Bitcoin Blackmail Email in 2020
The Bitcoin Blackmail Email in 2020 is a sextortion email attempt. The targeted user usually receives a threatening email with demands for a bitcoin payment. However, this is usually just a trick.
Many web users have recently posted about a new blackmail scam that is actively spreading around the web via emails. The scam contains of a message, sent from an unknown sender, which pretends to be a hacker. The self-proclaimed hacker typically claims to have compromised the victim’s computer and to have accessed their password and contacts. It also claims that, with the help of a secretly inserted malware, the attacker has captured an embarrassing video and screenshots of the victim, and threatens to send them to all the stolen contacts if a certain amount of money is not being paid.
The embarrassing videos and footage usually are related to pornography and adult dating links and are followed by a ransom demand. The hacker usually requires a payment in bitcoins and promises to delete the embarrassing content if he receives the money within the given deadline. Normally, the person behind the scam tries to blackmail the victim by sending a series of emails, mainly to their work email address.
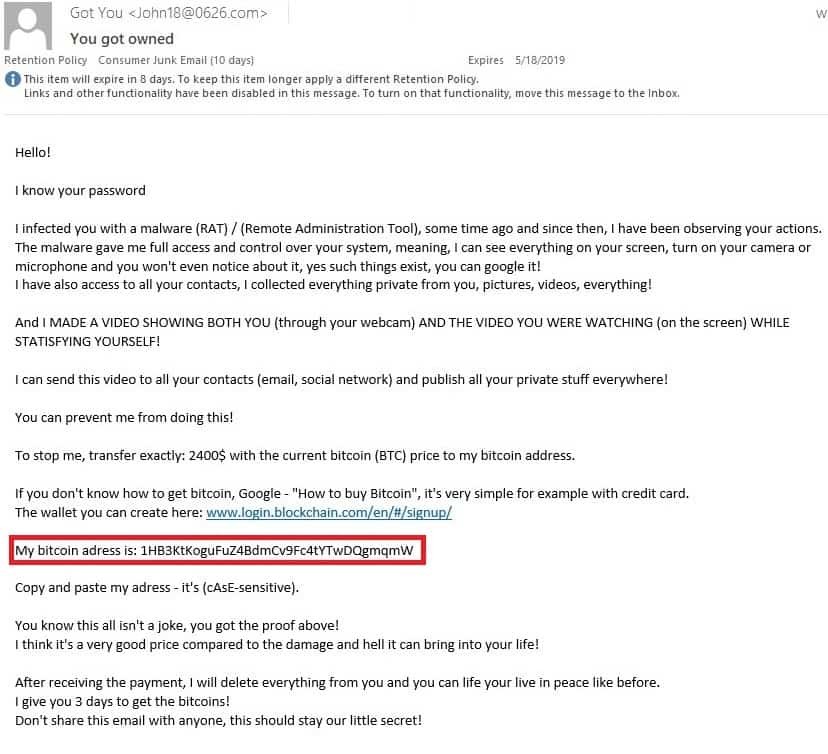
Here is another example of the email scam for bitcoins, which a user has posted online. You may notice that the words may be different in your case, some even maybe in broken English, but they all generally follow the same script.
Hacker Email Bitcoin in 2020
The Hacker Email bitcoin 2020 is an email scam. The main reason behind it is to extort money from the targeted users in the form of Bitcoin payments.
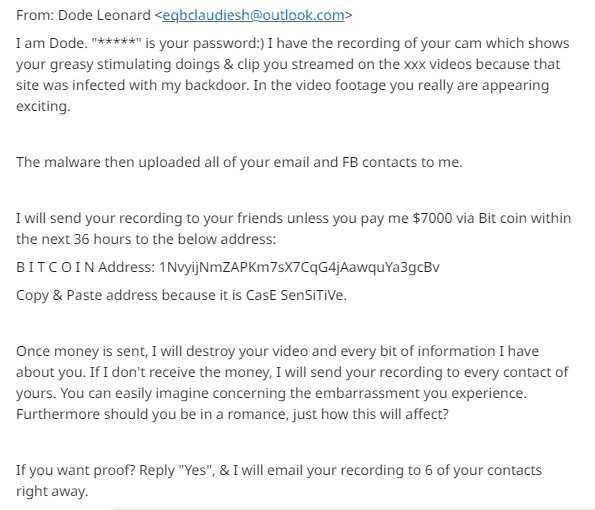
This is what users have recently shared about the blackmail email scam online:
“Well, I actually placed a malware on the porn website and guess what, you visited this web site to have fun (you know what I mean). While you were watching the video, your web browser acted as a RDP (Remote Desktop) and a keylogger which provided me access to your display screen and webcam. Right after that, my software gathered all your contacts from your Messenger, Facebook account, and email account.”
Threatening email asking for bitcoin in 2020
The Threatening email asking for bitcoin in 2020 is what is known as an email bitcoin scam. The people behind Bitcoin Blackmail Email would try to con you into paying a Bitcoin ransom to stop them from releasing embarrassing videos and information of you.
Recently more recent complaints have been forwarded towards us containing this message:
” What exactly did I do?
I made a split-screen video. First part recorded the video you were viewing (you’ve got a fine taste haha), and next part recorded your webcam (Yep! It’s you doing nasty things!).
What should you do?
Well, I believe, $1900 is a fair price for our little secret. You’ll make the payment via Bitcoin to the below address (if you don’t know this, search “how to buy bitcoin” in Google). “
According to security researchers, such a scam has been widely reported in Australia and has recently appeared in the United States. Leading analysts consider the email blackmail threat as an empty one since the blackmail message normally fails to include personal information about the victim or other details that can prove what the hacker claims. However, there have been reported cases where the hackers have addressed the victim’s real name and have sent them their old password, their actual phone number, as well as attached videos of them, reading the email, in order to “prove” that they have indeed hacked the machine.
Bitcoin email scam in 2020
The Bitcoin Email Scam in 2020 is an email bitcoin scam. This is also known as a sextortion email scam – users are being pressured into paying to stop the release of compromising personal information. In most cases, this is not true but just a hoax.
Below is a sample message sent by scammers trying to trick users into sending them Bitcoin currency.
i am a hacker who has access to your operating system. i also have full access to your account.
In case that you have received a disturbing email message from an unknown sender with a similar script and you are concerned, you should know that, so far, this is a scam campaign that has been sent to thousands of email addresses and is most probably a lie. As long as you don’t have any malware on your computer and your system and accounts have not been compromised, there is absolutely no reason to get panicked over such a blackmail threatening message. You should better report it as spam and post the text of the scam message (without your personal data) online so that Google can show it up to others, which may have been targeted with the same message. Also, for your safety, it is a good idea to avoid interaction with any spam messages, shady emails, and sketchy web locations and provide your PC with reliable security software against system breaches.
SUMMARY:
| Name | Bitcoin Blackmail |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Your browser may start to redirect you to different ads, pop-ups, and sponsored pages. |
| Distribution Method | Typically distributed via software bundles, free installation packs, download links, spam, ads, torrents, freeware sites. |
| Detection Tool |
Remove Bitcoin Blackmail Email in 2020
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them. If you see a screen like this when you click Uninstall, choose NO:


Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.
- Remember this step – if you have reason to believe a bigger threat (like ransomware) is on your PC, check everything here.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.

Type Regedit in the windows search field and press Enter.
Once inside, press CTRL and F together and type the virus’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Hi there ! I got a very similar scam to my Hotmail address this morning (though MAC correctly put it in Junk folder). Here is the text and email address. Please do not allow Yourself even one moment of hesitating – just report a scam and a scammer. The more we get those dickheads to the light – the more safe internet environment we will have. So, below is text of that message from some “Glen Perez”:
Hi!
I know that: xxxxxx – is your password! (It was one of my old ones used few years ago)
I infected you with my private malware, RAT, (Remote Administration Tool) some time ago.
The malware gave me full access and control over your computer, meaning, I got access to all your accounts (see password above) and I can see everything on your screen, even turn on your camera or microphone and you won’t even notice about it.
I made a video showing both you (through your webcam) and the video you were watching (on the screen) while statisfying yourself!
I can send this video to all your contacts (email, social network)!
I can publish absolutly everything I found on your computer!
You can prevent me from doing this!
To stop me, transfer exactly 1000$ with the current bitcoin (BTC) price to my bitcoin address.
If you don’t know how to get bitcoin, Google – “How to buy Bitcoin”.
The wallet you can create here: www .login .blockchain com/en/#/signup/
My bitcoin adress is: 13i31QoZKzo4DkB7ewHvFuHN5hDnztfRUe
Copy and paste my adress, it’s (cAsE-sensetive)
After receiving the payment, I will delete the video, and we will forget everything.
I give you 4 days to get the bitcoins.
Since I already have access to your computer, I know when you read this email.
Don’t share this email with anyone, this should stay our little secret!
MsgID: 9984232036
Wow. A year later and I received an e-mail with a nearly identical message! At first, I considered responding with, “Aww go ahead. They have known worse about me.” But, I realize it’s best to simply not engage with them. I think what frightens people the most is how these e-mails start off with a password that people have actually used. Then, a person is consumed by fear, trying to figure out how often they actually used the password. I stopped using the password I was threatened with, but it’s difficult to remember every site I might’ve visited, where I used the password. Is there a program that can find all the sites a person has registered for? Or is there a way to find all of the times a person used a certain e-mail to register for certain apps?
Hi Johnny R,
i don’t know about such site, but if you are using Chrome you can go to options (Customize and control Google Chrome), then click on Settings and there will be an option that says Passwords. When you click it, it will open you a list of sites you have visited. This are all the sites Chrome has saved your usernames and passwords. For Firefox is the same when you open settings in the menu there will be an option called Logins and Passwords. I assume the method is the same with other Browsers.
I got that same exact email, word for word two days ago. My email was sent by some idiot named Bobbie Thomas (alias) of course. The password this parasite used was an old one from my hotmail address as well. I recall hotmail being compromised several years ago and that’s where these perps got it from. These parasites need to be squashed!
Can anyone confirm whether or not the threats were carried out? I’m not paying the scum either way, but I’d at least like to warn my contacts in case they get a little more of me than they bargained for.
In most of the cases, it’s nothing but a scam without an actual malware behind it. Still, if anyone has had a different experience and the threats have actually been fulfilled, it may indeed be a good idea to at least share it in the comments so that the other users are informed.
I just received a similar mail. The password they specified is an old password used years ago on a hotmail account. This worries me because although it is an old password, it was accurate. Can anyone please share if you have been contacted again or what happened?
=======
I do know, xxxxx, is your pass word.
I require your total attention for the coming Twenty-four hours, or I will make sure you that you live out of embarrassment for the rest of your life.
Hi, you do not know me personally. Yet I know every thing about you. Your present facebook contact list, phone contacts along with all the digital activity on your computer from past 164 days.
And this includes, your masturbation video clips, which brings me to the main reason why I ‘m writing this specific email to you.
Well the previous time you visited the adult material web sites, my malware ended up being triggered in your personal computer which ended up saving a eye-catching video clip of your self pleasure act by triggering your web camera.
(you got a unquestionably odd preference btw lmao)
I have the whole recording. In the case you feel I ‘m playing around, simply reply proof and I will be forwarding the particular recording randomly to 6 people you recognize.
It may end up being your friends, co workers, boss, mother and father (I’m not sure! My software will randomly choose the contacts).
Will you be able to look into anyone’s eyes again after it? I question it…
Nonetheless, it doesn’t need to be that path.
I want to make you a 1 time, non negotiable offer.
Purchase USD 2000 in bitcoin and send it on the below address:
bc1***qshrp2as6enze6pdlp96aye90eh6s4jfzrrjqt0
[CASE sensitive copy & paste it, and remove *** from it]
(If you don’t know how, lookup how to purchase bitcoin. Do not waste my valuable time)
If you send out this ‘donation’ (why don’t we call it that?). Right after that, I will disappear for good . and never ever make contact with you again. I will erase everything I’ve got in relation to you. You may very well keep on living your current normal day to day lifestyle with zero concern.
You’ve 1 day to do so. Your time starts as quickly you read this mail. I have an special code that will tell me once you go through this e mail so don’t try to act smart.
Hi Krish,
I too got a similar email today (16 April 2020), from a “Elita Yellin” ([email protected])
The email was nearly word for word as what you’ve posted, but with very minor alterations. What got to me and and made me nervous was that the person knew my account’s password (although it was an old one), till I read Mike’s post above, saying that Hotmail was compromised a few years ago.
It’s a bit of a relief to find out that I’m not the only one to receive such emails. Needless to say, I’ll just be ignoring them.
I also got the similar mail today (April 17). Can you please explain us the solution to this.
Hi Nipuna, there is nothing much really to explain about emails such as the one you have received. They are sent out only to confuse or scare you into sending money to the people who wrote them. If the constant spam is not stopping it is possible that you may have been infected with malware. You can try to download SpyHunter or use our removal guide.
I received a similar email 2 days ago from Yancy Hyland [email protected] which I forwarded to [email protected]. I now forward all such scam and phishing emails to the email provider. If we all did the same there might be fewer of these scumbags eventually. I live in hope.
I got a slightly different e-mail. Only my email adress was true. Here it is:
I am a hacker who has access to your operating system.
I also have full access to your account: At the time of hacking your
account xxxxxxxxxx had this password:
h93heu14gigjbqddb.n8ffek3ttdfx.
You can say: this is my, but old password!
Or: I can change my password at any time!
Of course! You will be right,
but the fact is that when you change the password, my malicious code every
time saved a new one!
I’ve been watching you for a few months now.
But the fact is that you were infected with malware through an adult site
that you visited.
If you are not familiar with this, I will explain.
Trojan Virus gives me full access and control over a computer or other
device.
This means that I can see everything on your screen, turn on the camera and
microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence from
e-mail and messangers.
Why your antivirus did not detect my malware?
Answer: My malware uses the driver, I update its signatures every 4 hours
so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the
screen, and in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and
contacts on social networks. I can also post access to all your e-mail
correspondence and messengers that you use.
If you want to prevent this, transfer the amount of $733 to my bitcoin
address (if you do not know how to do this, write to Google: “Buy
Bitcoin”).
My bitcoin address (BTC Wallet) is: 16m1NLzSaxvgnnM4xZ2Eav1wyE6DbzGdgX
After receiving the payment, I will delete the video and you will never
hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see
this letter.
Do not try to answer me (the sender’s address is automatically
generated)!
Filing a complaint somewhere does not make sense because this email cannot
be tracked like my bitcoin address.
I do not make any mistakes.
If I find that you have shared this message with someone else, the video
will be immediately distributed.
Bye!
The scam messages may very, the important thing is not to fall for the scammers’ bait. Use our guide and the removal tool linked there if you still fear there may be some form of malware in your computer but do not pay the blackmailer.
Here’s the e-mail I got from William Wells. At least got me thinking about covering up my webcam.
Hi!
I am a hacker who has access to your computer.
I also have full access to your acc: At the time of hacking your
profile(MY E-MAIL ADDRESS) had this pass: OLD PASSWORD
You can say: this is my, but old password!
Or: I can change my pass at any time!
Of course! You will be right,
but the fact is that when you change the password, my virus every time
saved a new one!
I’ve been watching you for a few months now.
