Cl0p
Cl0p is a ransomware cryptovirus that specializes in the encryption of user data. Cl0p can target most popular files types such as images, videos, audio files, databases, text documents, etc.
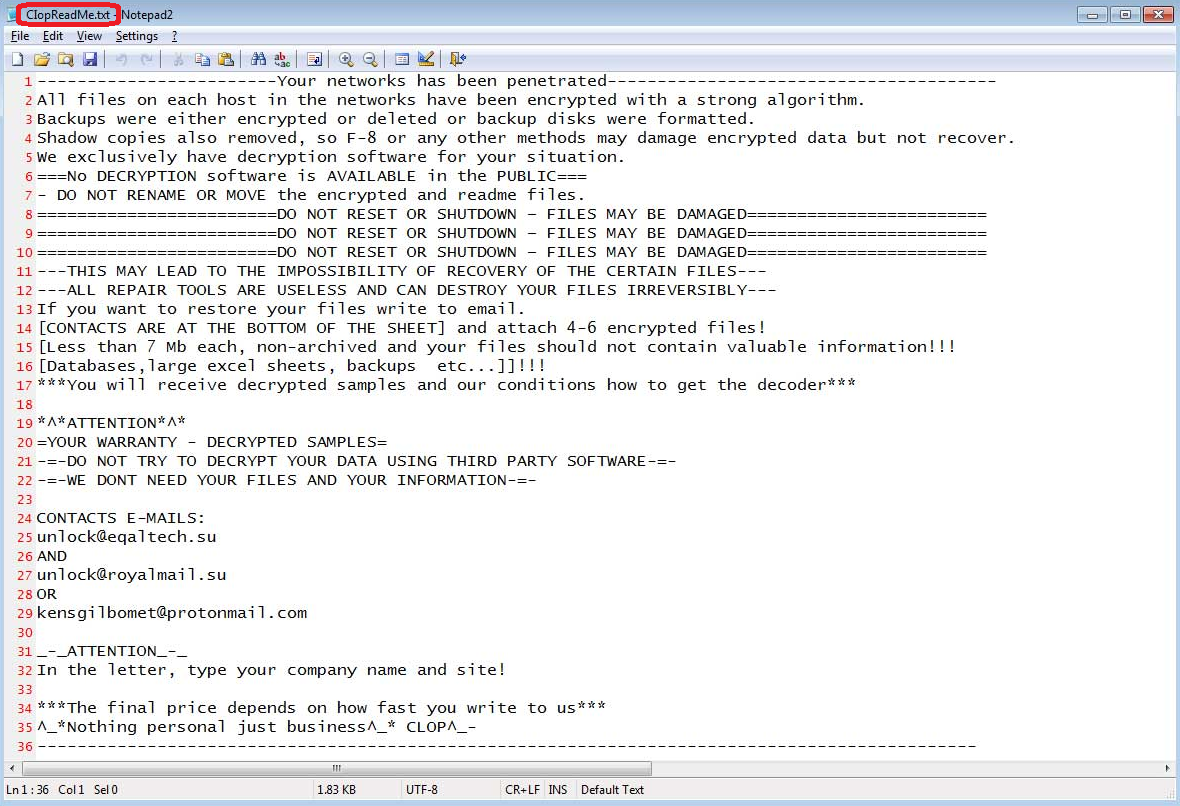
The Cl0p Ransomware will display this message in a .txt file.
Once in your system, Cl0p gets to work immediately and begins to scan your disks and drives for all the file types it’s after. Then, once it has a complete list of files, it will begin to create encrypted copies of each of them, one by one. Simultaneously, the ransomware variant will also delete the original files. So as a result, the victim user will be left with a whole bunch of encrypted copies of their original data and no possibility to access them in any way.
This is typical ransomware behavior but it doesn’t end there. Once the encryption process is over, the virus will usually generate some type of message on your screen. Whether it’s in a Notepad file or it’s some form of on-screen banner, Cl0p will make its presence known to you and will inform you of the fact that it has made a lion’s share of your information unusable to you. After this, it will also “kindly” offer you a way out of this rather sticky situation in exchange for a hefty sum of money (typically also requested in Bitcoin or other cryptocurrencies). The solution offered is a decryption key that only the hackers behind the virus are in possession of. And after you’ve received and applied it, you are theoretically supposed to be able to open your files again.
And while that may all sound good on paper, the reality of the matter is that there are many things that can go utterly wrong in this situation. And in a nutshell, you could easily end up spending your money for nothing. Instead, we would encourage you to remove Cl0p manually with the help of the removal guide below. And then have a look at the alternative file-recovery options we’ve listed in the second part of the guide.
The Cl0p Ransomware
The Cl0p ransomware belongs to one of the most rapidly growing malware categories due to how lucrative it is. And one of the main factors on the side of the Cl0p ransomware is its stealth and ability to bypass popular security software.
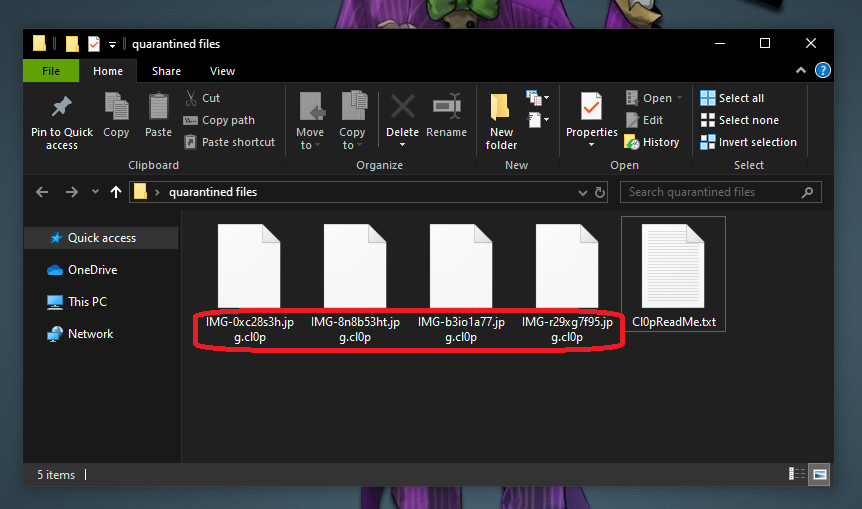
Once Cl0p has infected you it will start encrypting your files.
Ransomware viruses are actually well known for their ability to work under the radar of most antivirus systems. And this is because the encryption process itself doesn’t harm the files it is applied to, hence it doesn’t trigger a defense response. And sophisticated ransomware variants are even capable of disabling the antivirus program on a given computer. So that is certainly one advantage that ransomware has that users must be aware of in order to take adequate precautions against such attacks. And one major such precaution is regularly backing up your important files and storing copies on a separate hard drive that doesn’t have access to the internet.
The Cl0p file extension
The Cl0p file extension replaces that of the files it encrypts. Thus, the Cl0p file extension prevents any software from reading their file format.
SUMMARY:
| Name | Cl0p |
| Type | Ransomware |
| Detection Tool |
Cl0p Virus Removal
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment