We are proud to present our removal instructions for the Altruistics Software trojan app that appears in Windows.
The Altruistics app creates a process in the task manager called altruistics.exe and poses as an official app you can look up in the control panel. Altruistics uses all of a PC’s idle GPU and CPU power to mine cryptocurrency supposedly as a form of charity (because you are an altruist – get it?). That is of course a complete scam, since literally no one installs the app by choice.
Altruistics is unique and has very specific operation, which we observed and took great care to research. We already know from user feedback that the instructions below work. But if something changes and they are no longer relevant, please contact us or use the malware removal tool we recommend.
Altruistics Software Removal Guide
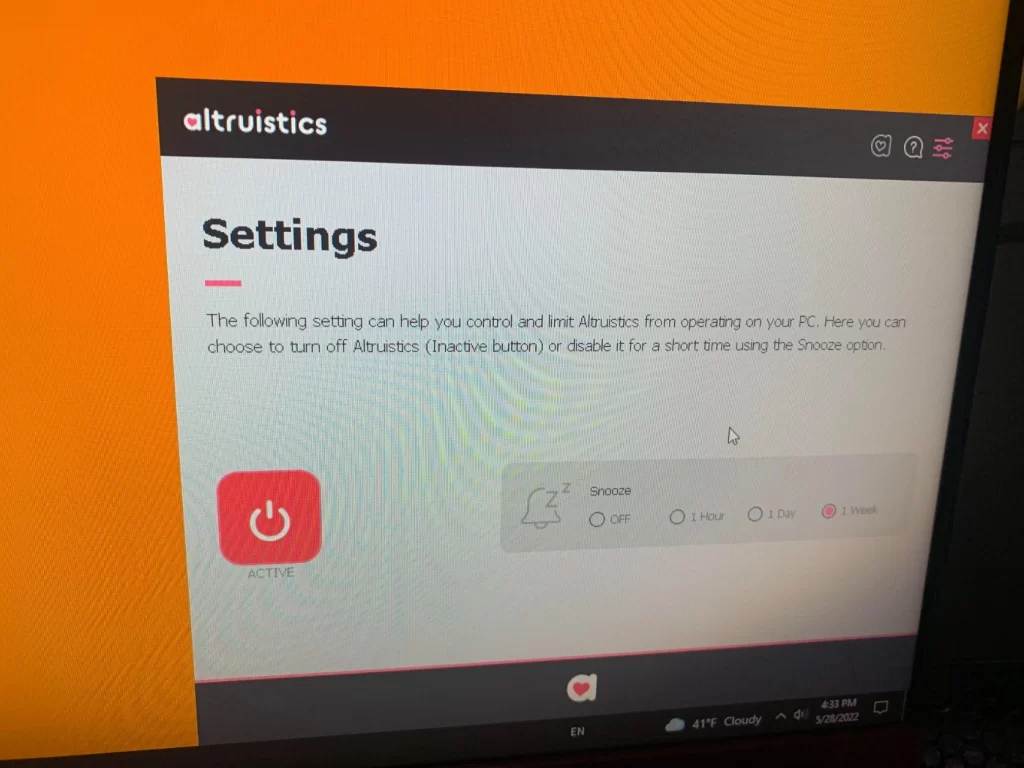
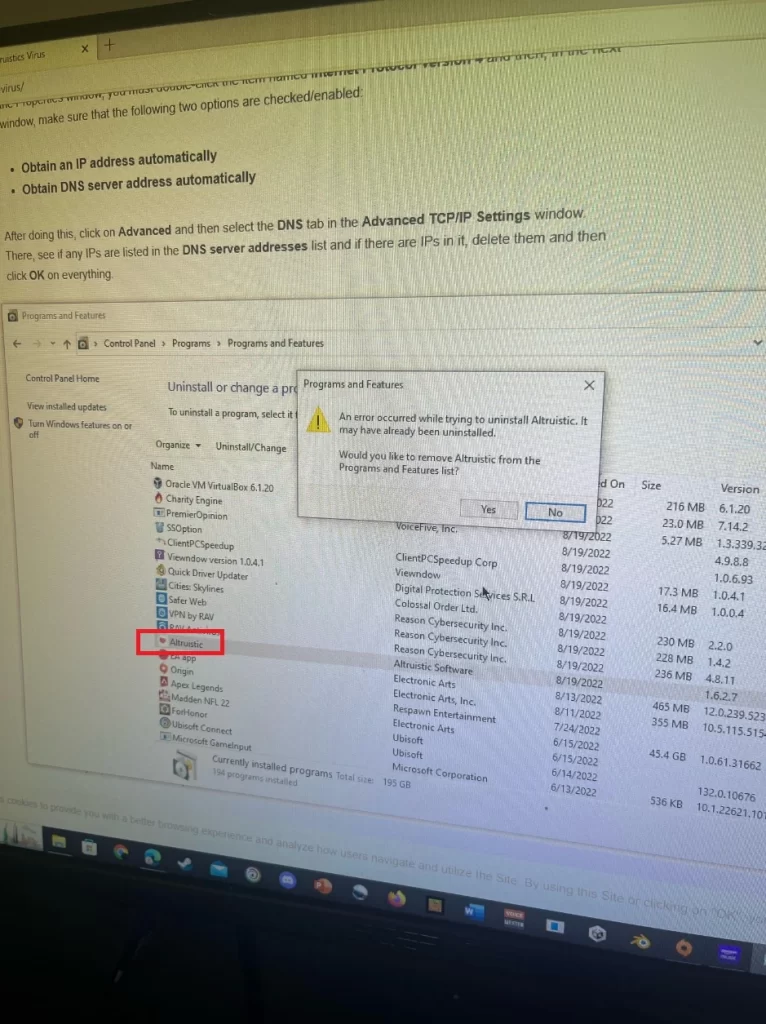
The real problems start when you identify Altruistics and try to uninstall it. The app has an official entry but the uninstall function doesn’t do anything, and the “turn off” setting in the app itself is the same. Trying to delete Altruistics’s folder only nets you an error or warning. Ending the task in task manager stops it for a second, then it resumes.
We will need to be thorough in the removal. Make sure you don’t skip anything. It’s important.
SUMMARY:
| Name | Altruistics |
| Type | Trojan |
| Detection Tool |
First, we want you to create a custom restore point for Windows. Just to be clear, nothing should go wrong. This is a safety precaution.
Hit the Windows button then type Restore. “Create a restore point” should come up right away.

In the new system properties dialog choose “Create”, name the restore point, and click Create.

How to remove Altruistics from your PC
This is where the real guide begins. Read all the steps before going through them. Begin after that. This will save you headaches. If you don’t feel up to the task, download the AV program we recommend. These steps are the only way we found to uninstall Altruistics without an AV program.
- Open the Start Men, type Folder Options, open it, and go to View. Check “Show Hidden Files, Folders, and Drives” and click OK.
- Now, open the Task Manager by pressing CTRL + SHIFT + ESC. Altruistics should be there either as Altruistics.exe or another similar name that operates wih a high CPU percentage. It may attempt to hide itself by stopping the task as soon as you open the Task Manager, but it should be easy to spot. We’ve seen similar names like Atruic, Altruic etc. pop up instead, but at any rate, you need to find which one is doing it.
- Right click on it and click the “Open File Location” option. If it’s the same as what we found, the location it sends you to should be “C:\Program Files (x86)\Altruistics”. If you encounter an error while trying to access it, just go through Windows and check this location first. Once you are there, delete the entire folder if you can.
- In case you are denied deleting the folder or its items, or you can’t even open it, go to this page and install the Lock Hunter tool. It’s free.
- This will allow you to destroy such undeletable items. Right-click the Altruistics folder, select What’s locking this folder?
- Click the Delete option in the new window. The tool will automatically unlock the folder and delete it for you.
- Now, it’s time to prevent the thing from coming back. Type Task Scheduler in the Start Menu, open it, select the Task Scheduler Library from the top-left, and look at the listed tasks.
- If anything seems odd and possibly linked to Altruistics, delete the task. You can look at what each function does by right-clicking it → Properties → Actions. Look where it starts from in the Details field. Aything that starts from a place like AppData or Roaming, or Downloads is not not be trusted. Delete it.
We unfortunately can’t give you an exact name to look for in the Task Scheduler, but there should be something. You could see a “Altruistics” task, but it could also have a different name – Atruic, altsrt, etc, a bunch of options starting with the letter “A”.
Spend some time looking through the entries to be sure. Delete anything you think is related and don’t be afraid – you made a system restore point, remember? You can just roll back. The scheduler is there to start new tasks in intervals.
After you are done, you can now safely go in the Control Panel, find Altruistics, and uninstall it – Windows should detect there’s something wrong with the uninstaller and remove it from the panel together with any leftovers.
How to check if Altruistics is removed completely
At this point, you should feel good enough to stop. BUT! There is the possibility Altruistics has downloaded and installed something else on your PC. We recommend restarting your PC, then opening the Task Manager again.
Look for other processes you may have missed. A good way to gauge this is in the Details Tab.

Arrange the processes by User Name.
The reason you want to do this is so that anything with your user name is displayed, together with its description on the right. This makes it relatively easy to spot fishy processes. If you find any, right click them and delete them like you did earlier in the guide.
What is Altruistic software?
Altruistic software is a deceptive term used to describe a harmful Trojan virus, known as the Altruistics virus. Despite its seemingly benevolent name, the Altruistic software is anything but. It’s a malicious program that infiltrates your computer, usually by hitching a ride with other software you might download from less-than-reputable sources. Once installed, it performs unsolicited operations like cryptojacking, which can severely slow down your system and potentially lead to privacy violations and financial losses.
Is Altruistic a virus?
Yes, Altruistic is a type of Trojan virus, and it’s one that can cause significant damage. Once installed on a computer, it can covertly perform tasks like cryptojacking, mining cryptocurrency for cybercriminals without the user’s knowledge. The Altruistic virus is typically bundled with seemingly harmless applications or software, deceiving users into unintentionally installing it.
How to remove Altruistic software?
Removing Altruistic software requires a reputable anti-virus program. Here are the general steps you should follow:
1. Update your anti-virus software to ensure it can detect and remove the latest threats.
2. Run a complete system scan to identify any infected files or programs.
3. Follow the anti-virus software’s recommendations to quarantine or remove any detected threats.
4. If the Altruistic software has been detected and removed, restart your computer to complete the process.
Remember, the best defense against such threats is to avoid downloading applications from dubious sources and to keep your anti-virus software updated.

#Bloqueo publicidad Spotify
0.0.0.0 adclick.g.doublecklick.net
0.0.0.0 googleads.g.doubleclick.net
0.0.0.0 http://www.googleadservices.com
0.0.0.0 pubads.g.doubleclick.net
0.0.0.0 securepubads.g.doubleclick.net
0.0.0.0 pagead2.googlesyndication.com
0.0.0.0 spclient.wg.spotify.com
0.0.0.0 audio2.spotify.com
#
Hi Edy,
you can safely delete these entries.
hi i cant delete altruistic folder from register can i know how to remove it some other way please?
Hi Jessica,
did you try SpyHunter, the antivirus software provided on this page?
im poor and i need to uninstall it how can i do
Hi adam,
I firmly suggest you to go through the Removal guide on this page. It will help you get rid of the virus.
Heeey, i dont know if you gonna read this, but this “Altruistics” program at least for me is not an add problem, is something that is using my CPU to the amount when sometimes it gets to the 100% of usage and i tried it all, just like in the article said… this malware could download more malware’s right?
Help me Please
Hi Jose Deacon,
if you went through the whole guide, then I suggest you download SpyHunter, the antivirus software provided on this page.
Hey George,
This Altruistics made all of my CPU go red 100%.
I just noticed my pc going slow, and looked at my task processes to locate the ‘altruistics’ program. Removing the program this the job, but your list of steps was very interesting for any later problem.
thx a lot.
From Belgium
I found Restminder at Registry editor, Should I remove it?
Hi kal,
toy can follow this link to remove Restminder.
you must press together Ctrl + F to evoke its search bar and then use the latter to search for Altruistics items and to delete them. When i delete them ” cannot delete altruisticsService : errror while delete key ” what i have to do :< can you help me
Hi Hiro,
did you manage to delete every other aspect of the program?
I need help im stuck on Registry Editor i cant delete anything
Hi Kapene Munro,
do you have Admin. rights?
i has some questions why does altruistic is in my pc and i rescreach it and i find it its a virus and it makes my pc slow and i cant end task the program, there are 2 altruistics in my pc and i dont know how to remove them.
Hi andy hillariker,
did you go through our removal guide? If you follow the steps, you will be able to remove the virus
help me the virus is not gone !!
Hi hieu,
did you go through the whole removal guide?
HELP I CANT GO TO SAFE MODE
Hi Chicken,
can you describe to us more about what is preventing you from doing that?
my laptop has that virus and veiwdow
but they are not working lmao
Hi someone is sus,
i still suggest you to go through the removal guide and get rid of these permanently.
It is very easy, if u need I can help you. I have removed it today only without any use of any antivirus app or antimalware app. If you need help, I’ll be grateful.
Thank You