Bozon3
Bozon3 is a harmful program, categorized as file-encrypting Ransomware. The goal of Bozon3 is to blackmail you for a money payment by keeping your files locked until you pay a ransom.
If you refuse to issue the payment, the hackers threaten to keep your files inaccessible for good. Obviously, this could bring some pretty serious issue to you if the files in your system are of significant importance.
The Bozon3 virus
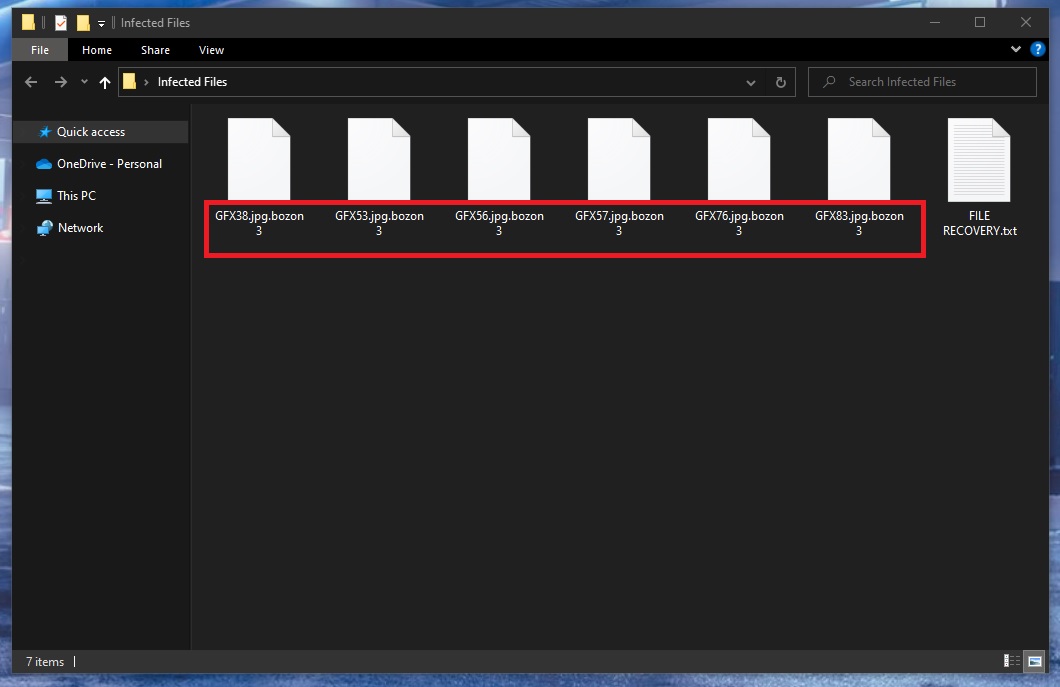
The Bozon3 virus is able to complete its goal by using file-encryption. Even removing the Bozon3 virus will not release the locked files if the user doesn’t have the corresponding decryption key.
As you well know, the Internet is filled with all kinds of shady programs which may attack your PC system and result in all forms of issues if you aren’t careful. Nevertheless, few of the software threats which you could bump into on the internet can match the notorious Ransomware virus category with regards to how nasty and harmful they are. What this type of computer virus is generally used for is blackmailing the attacked user, forcing them to carry out a ransom payment to the online criminal. Bozon3 is the specific virus we will be concentrating on within the next paragraphs. It uses an advanced data-encryption code to make its victims’ files inaccessible and then offers the attacked users to release their files if they pay a certain amount of money as a ransom. If you have already stumbled upon the said Ransomware cryptovirus that is known as Bozon3, you should keep reading this post, since the information within it may perhaps aid you in your battle against the nasty Ransomware virus.
The Bozon3 file encryption
The Bozon3 file encryption can only be bypassed through the use of a special key. The Bozon3 file decryption key is what the hackers use as leverage to blackmail you.
There are several details that make Ransomware computer viruses as hazardous as they are. One of them is that they might without difficulty run undetected by most safety applications. In general, this may mean that viruses like Bozon3, Xcvf, Bbnm are fully able to make one’s data inaccessible without giving out any indication of its actions. What’s more, that kind of Ransomware cryptovirus might be designed with great care and made very sophisticated. For honesty’s sake, we have to inform you that due to the high-level file encryption used by some Ransomware versions, oftentimes there isn’t really a way to restore the files without the key we already mentioned.
The Ransomware’s capability of staying unnoticed by most anti-malware tools doesn’t help either. Note that a typical Ransomware program wouldn’t normally really compromise anything on your Computer – for that reason, this kind of a virus quite often does not activate security notifications from the user’s anti-virus software tool. A virus program such as Bozon3 is not designed to modify or corrupt the files, to format your hard-drives, or harm system files – such malware can only make encryption-locked copies of the files it is after, and remove the original ones in order to ensure that you may not use your files before executing the money payment. As the procedure of encoding is actually a file-protection technique, the security program you use could not discover it. As soon as this process is performed, the victim usually gets a notification informing them about the completed file encryption procedure. The notification is there to tell the victim how to pay the ransom.
SUMMARY:
| Name | Bozon3 |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove Bozon3 Ransomware

The successful removal of Bozon3 requires thorough preparation and an in-depth grasp of the removal process. As a result, the first thing you should do is to save this page with removal instructions as a bookmark for later reference. In addition to that, you need to restart the infected machine in Safe Mode, instructions for which can be found in the link provided here. Once this step has been completed, proceed with the removal of Bozon3 as described below.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
Once Bozon3 has infected a computer, it tends to remain undetected by the user since it hides in the system’s background. For this reason, you need to open your Task Manager (CTRL + SHIFT + ESC) and inspect the Processes tab for any suspicious processes that may be linked to ransomware activity. These processes may consume a significant amount of CPU or Memory, have odd names, or have no connection to any of the software installed on your computer.
To check a suspicious process, highlight it and right-click on it. Next, select Open File Location as described below:

In this location, you’ll find all the files related to the process you’ve selected. To be on the safe side, do an antivirus scan on these files. If you don’t have access to a reliable anti-virus program, you can use the free online virus scanner provided below.

If any malicious files are found during the scan, right-click on the process and select End Process to stop it from running. Next, the File Location folder should also be cleaned of any potentially harmful files.

Next, you should look for any possibly dangerous modifications in your system’s Hosts file. You can access that file by pressing Windows key + R, and then pasting the line below in the Run box and pressing Enter:
notepad %windir%/system32/Drivers/etc/hosts
Look for strange IP addresses under “Localhost” and post them in the comments section if you find them disturbing. If we discover something suspicious about them, we’ll let you know.

If everything is normal in your Hosts file, close it and go to the Windows Search field. Type msconfig, then hit Enter.

Select Startup at the top, and look for startup items that aren’t part of the default set of apps that start with your computer. Investigate any “unknown” or strangely named items online before disabling them. Uncheck the boxes next to any items you don’t want to start up with your system and click OK.

A ransomware threat like Bozon3 may infiltrate the system’s registry without being detected and create dangerous registry entries. It is possible that if these entries are not removed, the malware will be able to remain on the system. Because of this, finding them is critical to eliminating the ransomware successfully from the machine. There is a manual process you can follow if you’re not sure how to do it.
Warning! Deleting important registry data and programs raises the risk of OS corruption. Therefore, security professional recommend using malware removal software on your computer for removing dangerous files from critical system locations such as the registry.
To make changes to the Registry, type regedit in the Windows Search field and press Enter to launch the Registry Editor.
After that, open the Editor’s Find window (by pressing CTRL and F) and type the name of the malware you’re looking for. Then use the Find Next button to look for files with that name. In order to deal with Bozon3, it is necessary to remove all registry entries that include references to it.
To avoid any risk, we advise our readers to use the powerful malware removal program linked on this page to remove dangerous entries from their operating system, rather than doing this manually.
There are five more system locations to search for traces of Bozon3 after you’ve cleaned out the registry. Just copy and paste each of them exactly as they are written in the Windows search field and press Enter to open them:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Any newly added Bozon3-related files should best be removed from these locations, especially if they have been added around the time of the attack. All files in Temp should be deleted, so any temporary files linked to the infection can be removed as well.

How to Decrypt Bozon3 files
Ransomware threats such as Bozon3 are extremely worrisome since even if the infection is removed, the victims will still need to find a way to decrypt their files. This free file recovery guide can help you learn about the latest file recovery solutions and best practices for minimizing the negative effects of Bozon3’s attack.
Before you use it, however, make sure that Bozon3 has been totally removed from the system. The free online virus scanner or the anti-virus software mentioned on this page will help you scan your computer for hidden malware. If you find yourself in trouble, let us know if there’s anything we can do for you by posting a question in the comments section below.

Leave a Comment