Bboo
Bboo is a representative of what is officially considered to be the most dangerous computer virus category of ransomware. Specifically, Bboo is file-encrypting ransomware. And what this means is that after it infects its victims, it encrypts the files in their systems using a complex double key. As a result, the victim users are left with a bunch of useless data that cannot be opened or accessed by any existing type of software.
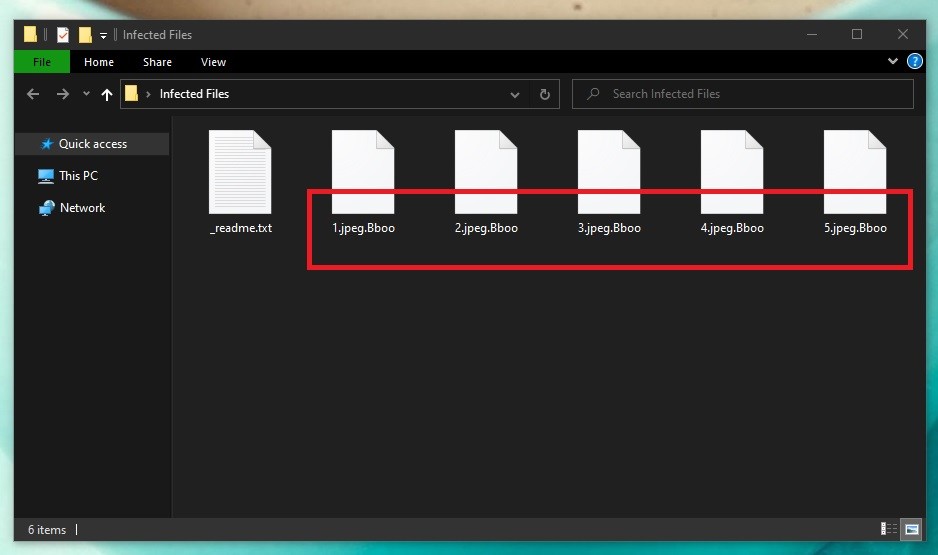
The Bboo Virus will encrypt your files
On top of that, once the encryption process comes to an end, the victims are informed about it via a note that is left on the desktop of the computer. Usually, it includes a ransom demand (hence, the name of this type of software), which users are required to pay in exchange for a special decryption key necessary to unlock the encrypted files. And as practice has shown, the hackers behind viruses like Bboo have an underlined preference for cryptocurrencies, most commonly Bitcoin. So there will typically also be a wallet number included to which you will have to make the transfer. And to make sure they drive their point across, the cybercriminals are also in the habit of including threats and scare tactics so that users are pressured into actually making the payment.
But don’t let those threats put pressure on you. Infections like this are very serious and require a serious approach towards them. Rushing to comply with the ransom demands will not necessarily solve your problem and may only end with you spending your money for nothing. We would recommend leaving this option as your last resort only after you’ve exhausted all other alternatives. But before you even attempt to recover your encrypted data, it is vital that you first tend to the removal of Bboo from your computer. If you do not do this, then even if you manage to restore some of your files, they will likely end up getting encrypted by the virus once again.
Below we have included a detailed removal guide that will walk you through the process of locating and deleting this ransomware virus from your machine. And after you have taken care of that, you will see that in the second part of the guide there are instructions on how you may be able to recover your data from system backups.
The Bboo virus
The Bboo virus is notorious for the extent of damage that it may inflict. An infection with the Bboo virus may potentially cost users permanent loss of important data. Unfortunately, this is a scenario that you will have to accept if your computer has already been infected with this malware. However, we do hope that the below instructions will help you recover your files and you won’t have to deal with the consequences of losing them to ransomware.
Especially if you already have copies of your data stored on a separate hard drive or if they’ve been uploaded to a cloud service, then you shouldn’t have much to worry about. Alternatively, as mentioned, we can help you recover copies from system backups. But there are also decryptor tools that are normally available for free online for certain ransomware variants, and that may be a feasible option for you if nothing else works.
This is one of the reasons why ransomware like Bboo is considered to be so terribly devastating. And another is the fact that it’s incredibly stealthy when at work. In fact, one of its main advantages in the face of other types of computer viruses is that it will not trigger the vast majority of security software out there.
The thing is that because ransomware uses encryption as a means of inflicting damage, it doesn’t show up on the radar of most antivirus programs. Encryption is in itself a very benign process and not something that is traditionally considered malicious. Therefore, ransomware can be left to undertake its harmful and often time-consuming activities whilst left completely undisturbed and right under the nose of its unsuspecting victims.
The Bboo file distribution
The Bboo file distribution tactics play an important role in preventing such infections in the future. Once you know how the Bboo file is distributed, you will be able to avoid ransomware attacks from now on.
Now, you may not have realized exactly at which point in time you may have landed this particular ransomware variant on your computer. And we cannot tell you for sure how this has come to pass either. But we can outline the main distribution channels of ransomware in general, and perhaps one of them might ring a bell for you. Either way, it’s important to know all the means of malware distribution so you can protect yourself accordingly.
One of the most common ways of getting infected with this and other virus types is through spam messages. Be it via email or social media, you’ve no doubt received messages from unfamiliar senders prompting you to follow a link or download an attached file under whatever pretense. By clicking on the respective link or attachment, if it was sent with malicious intents, you are likely to first download a Trojan horse virus, which acts as backdoor for the ransomware. Hence, it then automatically downloads the ransomware and all of this happens without you even realizing it.
Another possible way of landing ransomware like Bboo is through illegally obtained content. Say, you downloaded a cracked version of some piece of software from a torrent or similar website. It may have easily been embedded with ransomware or a Trojan that was programmed to infect you with malware (as stated above). Similarly, hackers also often hide viruses in online ads which are known as malvertisements. Therefore, we highly recommend not clicking about on random ads that come your way while you’re browsing the web.
Also, after you’ve removed Bboo from your system, it would be highly beneficial that you also run a full system scan in case it came with a Trojan horse virus. We have a designated removal tool that can help you take care of that problem, if it turns out that you have a need for it.
SUMMARY:
| Name | Bboo |
| Type | Ransomware |
| Detection Tool |
Remove Bboo Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Hello friend, all right? i wonder if there is already some anti virus and also something I can stop the ransoware of the (bboo) extension? I was infected with this damn ransoware and lost all my fotas, from my children and also some videos! i have all the files saved in a hd, help me to decrypt please. my name is Flavio and I live in Brazil. God bless you. Hug
Hello Flávio Souza, unfortunately your files cannot yet be decrypted, I would advise you to keep your files and wait for a decryption tool to be released in the future.