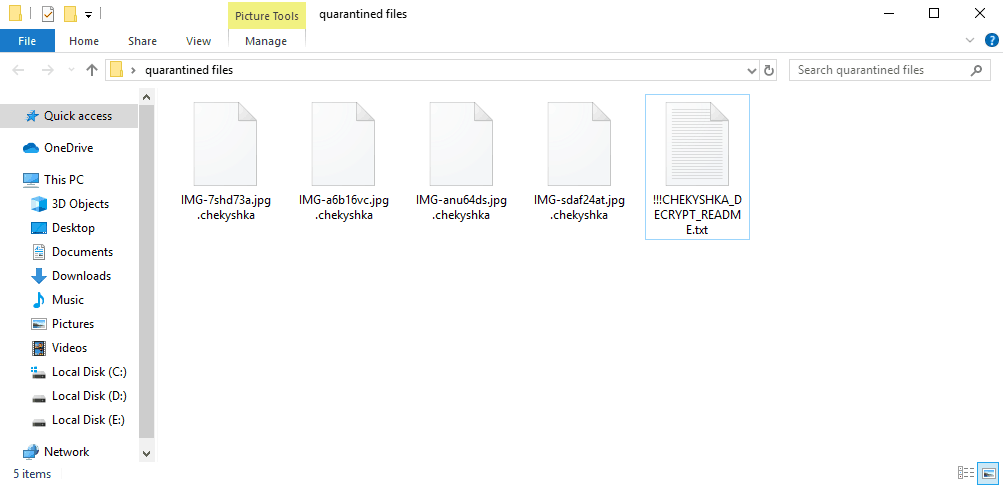
This page aims to help you remove Chekyshka Ransomware for free. Our instructions also cover how any .chekyshka file can be recovered.
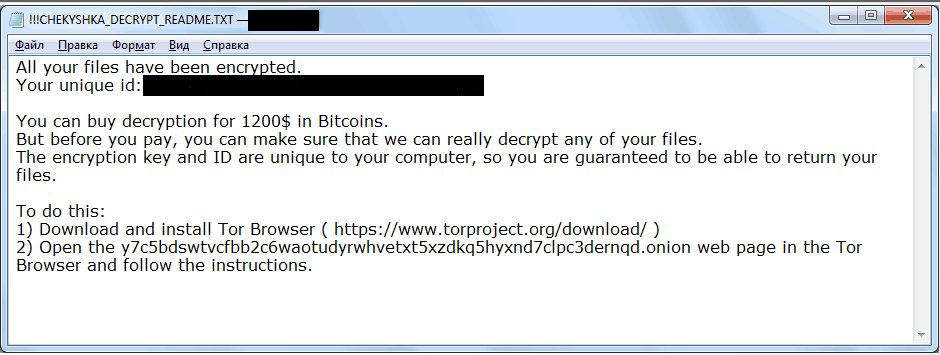
Once the encryption has finished you will find a !!!CHEKYSHKA_DECRYPT_README.txt file with the instructions for paying the ransom.
The Ransomware cryptoviruses are famous for their covert methods of operation and for their lack of symptoms. This makes them some of the most effective forms of malware that you can encounter and, unsurprisingly, the number of users who have their computer infected by such malware is always uncomfortably high. Throughout the past decade, the hackers behind the Ransomware infections such as .Litar and .Docm have really stepped up their game and have managed to infect millions of computers all over the world, extorting huge amounts of money from their victims. And, in the recent months, the number of Ransomware cryptovirus infections has increased dramatically. Each day several new viruses of this category get made and get released on the Internet to seek their latest victims. Chekyshka Ransomware is one such malware program of the cryptovirus category with the ability to encrypt the data of its victims and then threaten to destroy the decryption key – supposedly the only thing that can unlock the data – if the users do no comply with the demands of the hackers behind this infection. Of course, what those demands comprise is the payment of a ransom. Depending on who or what the victim is, the amount of money that is demanded may vary from several hundreds to several thousands of dollars (usually requested in BitCoin). For instance, if you are a regular user, you may be asked to pay couple of hundreds of dollars but if you are the head of a big company or some other organization with lots of resources, you will likely be blackmailed to pay much more. Some of the most aggressive Ransomware threats have even been report to attack the networks of schools, hospitals and governments, and since the data kept on the computers of these networks is so important and critical, more often than not, a payment is made to appease the criminal hackers. However, paying the ransom is not something that we would recommend if you are currently being blackmailed by Chekyshka and here’s why:
Why paying the ransom can have very unpleasant consequences
In fact, the reason why we advise against the payment is rather simple, and that reason is the fact that you may simply spend the money without getting your files restored. Remember that the hackers aren’t concerned with whether or not you actually regain the access to your files. All they are after is the money they want from you, and, as soon as they receive it, there’s nothing stopping them from vanishing without sending you a decryption key. And, in case this is what happens, there is nothing you can do to trace them and/or bring them to justice.
Sadly, although there is an alternative solution, it also doesn’t guarantee that everything will be back to normal with your files. Still, what we would advise you to do instead of paying the ransom is to remove the malware with the help of the Chekyshka Ransomware removal guide below and then try the data-recovery methods we have suggested in our site as an alternative means of bringing back your data.
SUMMARY:
| Name | Chekyshka |
| Type | Ransomware |
| Detection Tool |
Remove Chekyshka Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment