This page aims to help you remove .Besub Ransomware Virus for free. Our instructions also cover how any .Besub file can be recovered.
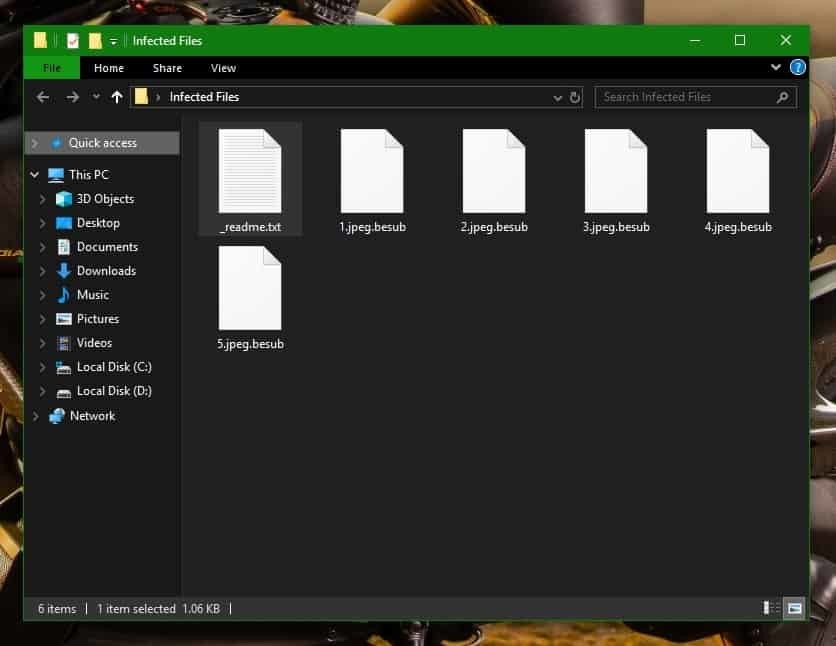
The .Besub Virus belongs to the DJVU (STOP Ransomware) family. It encrypts your files and modifies their extension to .besub.
When .Besub Ransomware is done encrypting your files, it leaves a _readme.txt file with instructions for you to follow:
ATTENTION!
Don't worry my friend, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-arDe4ZLdAE
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.
To get this software you need write on our e-mail:
[email protected]
Reserve e-mail address to contact us:
[email protected]
Our Telegram account:
@datarestore
The paragraphs down below will provide the visitors of this page with some essential details about a recently developed cyber threat that is called the .Besub Virus. The malicious virus which is going to be the focus of our article is categorized as a Ransomware. Something special about Ransomware programs such as this one is that they utilize a procedure called encryption with the help of which they deny the targeted victims access to their own personal data. Once all of those personal files have been duly encrypted by .Besub, the victim receives a message which asks for a ransom payment to be made in exchange for a decryption key. Generally, the dreaded message provides instructions by the hackers who are in control of the infection regarding the way the required ransom should be paid. Additionally, the notification may contain threatening text, claiming that all the encrypted data will be lost for good in the event that the requested ransom money doesn’t get transacted on time. In case you’ve had the bad luck of getting your computer infected by .Besub Virus, .Litar, .Docm you really should get as much information as you can in relation to this cryptovirus and the methods that you can use to deal with it. The good news is that the upcoming paragraphs can help you with that so we suggest you stick with us till the end where you can find a detailed Removal Guide and a professional removal tool for automatic assistance.
Ransomware operates in a special way!
Readers of this article must bear in mind that Ransomware is a rather unique type of computer threat. Maybe that’s exactly why this sort of malware is to be blamed for so many difficult-to-handle issues. Unlike most of the online dangers, which may be detected by using good antivirus programs, Ransomware normally succeeds in staying under the radar of the antivirus program that the users might have. The reason for that is in the unique way this sort of virus fulfills its purpose. Instead of attacking and trying to cause damage to your PC or its files, .Besub wouldn’t normally do any of this. This way, the malware won’t trigger the virus definitions of the antivirus software and would be able to remain hidden while silently encrypting your data. The encryption that the virus utilizes isn’t harmful by itself and doesn’t harm the data that it has targeted. It just makes it inaccessible without the application of a special decryption key. As a result, you will have access neither to the files nor to the decryption key and will be ruthlessly blackmailed into paying a certain amount of money in exchange for regaining your access.
Unfortunately, there are almost no visible symptoms, which could indicate the presence of such malware before it has carried out its nasty job which is the main reason why the majority of the victims come to know about the attack only when it is too late.
Paying the ransom to the criminals, however, is not a good solution to this type of malware. For one, this is just a direct sponsorship of their criminal scheme and for second, there is absolutely no guarantee that you will save your flies by fulfilling their ransom demands. That’s why we suggest you give a try to some alternatives which may help you to remove .Besub and recover some of your data from backups or other methods and only consider the ransom payment as a last resort.
SUMMARY:
| Name | .Besub |
| Type | Ransomware |
| Detection Tool |
Remove .Besub Ransomware Virus
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

I got infected with the BESUB virus lately is there a way to restore my files from the encryption??
Did you try any of the steps from the guide? Also, if you are seeking recovery solutions, you can find some suggestions in our How to Decrypt Ransomware article on this site.
127.0.0.1 space1.adminpressure.space
127.0.0.1 trackpressure.website
127.0.0.1 htagzdownload.pw
127.0.0.1 360devtraking.website
127.0.0.1 room1.360dev.info
127.0.0.1 djapp.info
127.0.0.1 sharefolder.online
127.0.0.1 telechargini.com
127.0.0.1 fffffk.xyz
127.0.0.1 smarttrackk.xyz
You should definitely delete those IP addresses from your hosts file – they are not supposed to be there and are likely related to the virus.
Hi, please help us to restore the infected the besub virus