange IP addresses that are listed below. If you notice something unusual, you are encouraged to report in the comments section of this article. This will allow us to examine them and provide you with advice on the next steps to take.

Next, open a System Configuration window by entering “msconfig” in the Windows Search box that is accessible in the Start menu and then clicking the Enter key on your keyboard. Choose the “startup” tab and look at the startup items listed under that tab. These are the items that are set to start with your system. Remove the tick from the checkbox next to any startup item that you believe is linked to the ransomware and click “OK” to apply your changes.

![]()
Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
The registry is a key system location that a threat like Ahui can access. Therefore, a comprehensive search in the Registry Editor is a step that you should not ignore when trying to delete any files connected to Ahui. To access the Registry Editor, type “regedit” in the Windows search bar and press Enter. After the editor opens, open a Find window by holding down CTRL and F at the same time. This box allows you to search the registry for files linked with the infection. Start your search by typing the name of the danger you’re searching for in the Find box and clicking Find Next.
Attention! Ransomware-related files may be risky to delete from the registry, especially if you are not familiar with malware removal. That’s because removing anything wrong from the registry might have a negative impact on your computer’s performance and stability. To avoid this risk, please use the professional malware removal application listed on this page or another reliable malware-removal software of your choosing to ensure that the ransomware-related files have been fully removed from the system.
In addition, we recommend that you search for other files that may be associated to the infection in the following five locations:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Type each of the terms above in the Windows search bar (including the percent symbol) and press Enter to open them. Search for anything unusual, such as files and folders with strange-looking names, but don’t remove any files unless you’re very convinced they’re connected to the danger. You can remove potentially dangerous temporary files by selecting the files in the Temp folder and then delete them with the delete key on your computer’s keyboard.
![]()
How to Decrypt Ahui files
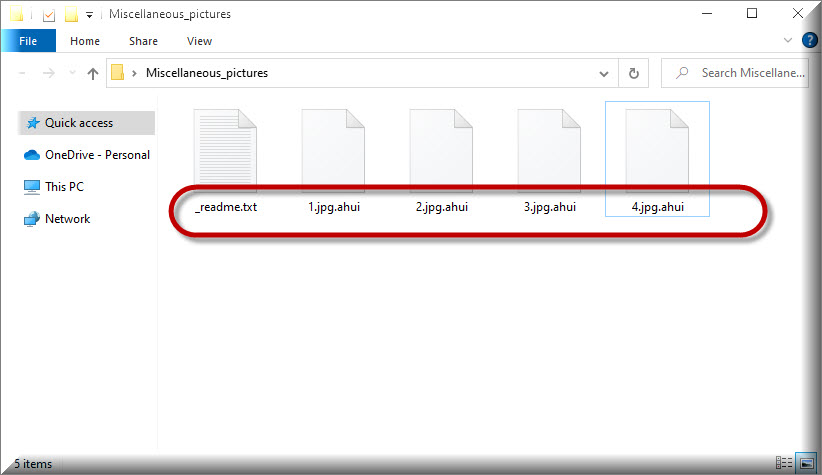
If you’ve never dealt with it before, decrypting your ransomware-encrytped data might be a difficult undertaking. One of the first thing that you should do if you have been attacked is to look at the file extensions that have been added to the end of the encrypted files. This will give you an information about the exact ransomware variant that you are dealing with.
Before commencing any data recovery procedure and looking at any file recovery solutions, make sure your computer is virus-free. You can do this by running a thorough malware scan with a reputable anti-virus tool and carefully removing any malware that has been detected.
New Djvu Ransomware
STOP Djvu is a ransomware variant that has recently emerged on the malware scene and is encrypting files with a complex encryption. Victims of this infection may recognize that they have been infected if they find the .Ahui extension attached to the end of their files. If you find yourself in this situation, you should not pay the ransom since there are decryptors available, such as the one listed below, that may be able to retrieve some of your encrypted data without giving your money to the crooks.
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
To give this decryptor a try, first open the link above, download the STOPDjvu.exe file and carefully read the license agreement and the attached instructions. Next, run the executable file as an administrator and follow the on-screen instructions. Keep in mind that this program may not be able to decode all files, especially if they were encrypted using online encryption techniques or unknown offline keys.
If manually deleting Ahui doesn’t work, and you have any concerns that the ransomware-related files are still on your system, you should use the recommended anti-virus software in the article to swiftly and efficiently remove Ahui. Our free online virus scanner may also be used as an additional tool to manually check any file on your computer that you’re worried about.



Leave a Reply