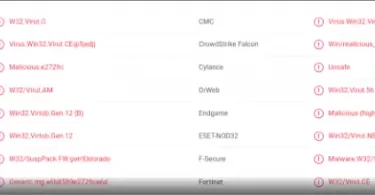
14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg A majority of antivirus programs have detected the virus using 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg Bitcoin Wallet. You can see the attached report from VirusTotal below: 14MRXnsQhQ7LQSfKPMsESdJsEPFDyMCmMg...
Tag - Email
1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK Malware
1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK A majority of antivirus programs have detected the virus using 1PPJpvSPbbMwbESJZXGS8VtKiFQkmm7DvK Bitcoin Wallet. You can see the attached report from VirusTotal below: Multiple antivirus programs detect the trojan...
Publishers Clearing House Scam
*Source of claim SH can remove it. Publishers Clearing House The Publishers Clearing House Scam has been circulating for years, targeting unsuspecting individuals with fake mail claiming they’ve won sweepstakes prizes. However, these scams are...
16691trULjLy1nscmMAJJi5bxULBUWBr9F Bitcoin Email
16691trULjLy1nscmMAJJi5bxULBUWBr9F This page aims to help you remove 16691trULjLy1nscmMAJJi5bxULBUWBr9F Email Bitcoin Virus. Our removal instructions work for every version of Windows. A majority of antivirus programs have...
Mareriedin.com Scam
Mareriedin.com Mareriedin.com is a deceptive website that should be avoided at all costs. Mareriedin...
Osanarelay Scam
*Source of claim SH can remove it. Osanarelay Osanarelay is a Trojan virus that can harm a computer in several different ways. For instance, Osanarelay can steal information from your system and transfer it to servers controlled by hackers or...
Got You Email
Got You Email Got You Email is a Trojan horse that can harm a computer in a number of ways. What is typical for Got You Email is that it can sneak in without being detected and run different malicious processes in the background of the system...
[email protected] Email
[email protected] The [email protected] email is a Trojan horse infection that can hack into any computer without the users’ knowledge. Once inside, [email protected] email can run data-corruption or file-destruction processes, steal sensitive...
Dynamer Trojan
Dynamer Dynamer is a rogue piece of software of the Trojan horse type and it can hijack legitimate system processes to stay disguised. Dynamer is able to gain access to essential system files and settings and manipulate them to complete different...
Win32 Bogent Virus
Bogent Bogent is an extremely harmful piece of malware that belongs to the Trojan horse software category. Users who have Bogent on their system are advised to remove it as soon as they detect it. Trojans like Bogent can be a nightmare for...