But the fact is that you were infected with virus through an adult web-page that you
visited.
If you are not familiar with this, I will explain.
Soft gives me full access and control over a computer or other device.
This means that I can see everything on your screen, turn on the camera and
microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence from e-mail and
messangers.
Why your antivirus did not detect my malware?
Answer: My malware uses the driver, I update its signatures every 4 hours so that
your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and
in the right half you see the video that you watched.
With one click of the mouse, I can send this video to all your emails and contacts
on social networks. I can also post access to all your e-mail correspondence and
messengers that you use.
If you want to prevent this, transfer the amount of $642 to my bitcoin address (if
you do not know how to do this, write to Google: “Buy Bitcoin”).
My bitcoin address (BTC Wallet) is: 1FsQ6ofgshD6bR5V1X5LG1iF5Am5zNgrTL
After receiving the payment, I will delete the video and you will never hear me again.
I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be
tracked like my bitcoin address.
And please do not try to answer me (the sender’s address is automatically generated).
I do not make any mistakes!
If I find that you have shared this message with someone else, the video will be
immediately distributed.
Bye!
CONFIDENTIALITY CAUTION: This message is intended only for the use of the individual or entity to whom it is addressed and contains information that is privileged and confidential. If you, the reader of this message, are not the intended recipient, you should not disseminate, distribute or copy this communication. If you have received this communication in error, please notify us immediately by return email and delete the original message. Thank you.
Yet another example of this type of scams – it may be a good idea to check your computer for hidden hazards but you should certainly not do anything that the hacker tells you to.
Hello!
My nickname in darknet is haley62.
I hacked this mailbox more than six months ago,
through it I infected your operating system with a virus (trojan) created by me and have been monitoring you for a long time.
Please check “from_address” for this email. You will see what I wrote this letter to you from yours account.
Even if you changed the password after that – it does not matter, my virus intercepted all the caching data on your computer
and automatically saved access for me.
I have access to all your accounts, social networks, email, browsing history.
Accordingly, I have the data of all your contacts, files from your computer, photos and videos.
I was most struck by the intimate content sites that you occasionally visit.
You have a very wild imagination, I tell you!
During your pastime and entertainment there, I took screenshot through the camera of your device, synchronizing with what you are watching.
Oh my god! You are so funny and excited!
I think that you do not want all your contacts to get these files, right?
If you are of the same opinion, then I think that $710 is quite a fair price to destroy the dirt I created.
Send the above amount on my BTC wallet (bitcoin): 1EWC67MSLiYRt2nNU5UWVMSxGG4b9RocUc
As soon as the above amount is received, I guarantee that the data will be deleted, I do not need it.
Otherwise, these files and history of visiting sites will get all your contacts from your device.
Also, I’ll send to everyone your contact access to your email and access logs, I have carefully saved it!
Since reading this letter you have 48 hours!
After your reading this message, I’ll receive an automatic notification that you have seen the letter.
I hope I taught you a good lesson.
Do not be so nonchalant, please visit only to proven resources, and don’t enter your passwords anywhere!
Good luck!
Can someone help me understand how does he make “sender” really like me?
I checked the sender email, it’s not some random identity, it is really me.
However, I can’t find this email in my sent folder. So this is a fabricated email. But how does he do it?
Don’t pay! You can report the scam bitcoin address to https:// bitcoinwhoswho .com so that other victims will know that it’s a scam before sending any btc. Your report will also let exchanges and other users know, so that the scammer won’t be able to withdraw any btc.
Today I received:
“I’m aware, xxxxxxxxxx, is your pass word.
I need your 100% attention for the up coming Twenty-four hrs, or I will make sure you that you live out of shame for the rest of your lifetime.
Hello there, you do not know me. But I know pretty much everything about you. Your entire fb contact list, mobile phone contacts and all the digital activity on your computer from past 181 days.
Which includes, your masturbation video footage, which brings me to the primary reason why I am composing this e mail to you.
Well the last time you visited the sexually graphic websites, my malware ended up being triggered inside your pc which ended up logging a beautiful video clip of your masturbation play simply by activating your web camera.
(you got a tremendously odd preference by the way haha)
I own the full recording. If, perhaps you think I am fooling around, just reply proof and I will be forwarding the recording randomly to 11 people you know.
It could end up being your friend, co workers, boss, parents (I’m not sure! My software program will randomly pick the contact details).
Will you be capable to look into anyone’s eyes again after it? I doubt that…
Nonetheless, doesn’t necessarily need to be that way.
I would like to make you a 1 time, non negotiable offer.
Get $ 2000 in bitcoin and send it on the below address:
bc1***qqgv78fcnmj8gdglermsss0y2fg997cuv0gfa6x
[CASE SENSITIVE, copy and paste it, and remove *** from it]
(If you don’t know how, lookup how to acquire bitcoin. Do not waste my important time)
If you send this particular ‘donation’ (let’s call it that?). After that, I will vanish and never ever make contact with you again. I will remove everything I’ve got about you. You may carry on living your current regular day to day life with no concerns.
You have got 1 day to do so. Your time will begin as soon you check out this email. I have an special program code that will notify me as soon as you go through this e-mail therefore don’t try to play smart.”
I have Webroot on my computer already and have run a scan and all appears to be fine. Would you recommend doing anything else?
Hi Steve,
did you go through the guide in this page ?
A few hours ago I got the exact same email! The bitcoin account was different…
??? $ ???? ?? ??????? ??? ???? ?? ?? ??? ?????? ????? ???????:
1*6wPZBULNmZf2kd1Bm5QEH8cs6E5fjnBpe
Hi got the below email a few minutes ago.. Using one of my very old FB passwords
Transfer $1000 in btc to the listed below address (remove***from it):
bc1***qe2m3m388gxu0ycf9cgzaw2xa2val0q9ys24d5k
You could be thinking why the hell would you do that? Very well, prepare yourself simply because I am going to move your world now. I had a hazardous viruses infect your own computer system and also record video clip of YOU (using your web cam) while you looked at ‘adult’ websites.
Here is one of your code kau*****
Still don’t believe me? Respond 7 and I will be randomly share your video clip with 7 people you’re friends with (Yes, I’ve access to your address book as well).
Currently, exactly what do I want to make this entire thing vanish? Well, I have already pointed out the deal in beginning of the e-mail. If you dont fulfill it within 24 hours, I’ll create your life nightmare by delivering that video clip to Everyone you know. Your time frame starts right now.
Hi Amip,
did you try to follow the guide here, in this post?
I got the exact same email today a few minutes ago, with some minor changes. It had an old password of mine. I just deleted the email.
I received the same e-mail. These guys are really a pain i the neck.
25/04/202 Australia. Did get the almost same email. It was revealing an old password and threatened to send video to all contacts if $2000 not paid in a bitcoin wallet.
Excellent way of telling, and fastidious piece
of writing to take information about my presentation topic, which i am going
to convey in school.
Hi. I have received 3 emails during the last few days all same as in the other comments but increasing in viciousness. They include an old password. I must admit I am frightened and unsettled. I have not responded to any of the mails but have photographed them as they can’t be forwarded due to being encrypted. I am in South Africa. Where can I report the 3 different email addresses Mail is being sent from.
I Just received this threatening email. How do you block the email when they use your own email address to hide behind, basically making it look like you have sent the email to yourself? It is obviously a scam because not only have I never visited the site they say I was on but the sex act they claimed they have caught on my webcam and videoed is physically impossible for a female. IDIOTS. How do I block someone or report someone spoofing my own email address ? I also wouldn’t know which device they have supposedly put their malware on as I use three different things online, yet the Spyhunter program says you can only use it once before having to pay for it, which is currently not something I have the means to buy. Wouldn’t McAfee catch someone trying to install malware on the system and block it ??